The infamous Lazarus Group actor has been targeting vulnerable versions of Microsoft Internet Information Services (IIS) servers as an initial breach route to deploy malware on targeted systems.
The findings come from the AhnLab Security Emergency response Center (ASEC), which detailed the advanced persistent threat's (APT) continued abuse of DLL side-loading techniques to deploy malware.
"The threat actor places a malicious DLL (msvcr100.dll) in the same folder path as a normal application (Wordconv.exe) via the Windows IIS web server process, w3wp.exe," ASEC explained. "They then execute the normal application to initiate the execution of the malicious DLL."
DLL side-loading, similar to DLL search-order hijacking, refers to the proxy execution of a rogue DLL via a benign binary planted in the same directory.
Lazarus, a highly-capable and relentless nation-state group linked to North Korea, was most recently spotted leveraging the same technique in connection with the cascading supply chain attack on enterprise communications service provider 3CX.
The malicious msvcr100.dll library, for its part, is designed to decrypt an encoded payload that's then executed in memory. The malware is said to be a variant of a similar artifact that was discovered by ASEC last year and which acted as a backdoor to communicate with an actor-controlled server.
The attack chain further entailed the exploitation of a discontinued open source Notepad++ plugin called Quick Color Picker to deliver additional malware in order to facilitate credential theft and lateral movement.
The latest development demonstrates the diversity of Lazarus attacks and its ability to employ an extensive set of tools against victims to carry out long-term espionage operations.
"In particular, since the threat group primarily utilizes the DLL side-loading technique during their initial infiltrations, companies should proactively monitor abnormal process execution relationships and take preemptive measures to prevent the threat group from carrying out activities such as information exfiltration and lateral movement," ASEC said.
U.S. Treasury Sanctions North Korean Entities
The findings also come as the U.S. Treasury Department sanctioned four entities and one individual involved in malicious cyber activities and fundraising schemes that aim to support North Korea's strategic priorities.
UPCOMING WEBINAR
Zero Trust + Deception: Learn How to Outsmart Attackers!
Discover how Deception can detect advanced threats, stop lateral movement, and enhance your Zero Trust strategy. Join our insightful webinar!
This includes the Pyongyang University of Automation, the Technical Reconnaissance Bureau and its subordinate cyber unit, the 110th Research Center, Chinyong Information Technology Cooperation Company, and a North Korean national named Kim Sang Man.
The Lazarus Group and its various clusters are believed to be operated by the Technical Reconnaissance Bureau, which oversees North Korea's development of offensive cyber tactics and tools.
The sanctions-hit nation, besides engaging in crypto currency theft and espionage operations, is known to generate illicit revenue from a workforce of skilled IT workers who pose under fictitious identities to obtain jobs in the technology and virtual currency sectors across the world.
"The DPRK conducts malicious cyber activities and deploys information technology (IT) workers who fraudulently obtain employment to generate revenue, including in virtual currency, to support the Kim regime and its priorities, such as its unlawful weapons of mass destruction and ballistic missile programs," the department said.
"These workers deliberately obfuscate their identities, locations, and nationalities, typically using fake personas, proxy accounts, stolen identities, and falsified or forged documentation to apply for jobs at these companies."
"They earn hundreds of millions of dollars a year by engaging in a wide range of IT development work, including freelance work platforms (websites/applications) and cryptocurrency development, after obtaining freelance employment contracts from companies around the world," the South Korean government warned in December 2022.
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.
.png)
 1 year ago
152
1 year ago
152 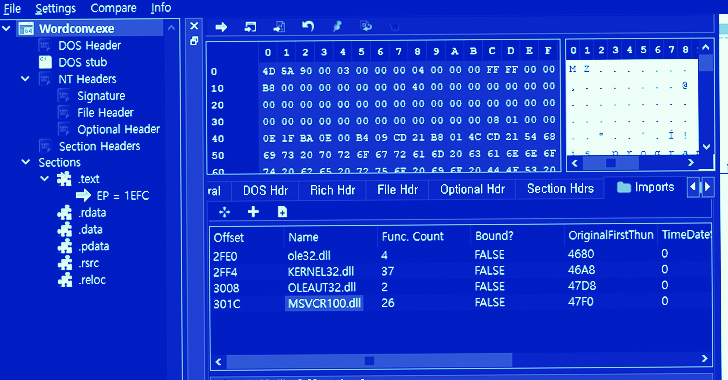















 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·