BOOK THIS SPACE FOR AD
ARTICLE AD
Cyberespionage groups have been using ransomware as a tactic to make attack attribution more challenging, distract defenders, or for a financial reward as a secondary goal to data theft.
A joint report from SentinelLabs and Recorded Future analysts presents the case of ChamelGang, a suspected Chinese advanced persistent threat (APT) that has been using the CatB ransomware strain in attacks that impact high-profile organizations worldwide.
A separate activity cluster uses BestCrypt and Microsoft BitLocker to achieve similar goals, although attribution is not clear.
ChamelGang targeting
ChamelGang is also known as CamoFei and has targeted government organizations and critical infrastructure entities between 2021 and 2023.
The group uses sophisticated techniques to gain initial access, for reconnaissance and lateral movement, and to exfiltrate sensitive data.
In an attack in November 2022, the threat actors targeted the Presidency of Brazil and compromised 192 computers. The adversary relied on standard reconnaissance tools to map the network and to gather information on critical systems.
In the last stage of the attack, ChamelGang deployed CatB ransomware on the network, dropping ransom notes at the beginning of each encrypted file. They provided a ProtonMail address for contact and a Bitcoin address for payment.
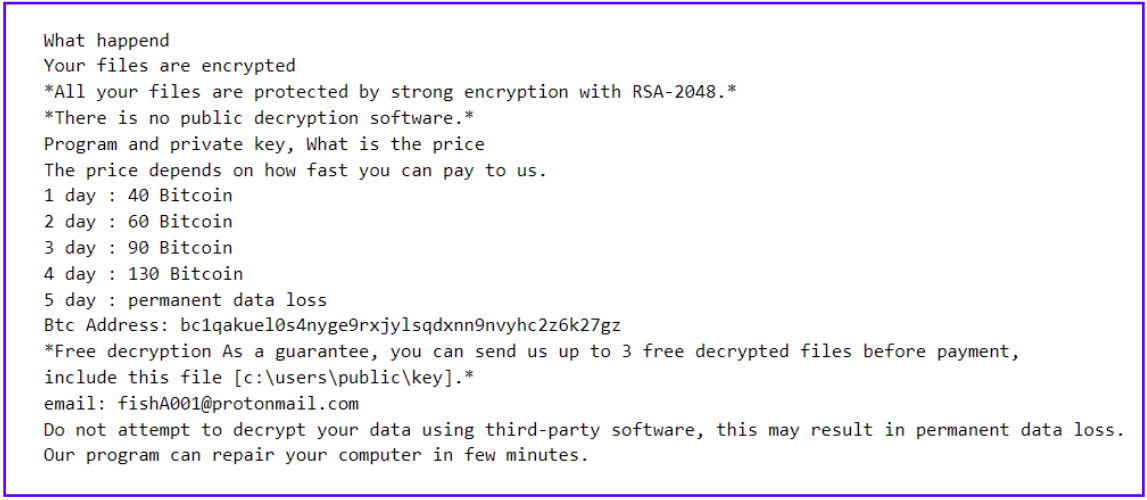 CatB ransom note
CatB ransom noteSource: SentinelLabs
The attack was initially attributed to TeslaCrypt but SentinelLabs and Recorded Future present new evidence that point to ChamelGang.
During another incident in late 2022, ChamelGang breached the All India Institute Of Medical Sciences (AIIMS) public medical research university and hospital. The threat actor used CatB ransomware once again, causing major disruptions in healthcare services.
The researchers believe that two other attacks, against a government entity in East Asia and an aviation organization in the Indian subcontinent are also the work of ChamelGang, based on the use of known TTPs, publicly available tooling seen in previous engagements, and their custom malware BeaconLoader.
BestCrypt and BitLocker
A separate cluster of activities spotted by SentinelLabs and Recorded Future encrypts files using Jetico BestCrypt and Microsoft BitLocker instead of CatB ransomware.
The researchers say that these intrusions impacted 37 organizations, most of them in North America. Other victims were in South America and Europe.
By comparing evidence in reports from other cybersecurity companies, the researchers discovered overlaps with past intrusions linked to suspected Chinese and North Korean APTs.
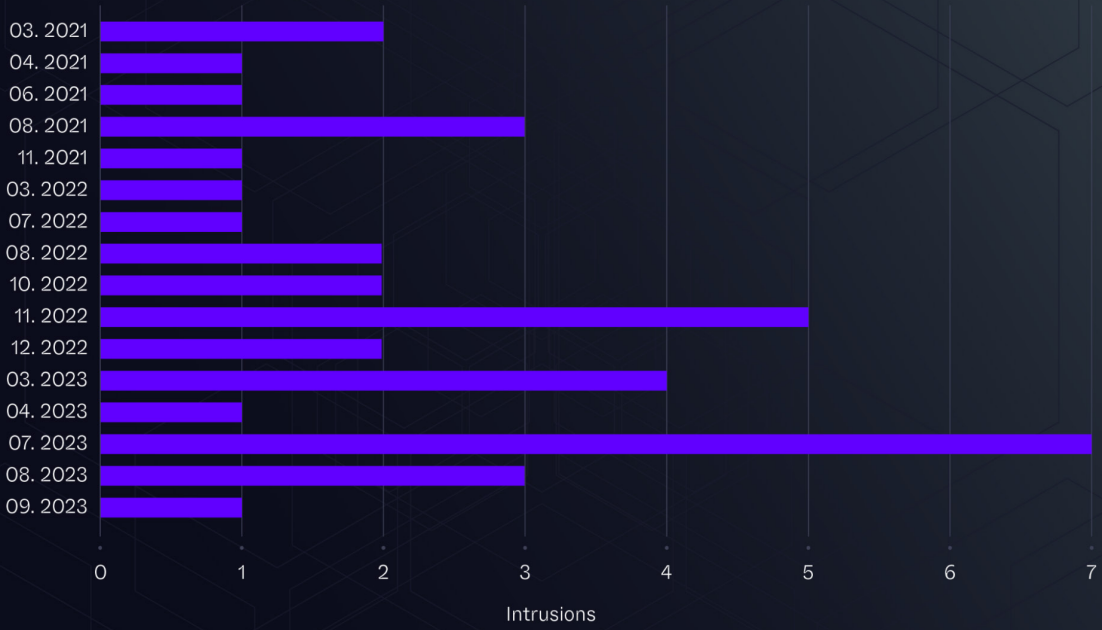 BestCrypt and BitLocker powered intrusions detected overtime
BestCrypt and BitLocker powered intrusions detected overtimeSource: SentinelLabs
Typically, BestCrypt was used to target server endpoints in an automated, serial encryption manner, while BitLocker was deployed against workstations, with unique recovery passwords used in each case.
The attackers also used the China Chopper webshell, a custom variant of the miPing tool, and leveraged Active Directory Domain Controllers (DCs) as footholds.
The analysts report these attacks lasted for nine days on average, while some had a short duration of just a couple of hours, indicating familiarity with the targeted environment.
A reason for involving ransomware in cyberespionage attacks could be that it provides strategic and operational benefits that blur the lines between APT and cybercriminal activity, which can lead to incorrect attribution or as a means to conceal the data collection nature of the operation.
Attributing past ransomware incidents to a cyberespionage threat actor as ChamelGang is new and shows that adversaries are changing tactics to cover their tracks while still attaining their goals.
.png)















 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·