BOOK THIS SPACE FOR AD
ARTICLE ADHello Guys! I am vasu a bug bounty researcher
A basic idea on a p3 bug of Bug-crowd-taxonomy

What is a CRLF injection vulnerability?
CRLF stands for Carriage Return Linefeed, which is a special sequence of characters (\n and \r in hex) used by the HTTP protocol as a line separator. A CRLF Injection attack occurs when an attacker manages to force the application to return the CRLF sequence plus attacker’s supplied data as part of the response headers.
Line feed = \n (%0a)
Carriage Return = \r (%0d)
CRLF vulnerabilities may be used as XSS (Cross-site Scripting) or HTTP Response Splitting attack vectors. In some cases it may also be possible to poison the cache of intermediate servers (proxies) an attack also known as HTTP Request Smuggling
Example
The below URLs has been split response header.
www.target.com/%3f%0d%0aLocation:%0d%0aContent-Type:text/html%0d%0aX-XSS-Protection%3a0%0d%0a%0d%0a%3Cscript%3Ealert%28document.domain%29%3C/script%3EGET /%0d%0aLocation:%20https://evil.com HTTP/1.1Tips
CRLF injection is most commonly done by modifying an HTTP parameter or URL
Focus on redirecting requests (30x)
Some Interesting Reports from hackerone
Mitigation / Precaution
restrict CR(0x13) and LF(0x10) from the user input
Properly encode the output in order to prevent the injection of custom HTTP headers
Payloads
How To Hunt
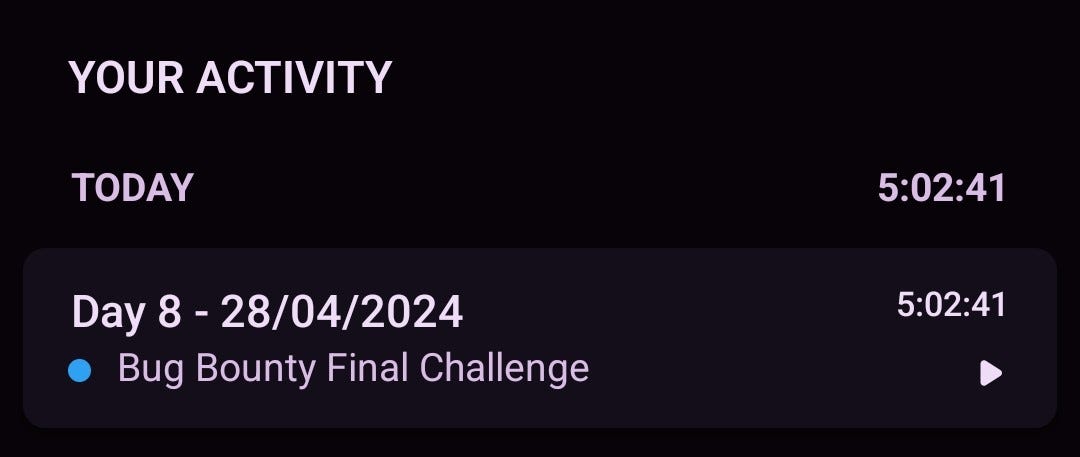
How CRLF can be your first bounty.
Reference
Hey Community this is my first blog, correct me incase any mistake. Thankyou! Linkedin
.png)
 1 year ago
103
1 year ago
103 












 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·