BOOK THIS SPACE FOR AD
ARTICLE AD Image: Midjourney
Image: MidjourneyA new threat actor known as CRYSTALRAY has significantly broadened its targeting scope with new tactics and exploits, now counting over 1,500 victims whose credentials were stolen and cryptominers deployed.
This is being reported by researchers at Sysdig, who have tracked the threat actor since February, when they first reported their use of the SSH-Snake open-source worm to spread laterally on breached networks.
SSH-snake is an open-source worm that steals SSH private keys on compromised servers and uses them to move laterally to other servers while dropping additional payloads on breached systems.
Previously, Sysdig identified roughly 100 CRYSTALRAY victims impacted by the SSH-Snake attacks and highlighted the network mapping tool's capabilities to steal private keys and facilitate stealthy lateral network movement.
Biting harder
Sysdig reports that the threat actor behind these attacks, now tracked as CRYSTALRAY, has significantly scaled up their operations, counting 1,500 victims.
"The team's latest observations show that CRYSTALRAY's operations have scaled 10x to over 1,500 victims and now include mass scanning, exploiting multiple vulnerabilities, and placing backdoors using multiple OSS security tools," reads Sysdig's report.
"CRYSTALRAY's motivations are to collect and sell credentials, deploy cryptominers, and maintain persistence in victim environments. Some of the OSS tools the threat actor is leveraging include zmap, asn, httpx, nuclei, platypus, and SSH-Snake."
 Overview of CRYSTALRAY attacks
Overview of CRYSTALRAY attacksSource: Sysdig
Sysdig says CRYSTALRAY uses modified proof-of-concept (PoC) exploits delivered to targets using the Sliver post-exploitation toolkit, providing another example of misuse of open-source tooling.
Before launching the exploits, the attackers conduct thorough checks to confirm the flaws discovered through nuclei.
The vulnerabilities CRYSTALRAY targets in its current operations are:
CVE-2022-44877: Arbitrary command execution flaw in Control Web Panel (CWP) CVE-2021-3129: Arbitrary code execution bug impacting Ignition (Laravel). CVE-2019-18394: Server-side request forgery (SSRF) vulnerability in Ignite Realtime OpenfireSysdig says Atlassian Confluence products are likely targeted, too, based on the observed exploitation patterns that emerge from attempts against 1,800 IPs, one-third of which are in the U.S.
CRYSTALRAY uses the Platypus web-based manager to handle multiple reverse shell sessions on the breached systems. At the same time, SSH-Snake continues to be the primary tool by which propagation through compromised networks is achieved.
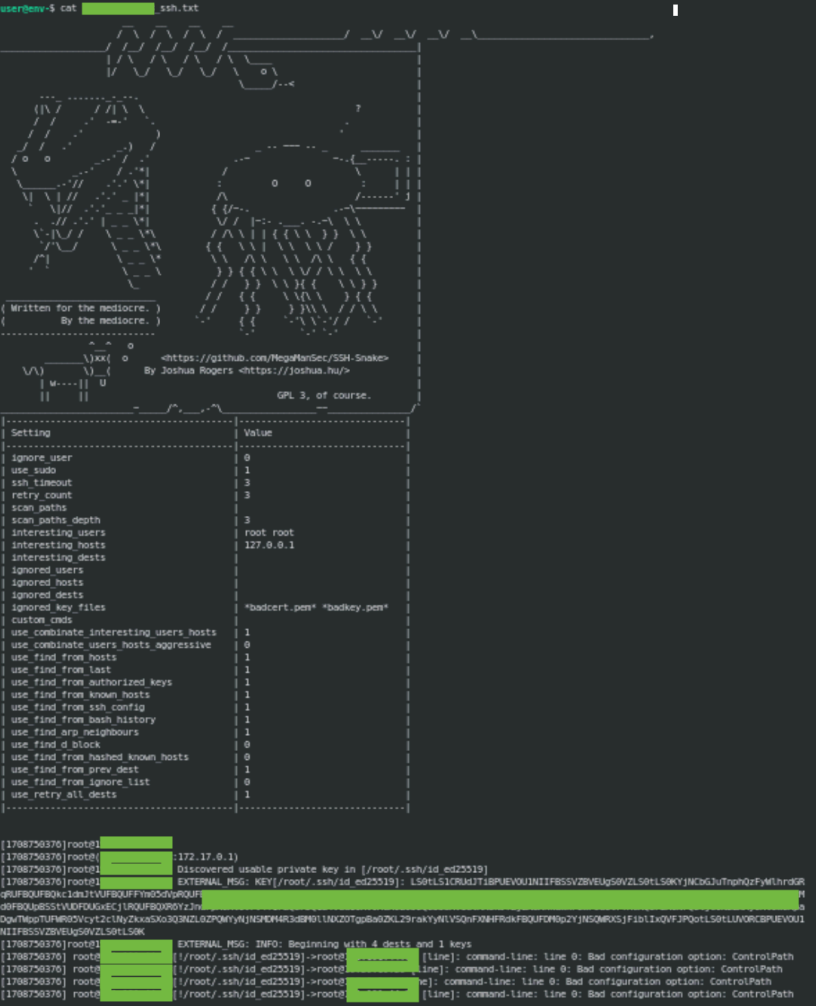 SSH-Snake recovering SSH keys
SSH-Snake recovering SSH keysSource: Sysdig
Once SSH keys are retrieved, the SSH-Snake worm uses them to log into new systems, copy itself, and repeat the process on the new hosts.
SSH-Snake not only spreads the infection but also sends captured keys and bash histories back to CRYSTALRAY's command and control (C2) server, providing options for greater attack versatility.
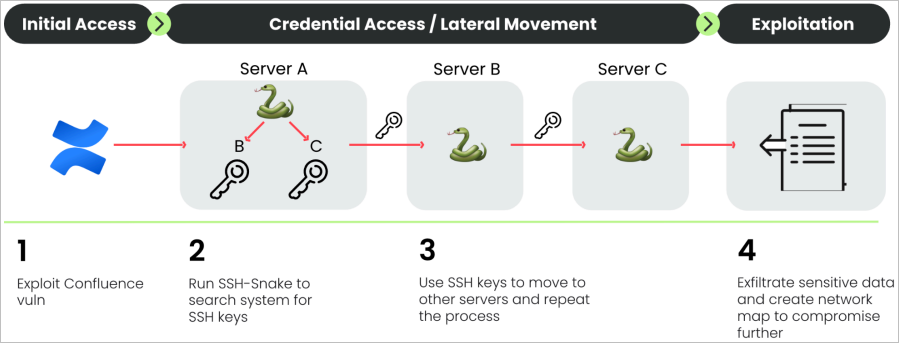 SSH-Snake propagation
SSH-Snake propagationSource: Sysdig
Monetizing stolen data
CRYSTALRAY aims to steal credentials stored in configuration files and environment variables using scripts that automate the process.
Threat actors can sell stolen credentials for cloud services, email platforms, or other SaaS tools on the dark web or Telegram for good profit.
Additionally, CRYSTALRAY deploys cryptominers on the breached systems to generate revenue by hijacking the host's processing power, with a script killing any existing cryptominers to maximize profit.
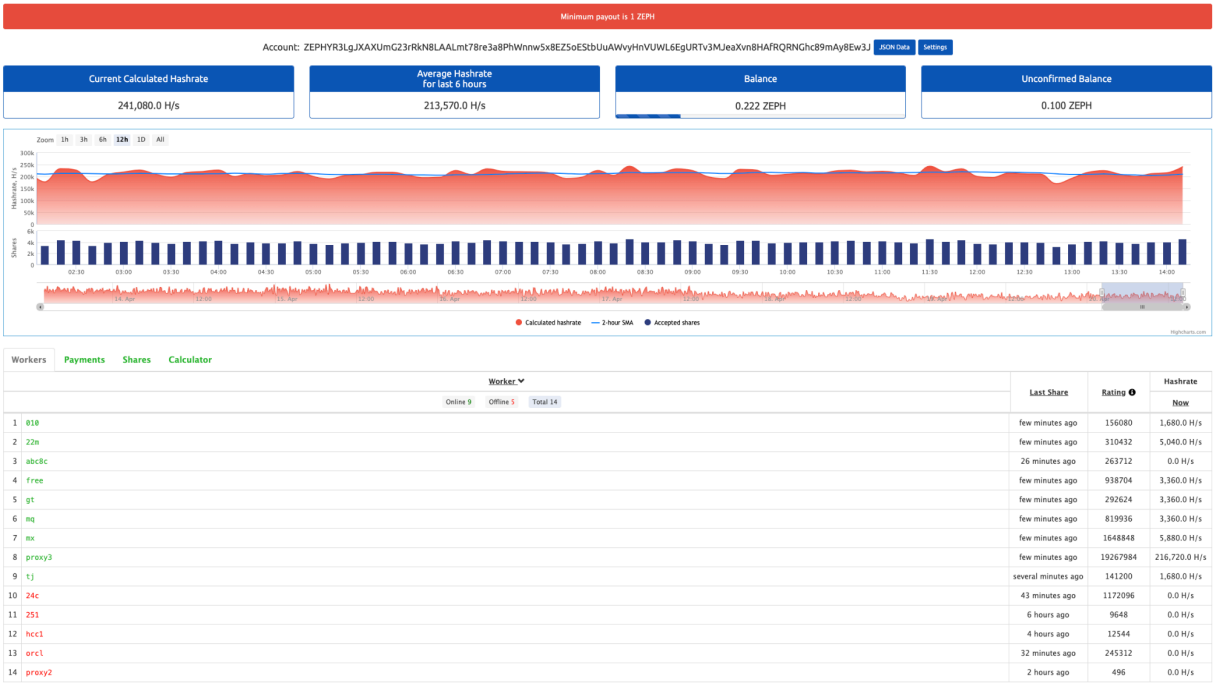 Mining activity associated with CRYSTALRAY operations
Mining activity associated with CRYSTALRAY operationsSource: Sysdig
Sysdig tracked some mining workers to a specific pool and discovered they were making roughly $200/month.
However, starting in April, CRYSTALRAY switched to a new configuration, making it impossible to determine its current revenue.
As the CRYSTALRAY threat grows, the best mitigation strategy is to minimize the attack surface through timely security updates to fix vulnerabilities as they are disclosed.
.png)
















 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·