Multiple cybercriminal groups are leveraging a malware-as-a-service (MaaS) solution to distribute a wide range of malicious software distribution campaigns that result in the deployment of payloads such as Campo Loader, Hancitor, IcedID, QBot, Buer Loader, and SocGholish against individuals in Belgium as well as government agencies, companies, and corporations in the U.S.
Dubbed "Prometheus TDS" (short for Traffic Direction System) and available for sale on underground platforms for $250 a month since August 2020, the service is designed to distribute malware-laced Word and Excel documents and divert users to phishing and malicious sites, according to a Group-IB report shared with The Hacker News.
More than 3,000 email addresses are said to have been singled out via malicious campaigns in which Prometheus TDS was used to send malicious emails, with banking and finance, retail, energy and mining, cybersecurity, healthcare, IT, and insurance emerging the prominent verticals targeted by the attacks.
"Prometheus TDS is an underground service that distributes malicious files and redirects visitors to phishing and malicious sites," Group-IB researchers said. "This service is made up of the Prometheus TDS administrative panel, in which an attacker configures the necessary parameters for a malicious campaign: downloading malicious files, and configuring restrictions on users' geolocation, browser version, and operating system."
The service is also known to employ third-party infected websites that are manually added by the campaign's operators and act as a middleman between the attacker's administrative panel and the user. To achieve this, a PHP file named "Prometheus.Backdoor" is uploaded to the compromised website to collect and send back data about the victim, based on which a decision is taken as to whether to send the payload to the user and/or to redirect them to the specified URL.
The attack scheme commences with an email containing a HTML file, a link to a web shell that redirects users to a specified URL, or a link to a Google Doc that's embedded with an URL that redirects users to the malicious link that when either opened or clicked leads the recipient to the infected website, which stealthily collects basic information (IP address, User-Agent, Referrer header, time zone, and language data) and then forwards this data to the Prometheus admin panel.
In the final phase, the administrative panel takes responsibility for sending a command to redirect the user to a particular URL, or to send a malware-ridden Microsoft Word or Excel document, with the user redirected to a legitimate site like DocuSign or USPS immediately after downloading the file to mask the malicious activity. Besides distributing malicious files, researchers found that Prometheus TDS is also used as a classic TDS to redirect users to specific sites, such as fake VPN websites, dubious portals selling Viagra and Cialis, and banking phishing sites.
"Prometheus TDS also redirected users to sites selling pharmaceutical products," the researchers noted. "Operators of such sites often have affiliate and partnership programs. Partners, in turn, often resort to aggressive SPAM campaigns in order to increase the earnings within the affiliate program. Analysis of the Prometheus infrastructure by Group-IB specialists revealed links that redirect users to sites relating to a Canadian pharmaceutical company."
Found this article interesting? Follow THN on Facebook, Twitter and LinkedIn to read more exclusive content we post.
.png)
 3 years ago
312
3 years ago
312 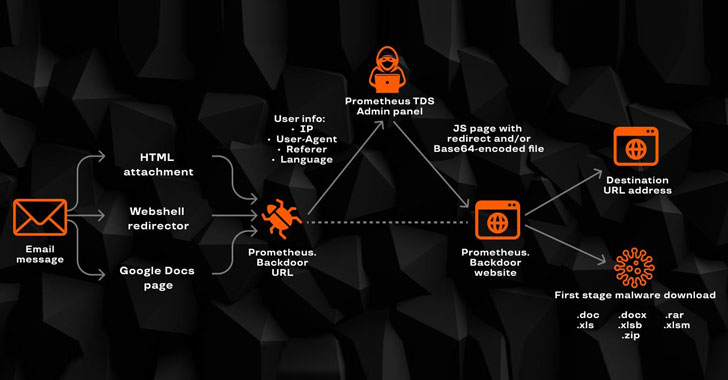

















 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·