BOOK THIS SPACE FOR AD
ARTICLE AD
Security researchers discovered that personal data of more than 100 million Android users has been exposed due to various misconfigurations of cloud services.
The data was found in unprotected real-time databases used by 23 apps with download counts ranging from 10,000 to 10 million and also includes internal developer resources.
A dozen popular apps expose user data
While misconfigured real-time databases are not a surprise, the discovery shows that some Android developers do not follow basic security practices to restrict access to the app’s database.
The amount of mobile apps with misconfiguration issues shows that this is a widespread problem that can be easily leveraged for malicious purposes.
App developers use real-time databases to store data in the cloud and synchronize it in real-time with connected clients.
Check Point researchers found that some of these databases were left unprotected and anyone could access personal information, some of it sensitive, belonging to over 100 million users.
The data includes names, email addresses, dates of birth, chat messages, location, gender, passwords, photos, payment details, phone numbers, push notifications.
Some of the apps exposing this type of information are present in Google Play and have more than 10 million installations (Logo Maker, Astro Guru). Others, like T'Leva, are less popular but still have a significant user base with installation count between 10,000 and 500,000.
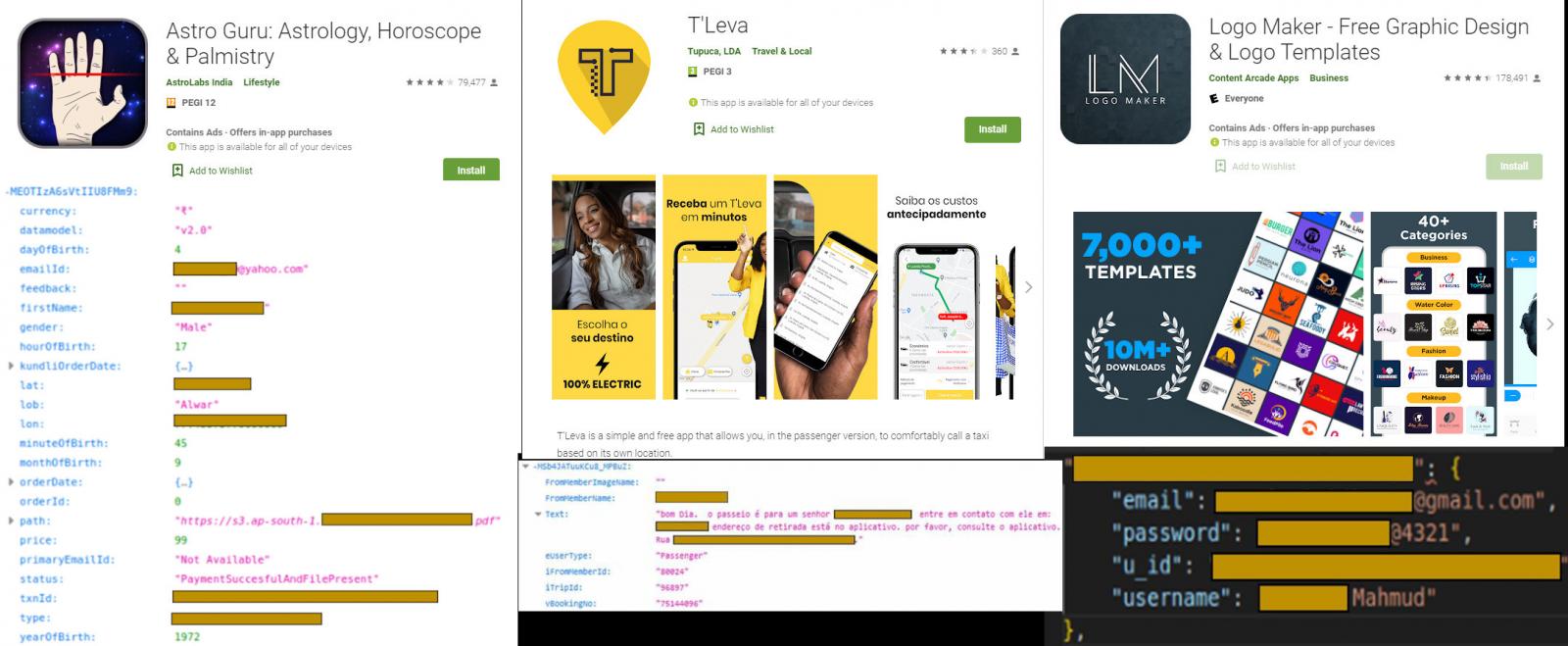 Android apps with unprotected real-time database
Android apps with unprotected real-time databaseAccess keys inside
The researchers also found developer-related sensitive details embedded in some of the tested apps. In one app, they found the credentials for push notification services.
In Screen Recorder, another app on Google Play with over 10 million installations, the researchers found the cloud storage keys that give access to users’ screenshots from the device.
They discovered that iFax Android app also stored the cloud storage keys and the database contained documents and fax transmissions from more than 500,000 users.
Some developers, though, adopted the “security through obscurity” principle and obfuscated the secret key by using base64 encoding, which adds no protection since decoding is not protected.
“Even if the application does not use clear-text keys, all that is needed is to find the piece of code that initializes the cloud-service interface, which mostly receives those keys as parameters, and follow their value. Eventually, if the keys are embedded into the app, we will get their value” - Check Point
Of the 23 apps that Check Point researchers analyzed, a dozen have more than 10 million installations on Google Play and most of them had the real-time database unprotected, exposing sensitive user information.
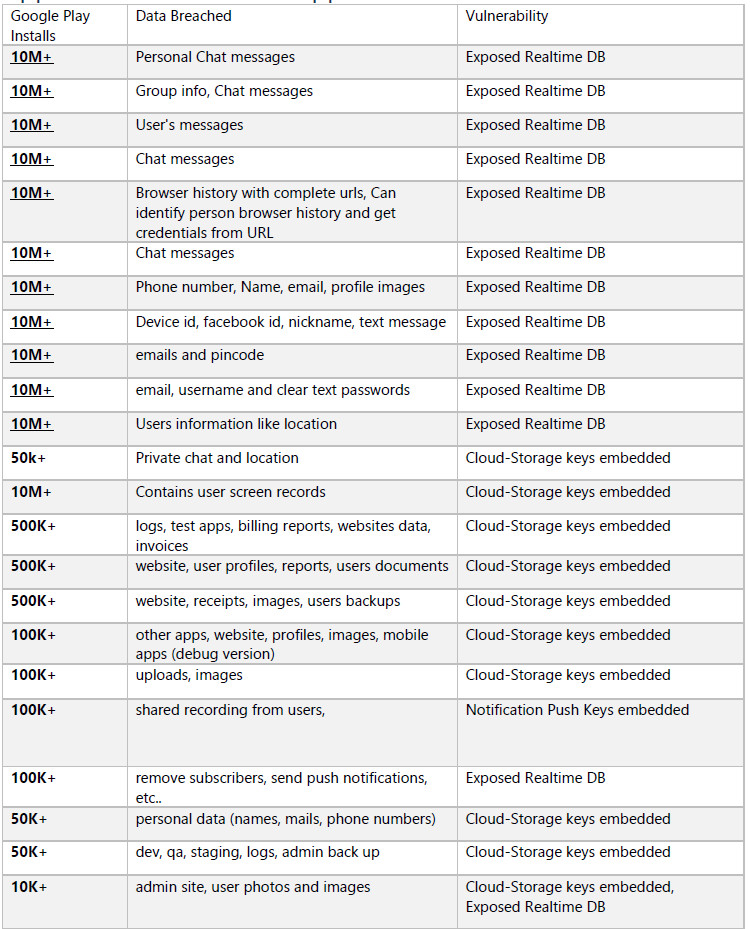 User info exposed in unprotected databases of Android apps
User info exposed in unprotected databases of Android appsAlthough the issue is not new, it is surprising that that highly-popular applications don’t enforce basic security practices to protect their users and data.
.png)













 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·