BOOK THIS SPACE FOR AD
ARTICLE AD
For the last two years the absolute worst, most prolific, most globally significant “big game” ransomware gang has been LockBit.
This evening its position as ransomware’s biggest beast is suddenly in doubt, following some non-consensual website redecoration at the hands of the UK’s National Crime Agency (NCA).
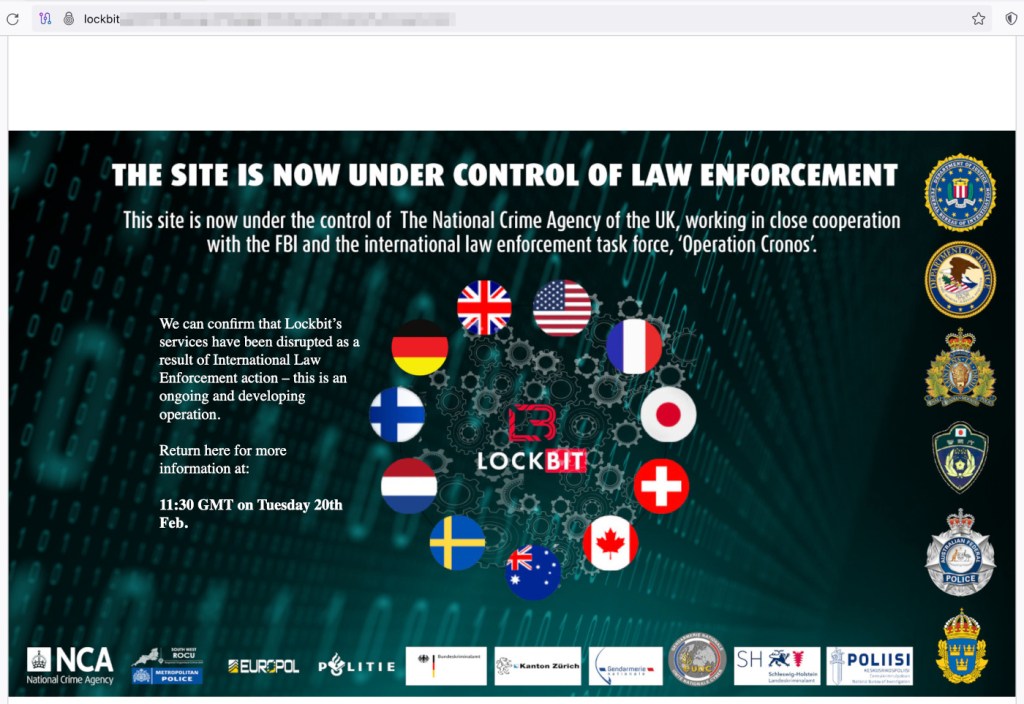 The LockBit data leak site has a new look
The LockBit data leak site has a new look
The LockBit dark web site usually hosts the names and data of organisations that refused to pay ransoms. That’s been replaced by a message from the NCA, saying:
This site is now under the control of The National Crime Agency of the UK, working in close cooperation with the FBI and the international law enforcement task force, ‘Operation Cronos’.
Repleat with the flags and badges of the countries and agencies involved, the new look site promises there is more to come. “We can confirm that Lockbit’s services have been disrupted as a result of International Law Enforcement action – this is an ongoing and developing operation. Return here for more information at: 11:30 GMT on Tuesday 20th Feb.
Since the demise of Conti in 2022, LockBit has been unchallenged as the most prolific ransomware group in the world. In the last 12 months it has racked up more than two and half times as many known attacks as ALPHV, its closest rival.
 Top 5 ransomware gangs by known attacks, February 2023 – January 2024
Top 5 ransomware gangs by known attacks, February 2023 – January 2024
At this stage we have no idea how serious the damage to LockBit is, and law enforcement is only claiming that the group has been “disrupted”. However, even if that disruption isn’t fatal, it will doubtless raise serious questions among LockBit’s criminal associates.
LockBit sells ransomware-as-a-service (RaaS) to “affiliates”, criminal gangs who use the service to carry out ransomware attacks. Even if LockBit can rebuild its infrastructure elsewhere those affiliates now have every reason to question its credibility.
The takedown comes just two months after LockBit’s biggest rival, ALPHV, also suffered a serious mauling at the hands of international law enforcement, before staggering back to its feet.
How to avoid ransomware
Block common forms of entry. Create a plan for patching vulnerabilities in internet-facing systems quickly; and disable or harden remote access like RDP and VPNs. Prevent intrusions. Stop threats early before they can even infiltrate or infect your endpoints. Use endpoint security software that can prevent exploits and malware used to deliver ransomware. Detect intrusions. Make it harder for intruders to operate inside your organization by segmenting networks and assigning access rights prudently. Use EDR or MDR to detect unusual activity before an attack occurs. Stop malicious encryption. Deploy Endpoint Detection and Response software like ThreatDown EDR that uses multiple different detection techniques to identify ransomware, and ransomware rollback to restore damaged system files. Create offsite, offline backups. Keep backups offsite and offline, beyond the reach of attackers. Test them regularly to make sure you can restore essential business functions swiftly. Don’t get attacked twice. Once you’ve isolated the outbreak and stopped the first attack, you must remove every trace of the attackers, their malware, their tools, and their methods of entry, to avoid being attacked again.You can learn more about the threat of big game ransomware like LockBit and ALPHV in our 2024 State of Malware report.
.png)














 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·