BOOK THIS SPACE FOR AD
ARTICLE ADNorth Korean hackers are infiltrating Western companies using fraudulent IT workers to steal sensitive data and extort ransom. Learn how to identify these deceptive tactics and protect your organization from this growing threat. Secureworks reveals the latest strategies employed by the North Korean threat group NICKEL TAPESTRY.
A recent report by cybersecurity firm Secureworks has exposed a disturbing but not-so-new tactic employed by North Korean hackers. They are infiltrating Western companies by posing as legitimate IT workers, stealing sensitive data, and then demanding ransom for its return.
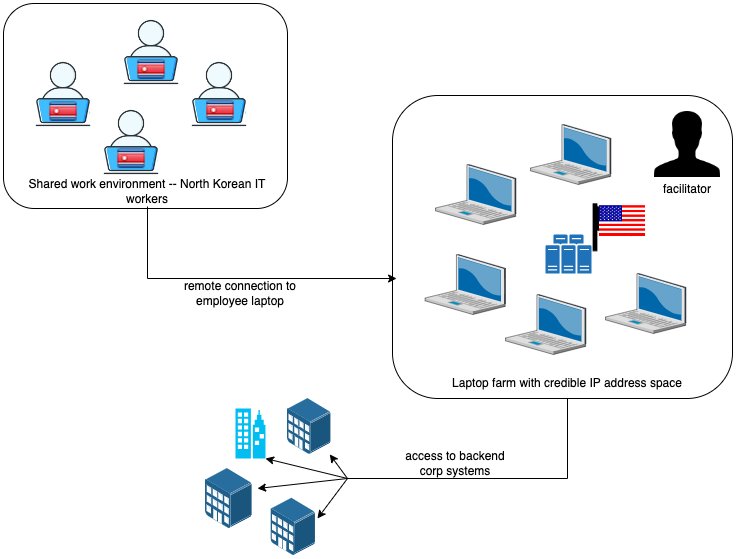
The mastermind behind this scheme is a North Korean hacking group known as Nickel Tapestry. The group operates from “laptop farms,” using stolen or falsified identities to fool HR departments at companies across the US, UK, and Australia. Often applying for developer positions, they utilize a variety of tactics to evade and conceal their identities/locations.
For instance, they request changes to delivery addresses for corporate laptops, often rerouting them to laptop farms, and sometimes they express a strong preference for using personal laptops and virtual desktop infrastructure (VDI) setups, a tactic previously warned by the FBI. This allows them to remotely access company networks without leaving a trace.
Also, they often exhibit “suspicious financial behaviours” such as frequent changes to bank account information or utilizing digital payment services to bypass traditional banking systems.
Additionally, the group uses residential proxy addresses and VPNs to mask their actual IP addresses. They also use “Splitcam” software during video calls to simulate video calls, avoiding the need to enable their webcams by creating fake AI clones of themselves.
In one case, a fake worker gained access to a company’s network, exfiltrated sensitive data, and then – after being fired for poor performance – demanded a six-figure ransom for its return. This extortion element significantly increases the potential financial damage caused by these attacks.
“The emergence of ransom demands marks a notable departure from prior NICKEL TAPESTRY schemes. However, the activity observed prior to the extortion aligns with previous schemes involving North Korean workers,” Secureworks’ Counter Threat Unit research team wrote in the report.
Perhaps most disturbing is the evidence of collaboration between these fake workers. They may provide fake references for each other, perform job duties on each other’s behalf, and even communicate via email while masquerading as different individuals. In one instance, researchers believe a single individual may have adopted multiple personas to further the scam.
You’ve Been Warned!
This IT worker scam isn’t new. Similar tactics have been observed since 2018, with fraudulent workers securing positions at Fortune 100 companies and funnelling stolen intellectual property back to North Korea to potentially fund weapons programs, including weapons of mass destruction.
In May 2022, the US government warned organizations to beware of North Korean hackers in the guise of IT freelancers claiming to be non-DPRK (Democratic People’s Republic of Korea) nationals.
In July 2024, North Korean hackers attempted another fake hiring scheme, this time targeting KnowBe4, a prominent U.S.-based cybersecurity company. In this case, a hacker posed as an IT worker and managed to secure employment with the company. The next step in the attack involved installing malware on a company-issued MacBook, intending to compromise KnowBe4’s systems.
Protection Measures
How can companies protect themselves from this evolving threat? Secureworks recommends thorough background checks and verification of candidate identities. Researchers suggest that a candidate’s work traits, such as applying for a full stack developer position, claiming 8-10 years of experience, and having novice to intermediate English skills, are the biggest red flags.
Additionally, unusual communication hours, varying communication styles, excuses for not enabling cameras during interviews, and a call center-like tone should trigger further investigation.
.png)














 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·