BOOK THIS SPACE FOR AD
ARTICLE AD
The DarkSide ransomware operation has allegedly shut down after the threat actors lost access to servers and their cryptocurrency was transferred to an unknown wallet.
This news was shared by a threat actor known as 'UNKN', the public-facing representative of the rival REvil ransomware gang, in a forum post first discovered by Recorded Future researcher Dmitry Smilyanets on the Exploit hacking forum.
In the post, 'Unkn' shared a message allegedly from DarkSide explaining how the threat actors lost access to their public data leak site, payment servers, and DoS (denial of service) servers due to law enforcement action.
"Since the first version, we have promised to speak honestly and openly about problems. A few hours ago, we lost access to the public part of our infrastructure, namely : Blog, Payment server, DOS servers," reads the forum post from UNKN.
"Now these servers are unavailable via SSH, the hosting panels are blocked. Hosting support, apart from information "at the request of law enfocement agencies", does not provide any other information."
This news comes a day after President Biden said in a White House press conference that countries harboring ransomware networks must take action to shut them down.
"We do not believe — I emphasize, we do not believe the Russian government was involved in this attack. But we do have strong reason to believe that criminals who did the attack are living in Russia. That’s where it came from — were from Russia," Biden said in a press conference about the Colonial Pipeline attack.
"We have been in direct communication with Moscow about the imperative for responsible countries to take decisive action against these ransomware networks."
Starting yesterday, security researchers and journalists noted that the DarkSide data leak site was no longer accessible, and it was speculated that law enforcement had seized the server.
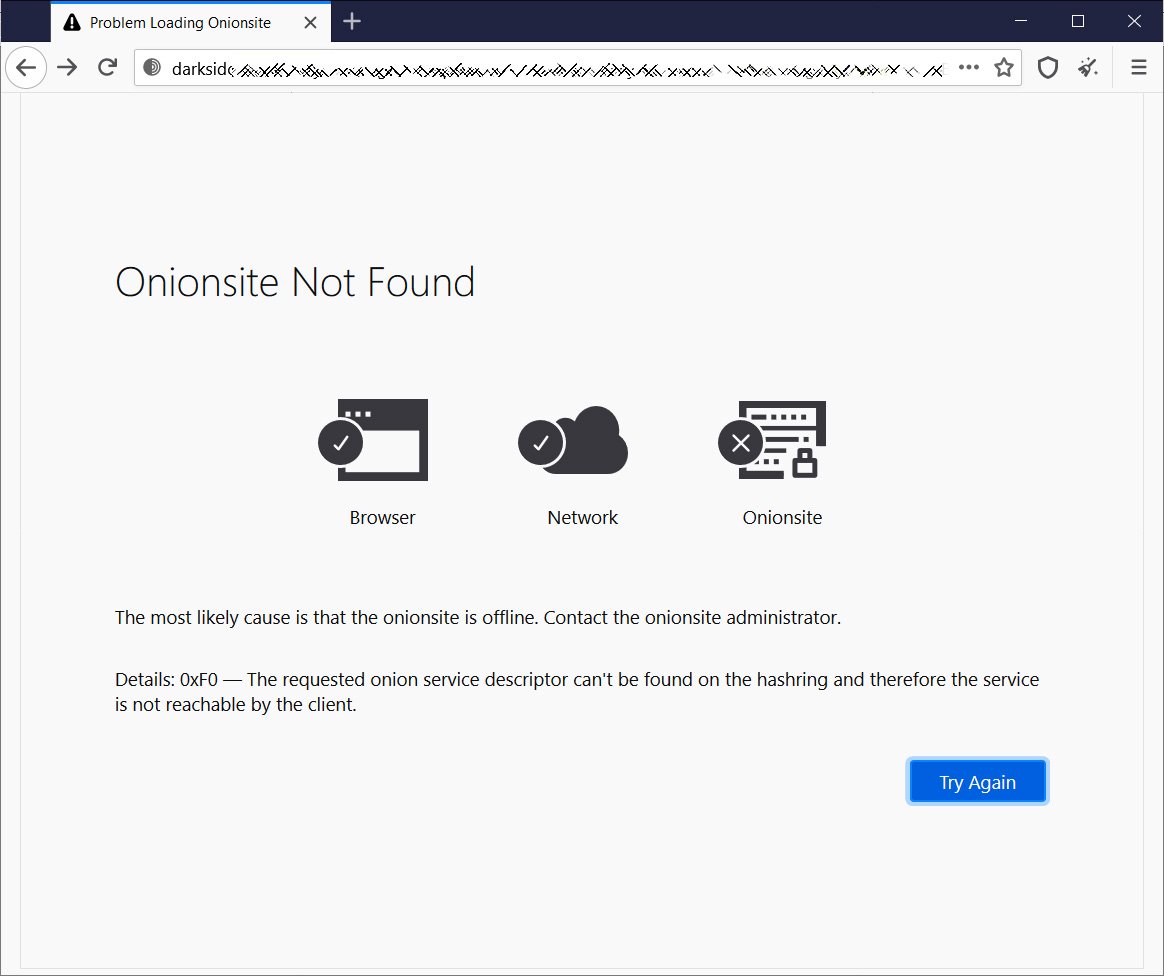 Offline DarkSide data leak site
Offline DarkSide data leak siteHowever, BleepingComputer has confirmed that the DarkSide Tor payment server is still operational at the time of this writing. If law enforcement seized the server, they might have kept it running to allow victims to access their decryptors.
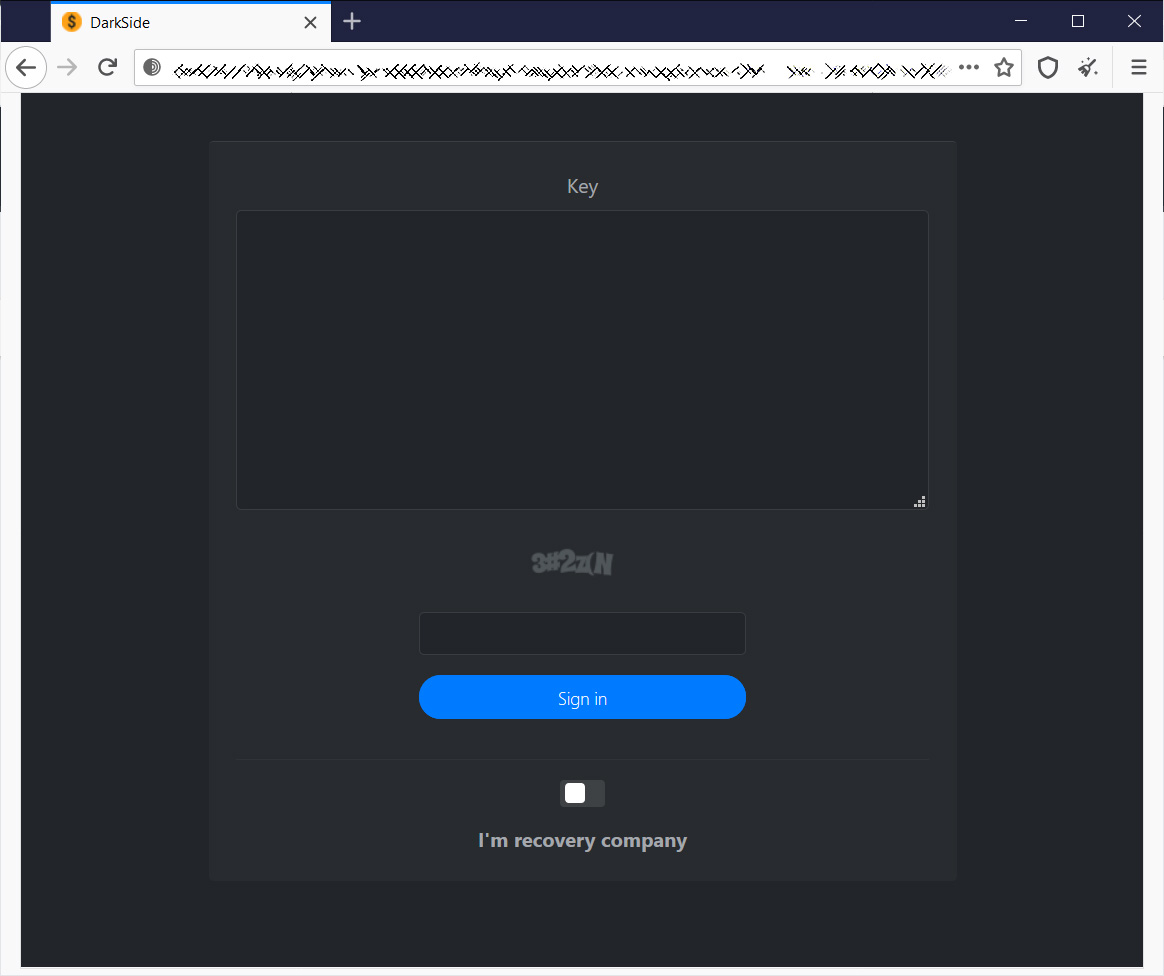 DarkSide Tor payment live at the time of writing
DarkSide Tor payment live at the time of writingFeeling the heat from law enforcement, it has also been speculated that the DarkSide ransomware gang may be pulling an exit scam.
After pulling in $9.4 million in ransom payments this week between Brenntag and Colonial Pipeline, they may be stealing the money, so they do not have to pay affiliates and to blame it on a law enforcement operation.
REvil ransomware adds new restrictions
Historically, the REvil ransomware gang has shown no scruples regarding who they attack.
However, after the DarkSide's reported takedown, REvil has now begun to impose new restrictions on who can be encrypted.
REvil's representative, UNKN, states that affiliates are now required first to gain permission to target an organization and that they can no longer target the following entities:
1. Work in the social sector (health care, educational institutions) is prohibited;
2. It is forbidden to work on the gov-sector (state) of any country;
Ransomware-as-a-Service (RaaS) operations have historically run as a free-for-all, where affiliates encrypt any victim they want without gaining prior approval.
It will be interesting to see if these new rules will lead affiliates to move to other RaaS operations with fewer restrictions.
.png)















 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·