BOOK THIS SPACE FOR AD
ARTICLE ADDirtyMoe is a Windows botnet that is rapidly growing, it passed from 10,000 infected systems in 2020 to more than 100,000 in the first half of 2021.
Researchers from Avast are warning of the rapid growth of the DirtyMoe botnet (PurpleFox, Perkiler, and NuggetPhantom), which passed from 10,000 infected systems in 2020 to more than 100,000 in the first half of 2021. Experts defined DirtyMoe as a complex malware that has been designed as a modular system.
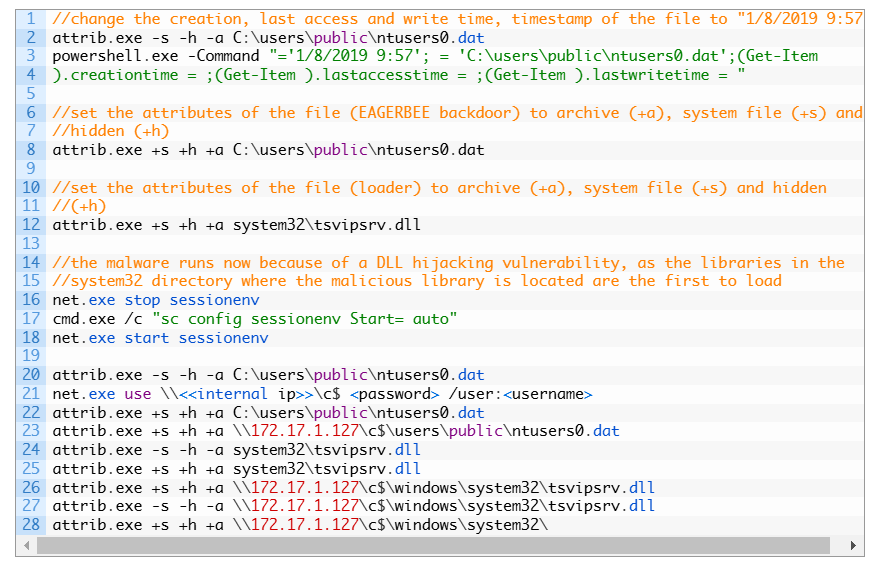
The Windows botnet has been active since late 2017, it was mainly used to mine cryptocurrency, but it was also involved in DDoS attacks in 2018. The DirtyMoe rootkit was delivered via malspam campaigns or served by malicious sites hosting the PurpleFox exploit kit that triggers vulnerabilities in Internet Explorer, such as the CVE-2020-0674 scripting engine memory corruption vulnerability.
The operations behind the DirtyMoe botnet rapidly changed since the end of 2020, when the malware authors added a worm module that could increase their activity by spread via the internet to other Windows systems.
“Recently, a new infection vector that cracks Windows machines through SMB password brute force is on the rise” reads the analysis published by AVAST.
The module that implements the warm capabilities was spotted scanning the internet and performing password brute-force attacks against Windows systems with SMB port open online.
“The increase of incidences has been higher in orders of magnitude this year, as the logarithmic scale of Figure 3 indicates.” continues the report.
Most of the hits are in Russia (65k), followed by Ukraine, Vietnam and Brazil.
Experts pointed out that the number of infected systems could be far greater because data provided by AVAST are only related to systems running their antivirus solution.
Most of the C&C servers involved in the attacks are located in China, a circumstance that suggests that the threat actors behind DirtyMoe are a well-organized group that operates on a global scale.
“The malware implements many self-defense and hiding techniques applied on local, network, and kernel layers. Communication with C&C servers is based on DNS requests and it uses a special mechanism translating DNS results to a real IP address. Therefore, blocking of C&C servers is not an easy task since C&C addresses are different each time and they are not hard-coded.” concludes the analysis.” continues the analysis. “Both PurpleFox and DirtyMoe are still active malware and gaining strength.”
Avast published indicators of compromise (IOCs) related to the attacks that involved this botnet
Follow me on Twitter: @securityaffairs and Facebook
(SecurityAffairs – hacking, botnet)
.png)














 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·