Cybersecurity researchers have taken the wraps off a new and entirely undetected Linux threat dubbed OrBit, signally a growing trend of malware attacks geared towards the popular operating system.
The malware gets its name from one of the filenames that's utilized to temporarily store the output of executed commands ("/tmp/.orbit"), according to cybersecurity firm Intezer.
"It can be installed either with persistence capabilities or as a volatile implant," security researcher Nicole Fishbein said. "The malware implements advanced evasion techniques and gains persistence on the machine by hooking key functions, provides the threat actors with remote access capabilities over SSH, harvests credentials, and logs TTY commands."
OrBit is the fourth Linux malware to have come to light in a short span of three months after BPFDoor, Symbiote, and Syslogk.
The malware also functions a lot like Symbiote in that it's designed to infect all of the running processes on the compromised machines. But unlike the latter which leverages the LD_PRELOAD environment variable to load the shared object, OrBit employs two different methods.
"The first way is by adding the shared object to the configuration file that is used by the loader," Fishbein explained. "The second way is by patching the binary of the loader itself so it will load the malicious shared object."
The attack chain commences with an ELF dropper file that's responsible for extracting the payload ("libdl.so") and adding it to the shared libraries that are being loaded by the dynamic linker.
The rogue shared library is engineered to hook functions from three libraries — libc, libcap, and Pluggable Authentication Module (PAM) — causing existing and new processes to use the modified functions, essentially permitting it to harvest credentials, hide network activity, and set up remote access to the host over SSH, all the while staying under the radar.
Furthermore, OrBit relies on a barrage of methods that allows it to function without alerting its presence and establish persistence in a manner that makes it difficult to remove from the infected machines.
Once engaged, the backdoor's ultimate goal is to steal information by hooking the read and write functions to capture data that's being written by the executed processes on the machine, including bash and sh commands, the results of which are stored in specific files.
"What makes this malware especially interesting is the almost hermetic hooking of libraries on the victim machine, that allows the malware to gain persistence and evade detection while stealing information and setting SSH backdoor," Fishbein said.
"Threats that target Linux continue to evolve while successfully staying under the radar of security tools, now OrBit is one more example of how evasive and persistent new malware can be."
Found this article interesting? Follow THN on Facebook, Twitter and LinkedIn to read more exclusive content we post.
.png)
 2 years ago
179
2 years ago
179 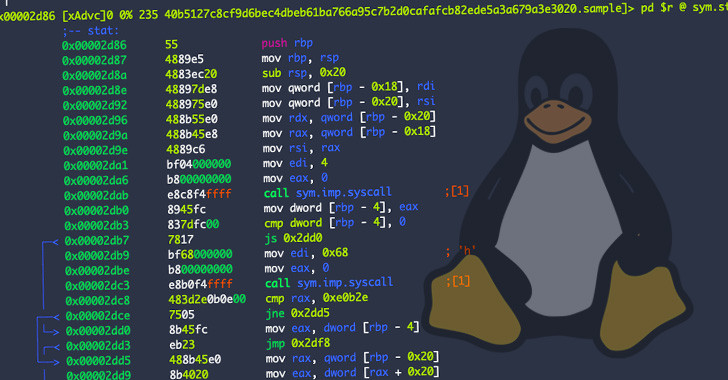
















 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·