BOOK THIS SPACE FOR AD
ARTICLE ADSummary:
When a user uploads an image in example.com, the uploaded image’s EXIF Geolocation Data does not gets stripped. As a result, anyone can get sensitive information of example.com users like their Geolocation, their Device information like Device Name, Version, Software & Software version used etc.
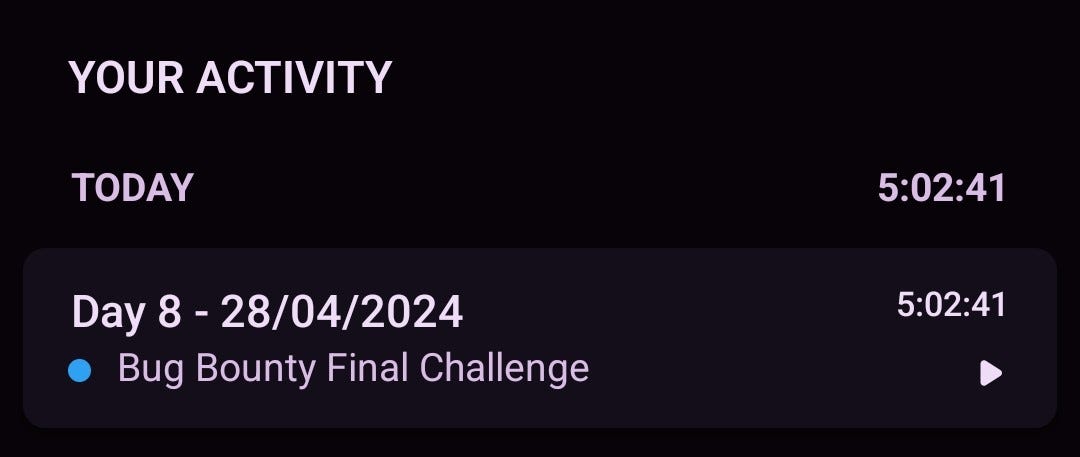
Steps to reproduce:
Got to Github ( https://github.com/ianare/exif-samples/tree/master/jpg)There are lot of images having resolutions (i.e 1280 * 720 ) , and also whith different MB’s .Go to Upload option on the websiteUpload the imagesee the path of uploaded image ( Either by right click on image then copy image address OR right click, inspect the image, the URL will come in the inspect , edit it as html )open it (http://exif.regex.info/exif.cgi)See wheather is that still showing exif data , if it is then Report it.Reports (Hackerone)
IDOR with Geolocation data not stripped from imagesbusiness logic , register vulnerability , bypass 2fa , authentication ,IDOR
https://github.com/Az0x7/vulnerability-Checklist
linkedin , Twitter.png)
 1 year ago
76
1 year ago
76 












 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·