A week after it emerged that sophisticated mobile spyware dubbed Hermit was used by the government of Kazakhstan within its borders, Google said it has notified Android users of infected devices.
Additionally, necessary changes have been implemented in Google Play Protect — Android's built-in malware defense service — to protect all users, Benoit Sevens and Clement Lecigne of Google Threat Analysis Group (TAG) said in a Thursday report.
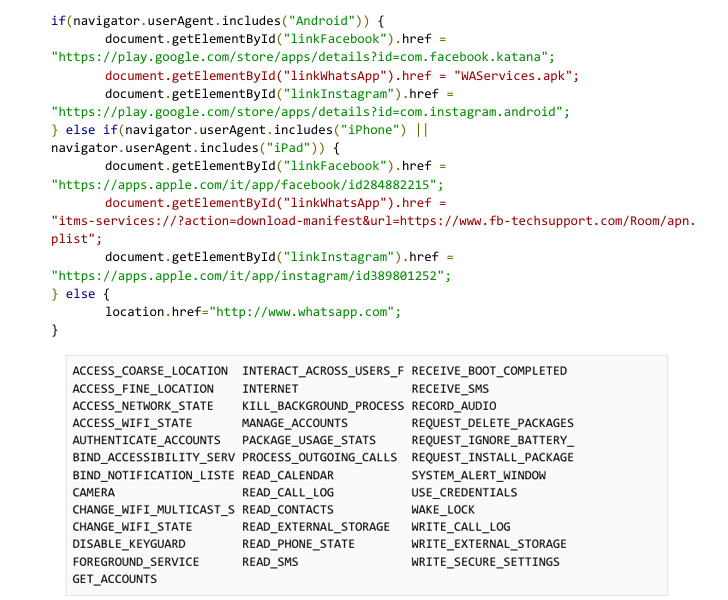
Hermit, the work of an Italian vendor named RCS Lab, was documented by Lookout last week, calling out its modular feature-set and its abilities to harvest sensitive information such as call logs, contacts, photos, precise location, and SMS messages.
Once the threat has thoroughly insinuated itself into a device, it's also equipped to record audio and make and redirect phone calls, in addition to abusing its permissions to accessibility services to keep tabs on the foreground apps used by the victims.
Its modularity also enables it to be wholly customizable, equipping the spyware's functionality to be extended or altered at will. It's not immediately clear who were targeted in the campaign, or which of RCS Lab clients were involved.
The Milan-based company, operating since 1993, claims to provide "law enforcement agencies worldwide with cutting-edge technological solutions and technical support in the field of lawful interception for more than twenty years." More than 10,000 intercepted targets are purported to be handled daily in Europe alone.
"Hermit is yet another example of a digital weapon being used to target civilians and their mobile devices, and the data collected by the malicious parties involved will surely be invaluable," Richard Melick, director of threat reporting for Zimperium, said.
The targets have their phones infected with the spy tool via drive-by downloads as initial infection vectors, which, in turn, entails sending a unique link in an SMS message that, upon clicking, activates the attack chain.
It's suspected that the actors worked in collaboration with the targets' internet service providers (ISPs) to disable their mobile data connectivity, followed by sending an SMS that urged the recipients to install an application to restore mobile data access.
"We believe this is the reason why most of the applications masqueraded as mobile carrier applications," the researchers said. "When ISP involvement is not possible, applications are masqueraded as messaging applications."
To compromise iOS users, the adversary is said to have relied on provisioning profiles that allow fake carrier-branded apps to be sideloaded onto the devices without the need for them to be available on the App Store.
An analysis of the iOS version of the app shows that it leverages as many as six exploits — CVE-2018-4344, CVE-2019-8605, CVE-2020-3837, CVE-2020-9907, CVE-2021-30883, and CVE-2021-30983 — to exfiltrate files of interest, such as the WhatsApp database, from the device.
"As the curve slowly shifts towards memory corruption exploitation getting more expensive, attackers are likely shifting too," Google Project Zero's Ian Beer said in a deep-dive analysis of an iOS artifact that impersonated the My Vodafone carrier app.
On Android, the drive-by attacks require that victims enable a setting to install third-party applications from unknown sources, doing so which results in the rogue app, masquerading as smartphone brands like Samsung, requests for extensive permissions to achieve its malicious goals.
The Android variant, besides attempting to root the device for entrenched access, is also wired differently in that instead of bundling exploits in the APK file, it contains functionality that permits it to fetch and execute arbitrary remote components that can communicate with the main app.
"This campaign is a good reminder that attackers do not always use exploits to achieve the permissions they need," the researchers noted. "Basic infection vectors and drive by downloads still work and can be very efficient with the help from local ISPs."
Stating that seven of the nine zero-day exploits it discovered in 2021 were developed by commercial providers and sold to and used by government-backed actors, the tech behemoth said it's tracking more than 30 vendors with varying levels of sophistication who are known to trade exploits and surveillance capabilities.
What's more, Google TAG raised concerns that vendors like RCS Lab are "stockpiling zero-day vulnerabilities in secret" and cautioned that this poses severe risks considering a number of spyware vendors have been compromised over the past ten years, "raising the specter that their stockpiles can be released publicly without warning."
"Our findings underscore the extent to which commercial surveillance vendors have proliferated capabilities historically only used by governments with the technical expertise to develop and operationalize exploits," TAG said.
"While use of surveillance technologies may be legal under national or international laws, they are often found to be used by governments for purposes antithetical to democratic values: targeting dissidents, journalists, human rights workers and opposition party politicians."
Found this article interesting? Follow THN on Facebook, Twitter and LinkedIn to read more exclusive content we post.
.png)
 2 years ago
146
2 years ago
146 
















 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·