BOOK THIS SPACE FOR AD
ARTICLE ADLinux Users Beware: “Spinning YARN” Malware Campaign Targets Misconfigured Servers Running on Apache Hadoop YARN, Docker, Confluence and Redis.
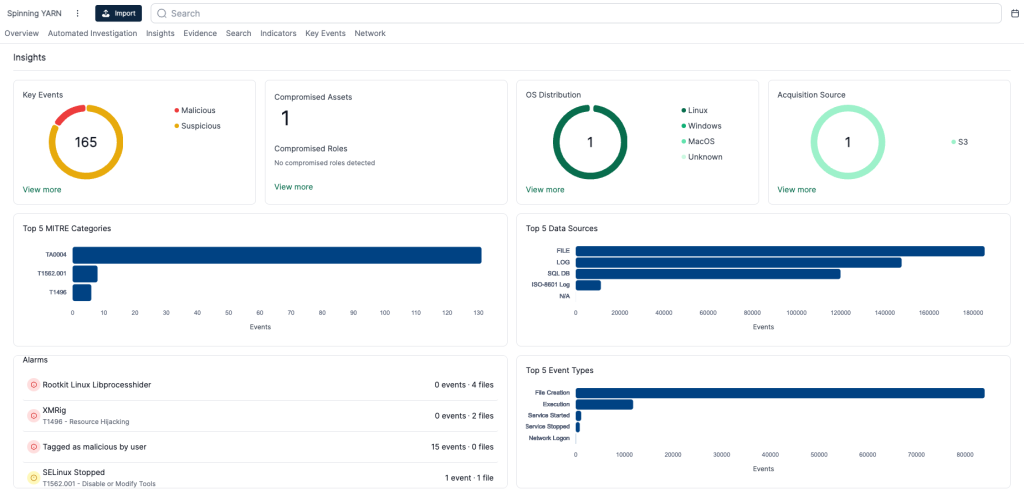
Cado Security Labs has discovered an emerging Linux malware campaign dubbed Spinning Yarn targeting misconfigured servers running Apache Hadoop YARN, Docker, Confluence, and Redis web-facing services.
The emergence of the new Linux malware shouldn’t come as a surprise, given the recent surge in threats targeting Linux devices and servers. Just a couple of days ago, an old Linux malware known as Bifrost RAT resurfaced with a new variant that mimics VMware domains.
According to Cado Security’s research research shared with Hackread.com ahead of publication on Wednesday, Spinning Yarn is a malicious campaign that exploits weaknesses in popular Linux software used by businesses across various sectors.
These services are crucial components in organizations’ IT infrastructure. Docker is critical for developing, deploying, and managing containerized applications. Apache Hadoop allows distributed processing of large datasets. Redis, a widely used in-memory data store, helps in caching real-time applications, and Confluence allows collaboration and knowledge management.
By compromising these applications, attackers can gain unauthorized access to systems, steal sensitive data, disrupt operations, or deploy ransomware, posing a significant threat to servers and critical infrastructure.
In Spinning Yarn, threat actors have used several unique payloads, including four Golang binaries that automate the discovery and infection of hosts and let them exploit code. They use Confluence to exploit common misconfigurations and vulnerabilities, launching Remote Code Execution (RCE) attacks and infecting new hosts.
The attackers exploit CVE-2022-26134, an n-day vulnerability in Confluence, and deploy a container for the Docker compromise. The vulnerability has been exploited since 2022, including by Mirai malware variant V3G4 against IoT devices for DDoS attacks
Further probing revealed a series of shell scripts and standard Linux attack techniques used to deliver a cryptocurrency miner, spawn a reverse shell, and enable persistent access to compromised hosts. They also deploy an instance of the Platypus open-source reverse shell utility to maintain access.
In an attempt to evade detection, multiple user-mode rootkits are deployed. Researchers observed that the shell script payloads employed in this campaign share similarities with those used in previous cloud attacks.
In their blog post, Cado Security Labs detailed initial access activity on a docker Engine API honeypot on this IP address: 47966971. The attacker spawned a new container using Alpine Linux and created a bind mount for the underlying server’s root directory. This technique is common in Docker attacks, allowing attackers to write files to the host and execute a job for the Cron scheduler eventually achieving RCE.
In this campaign, the attacker wrote an executable and registered a Cron job to execute base64-encoded shell commands. Such extensive attack on Linux applications demonstrates attackers’ growing sophistication in targeting web-facing services in cloud environments, keeping abreast of vulnerabilities.
To mitigate the risks from campaigns like Spinning Yarn, regularly update software, enable strong passwords, educate employees on cybersecurity best practices, segment your network to limit potential damage, and deploy security solutions like endpoint security solutions and firewalls to detect and prevent malware infections. This will help protect against known vulnerabilities and ensure a secure environment.
.png)
















 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·