BOOK THIS SPACE FOR AD
ARTICLE AD
CrushFTP warned customers today in a private memo of an actively exploited zero-day vulnerability fixed in new versions released today, urging them to patch their servers immediately.
As the company also explains in a public security advisory published on Friday, this zero-day bug enables unauthenticated attackers to escape the user's virtual file system (VFS) and download system files.
However, those using a DMZ (demilitarized zone) perimeter network in front of their main CrushFTP instance are protected against attacks.
"Please take immediate action to patch ASAP. A vulnerability was reported today (April 19th, 2024), and we patched it immediately. [..] This vulnerability exists in the wild," the company warned customers via email.
"The bottom line of this vulnerability is that any unauthenticated or authenticated user via the WebInterface could retrieve system files that are not part of their VFS. This could lead to escalation as they learn more, etc."
The company also warned customers with servers still running CrushFTP v9 to immediately upgrade to v11 or update their instance via the dashboard.
"There is a simple rollback in case you have an issue or regression with some functionality. Update immediately," CrushFTP warned.
The security flaw was reported by Simon Garrelou of Airbus CERT and is now fixed in CrushFTP versions 10.7.1 and 11.1.0.
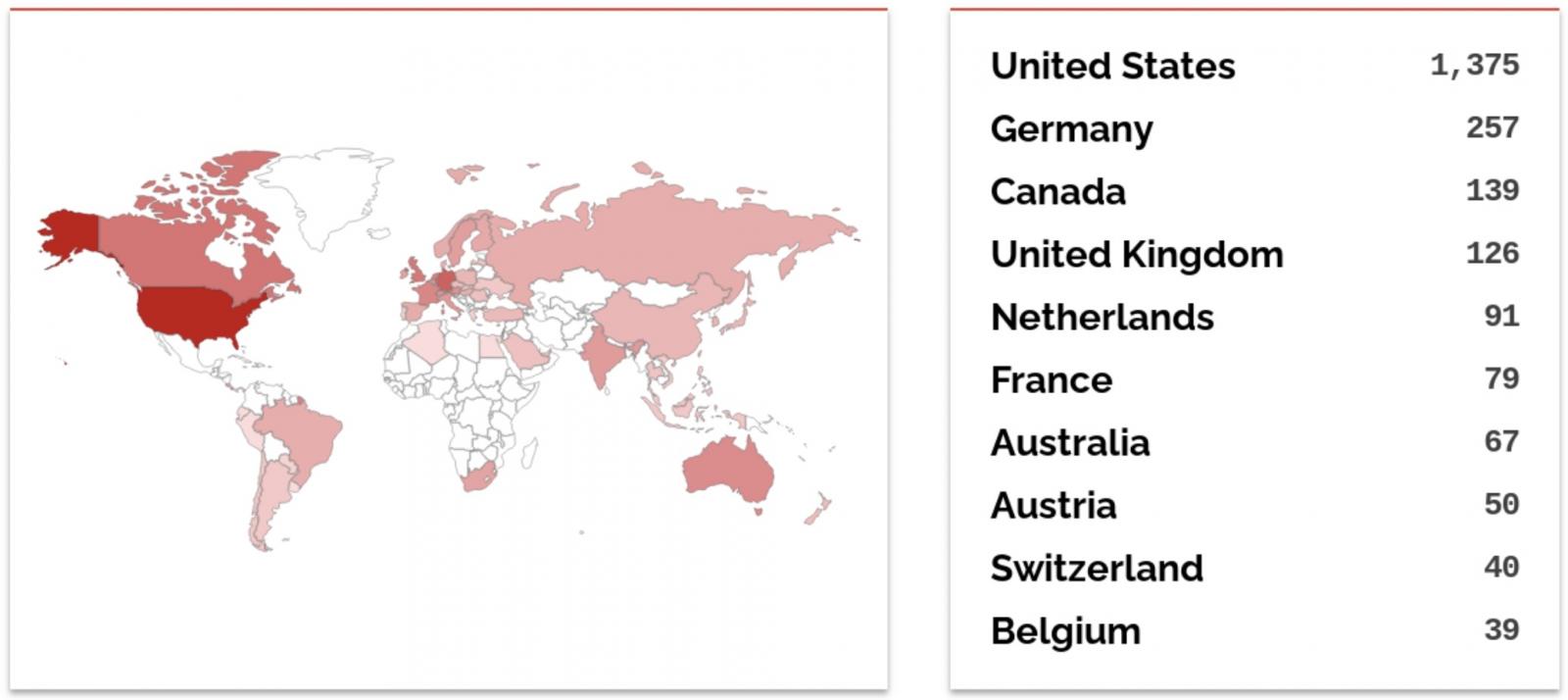
According to Shodan, at least 2,700 CrushFTP instances have their web interface exposed online to attacks, although it's impossible to determine how many have yet to be patched.
Exploited in targeted attacks
Cybersecurity company CrowdStrike also confirmed the vulnerability (which has yet to get a CVE ID assigned) in an intelligence report with more information on the attackers' tactics, techniques, and objectives (TTPs).
CrowdStrike says its Falcon OverWatch and Falcon Intelligence teams have seen the CrushFTP zero-days being exploited in targeted attacks.
The threat actors are targeting CrushFTP servers at multiple U.S. organizations, and evidence points to an intelligence-gathering campaign, likely politically motivated.
"Falcon OverWatch and Falcon Intelligence have observed this exploit being used in the wild in a targeted fashion," CrowdStrike says.
"CrushFTP users should continue to follow the vendor's website for the most up-to-date instructions and prioritize patching."
In November, CrushFTP customers were also warned to patch a critical remote code execution vulnerability (CVE-2023-43177) after Converge security researchers who reported the flaw also released a proof-of-concept exploit.
.png)













 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·