BOOK THIS SPACE FOR AD
ARTICLE AD
Credential Flusher, understanding the threat and how to protect your login data
Pierluigi Paganini
September 18, 2024

Credential Flusher is a method that allows hackers to steal login credentials directly from the victim’s web browser.
The cyber attacks have become increasingly sophisticated, putting our personal information at risk. One of the latest and most insidious techniques is Credential Flusher, a method that allows hackers to steal login credentials directly from the victim’s web browser.
The following article analyzes the operation of this technique as explained by OALABS researchers, highlighting the risks and protective measures we can take:
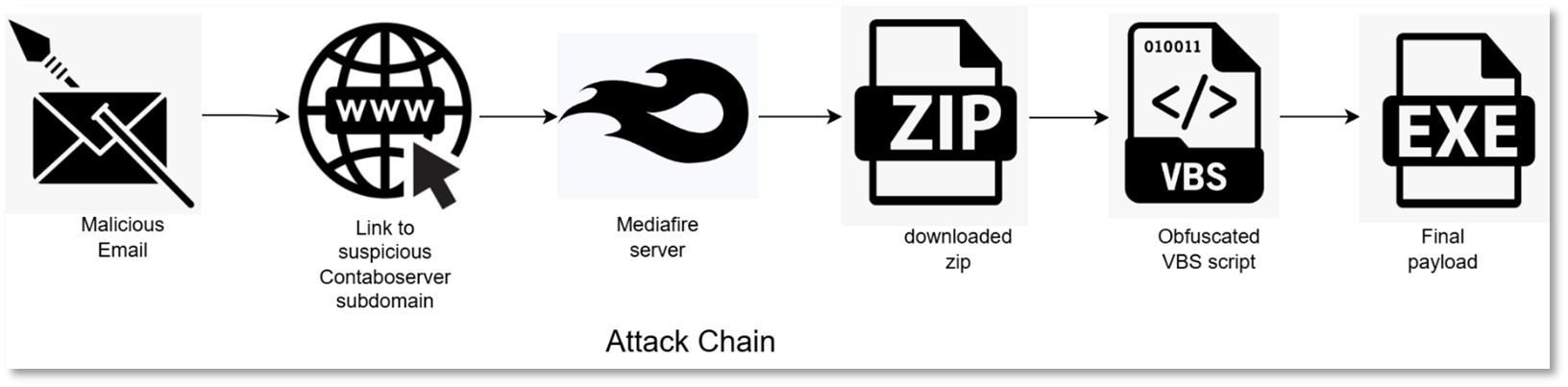
Attack flow
The Credential Flusher method uses an AutoIt script to force users to enter their credentials in a browser operating in kiosk mode. This mode limits the user’s ability to close the browser or access other applications, making it easier for hackers to obtain the desired information.
The AutoIt script does not directly steal the credentials but works in combination with other malware, such as StealC, to extract the information. The malware is distributed via the Amadey loader (https://research.openanalysis.net/cpp/stl/amadey/loader/config/2022/11/13/amadey.html ), which can be spread through phishing e-mails or downloads from compromised sites.

Flow chart – Credit OALABS
In the OALABS example, Amadey loads StealC and “AutoIt2Exe” binary (https://www.unpac.me/results/135c3dff-3159-4738-83ed-ed04cc09d3a8?hash=78f4bcd5439f72e13af6e96ac3722fee9e5373dae844da088226158c9e81a078 ) from http[:]//31.41.244[.]11 and executes them.
The AutoIt script opens the legitimate Google “Sign in” page in kiosk mode and sets a parameter to ignore the F11 and ESC keys on the victim’s browser.
Script code snippet – Credit OALABS
The attackers hope that the victim will save the password when asked by the browser, so that it will be stolen by StealC running.
Why and how to protect ourselves
Once the credentials are stolen, hackers can use them to access various online accounts, including banking, e-mail, and social media accounts. This can lead to identity theft, financial losses, and other serious consequences for the victim. To protect against attacks like Credential Flusher, it is essential to adopt a series of security measures:
Use updated antivirus software: Ensure that your security software is always up to date to detect and block the latest threats. Enable 2FA Authentication: This measure adds an extra layer of security by requiring a second factor of authentication in addition to the password. Be cautious of phishing attempts: Do not click on suspicious links or download attachments from unverified e-mails. Always verify the authenticity of received communications. Regularly update software: Keep your operating system and all applications updated to fix any security vulnerabilities. Use complex and unique passwords: Avoid reusing the same passwords for multiple accounts and use password managers to generate and store secure passwords.Conclusion
Credential Flusher represents a significant threat to the security of our login credentials. However, by adopting the right protective measures, we can significantly reduce the risk of falling victim to this type of attack. Staying informed about new attack techniques and constantly updating our security practices is essential to protect our personal information.
About the author: Salvatore Lombardo (Twitter @Slvlombardo)
Electronics engineer and Clusit member, for some time now, espousing the principle of conscious education, he has been writing for several online magazine on information security. He is also the author of the book “La Gestione della Cyber Security nella Pubblica Amministrazione”. “Education improves awareness” is his slogan.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Credential Flusher)
.png)












 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·