BOOK THIS SPACE FOR AD
ARTICLE AD
Hello Folks 👋,I have found a good open redirect with my param scanner. I will tell you here how I found it and what kind of swag I got. I am also currently modifying my scanner, PSFuzz, so that it can also scan OpenRedirects and will then improve it over time. https://github.com/Proviesec/PSFuzz
And here is my story:
I was invited to a new private BugBounty programme and thought, well, I’ll look for the easy stuff first. Since I use Burp, I record my history with all redirects and links, which makes searching for bugs easier. After investigating a few simple security holes, I actually wanted to try to find some XSS stuff. I also like to use Google Dorks, for example I used
site:*redacted.com inurl:targetand had a result, so I looked to see if it was suitable for an open redirect.
Behind the google result was the login page of the website. And I always love to test these. And this time I noticed that the parameter target contained a whole URL, which was very tempting to test.The url looks like this: https://my.redacted.com/forgetUsername?target=https:%2F%2Fwww.redacted.com
Therefore, you could already see that the link no longer jumps to the “my” subdomain but to the “www” subdomain.So I tested it out and replaced the URL: https://my.redacted.com/forgetUsername?target=https:%2F%2Fwww.hackerone.comNow you just have to click submit or cancel and you will be redirected.

As, you can see it redirects to that website when you inject this payload: target=https:%2F%2Fwww.hackerone.com -> www.hackerone.com
So I quickly found a good open redirect.

What is a open redirect?
When a web application or server redirects a user to a specific website or page using a link submitted by an unauthenticated user, this is called an open redirect.
Impact
An open redirection vulnerability occurs when an application unsafely injects user-controllable data into a redirection target. An attacker can construct a URL in the application that causes redirection to any external domain. This behavior can be used to facilitate phishing attacks against application users. The ability to use the real application URL, locate the correct domain, and a valid SSL certificate (if using SSL) lends credibility to phishing attacks, as many users, even if they verified these characteristics, they wouldn’t notice subsequent redirects to a different domain.
Timeline:
Submitted: 18 May, 2021
Accepted: 18 May, 2021
Triaged: 19 May, 2021
Resolved: 20 May, 2021
Closed + rewarded with a swag: 03 Jun, 2021
![]()
I had already stopped believing in swag, but after 6 months I received a package and it was from the company I sent this report to. Since this is a private programme and the company’s logo was all over it, I will describe the swag to you. I received an item of clothing, a BugBounty coin and a hiking utensil. All in the total value of 60 dollars. The box was beautifully packaged and I was very happy about it.
How can you find a openredirect?
Google Dorks for Openredirect:
https://github.com/Proviesec/google-dorks/blob/main/google-dorks-open-redirect.txt
Openredirect Payloads:
Other Tools:
https://github.com/payloadbox/open-redirect-payload-list
https://portswigger.net/support/using-burp-to-test-for-open-redirections
Also look for OpenRedirects on websites. Such bugs can also earn you a bounty, are often overlooked and can also have consequences for a company.
An open redirect does not always equal a security breach, sometimes they are intentional so it is harder to get a bounty with it. Feel free to watch this video about it: https://www.youtube.com/watch?v=tE47rd2sf3M
Please feel free to ask me and suggest any changes that I should consider next time. Thank you for reading anyway.👋
.png)
 1 year ago
115
1 year ago
115 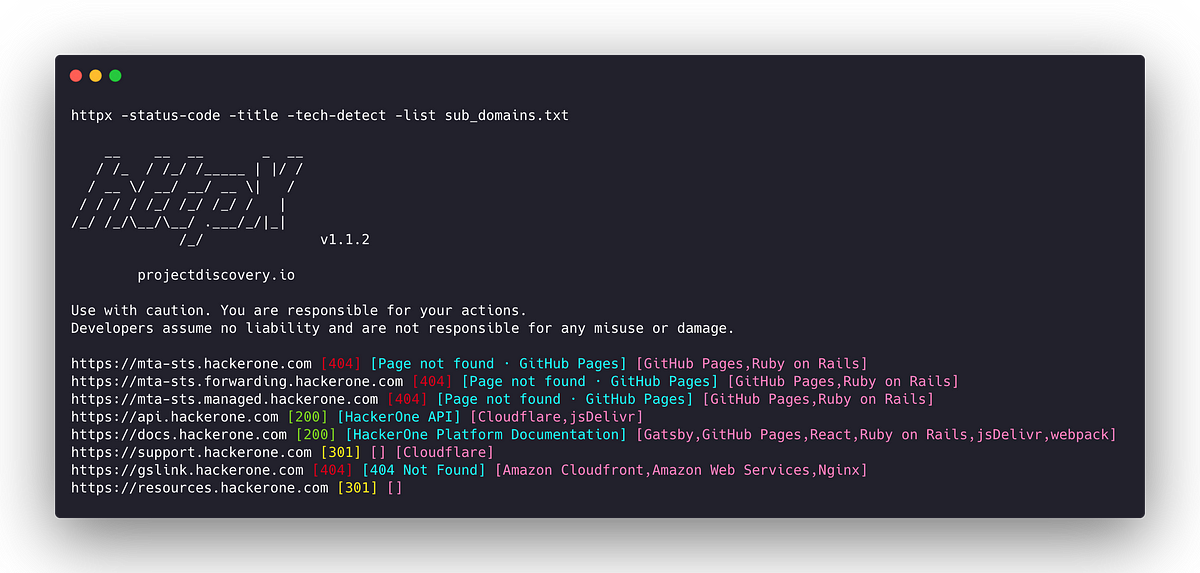













 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·