A recent wave of spear-phishing campaigns leveraged weaponized Windows 11 Alpha-themed Word documents with Visual Basic macros to drop malicious payloads, including a JavaScript implant, against a point-of-sale (PoS) service provider located in the U.S.
The attacks, which are believed to have taken place between late June to late July 2021, have been attributed with "moderate confidence" to a financially motivated threat actor dubbed FIN7, according to researchers from cybersecurity firm Anomali.
"The specified targeting of the Clearmind domain fits well with FIN7's preferred modus operandi," Anomali Threat Research said in a technical analysis published on September 2. "The group's goal appears to have been to deliver a variation of a JavaScript backdoor used by FIN7 since at least 2018."
An Eastern European group active since at least mid-2015, FIN7 has a checkered history of targeting restaurant, gambling, and hospitality industries in the U.S. to plunder financial information such as credit and debit card numbers that were then used or sold for profit on underground marketplaces.
Although multiple members of the collective have been imprisoned for their roles in different campaigns since the start of the year, FIN7's activities have also been tied to another group called Carbanak, given its similar TTPs, with the main distinction being that while FIN7 focuses on hospitality and retail sectors, Carbanak has singled out banking institutions.
In the latest attack observed by Anomali, the infection commences with a Microsoft Word maldoc containing a decoy image that's purported to have been "made on Windows 11 Alpha," urging the recipient to enable macros to trigger the next stage of activity, which involves executing a heavily-obfuscated VBA macro to retrieve a JavaScript payload, which has been found to share similar functionality with other backdoors used by FIN7.
Besides taking several steps to try to impede analysis by populating the code with junk data, the VB script also checks if it is running under a virtualized environment such as VirtualBox and VMWare, and if so, terminates itself, in addition to stopping the infection chain upon detecting Russian, Ukrainian, or several other Eastern European languages.
The backdoor's attribution to FIN7 stems from overlaps in the victimology and techniques adopted by the threat actor, including the use of a JavaScript-based payload to plunder valuable information.
"FIN7 is one of the most notorious financially motivated groups due to the large amounts of sensitive data they have stolen through numerous techniques and attack surfaces," the researchers said. "Things have been turbulent for the threat group over the past few years as with success and notoriety comes the ever-watchful eye of the authorities. Despite high-profile arrests and sentencing, including alleged higher-ranking members, the group continues to be as active as ever."
Found this article interesting? Follow THN on Facebook, Twitter and LinkedIn to read more exclusive content we post.
.png)
 3 years ago
320
3 years ago
320 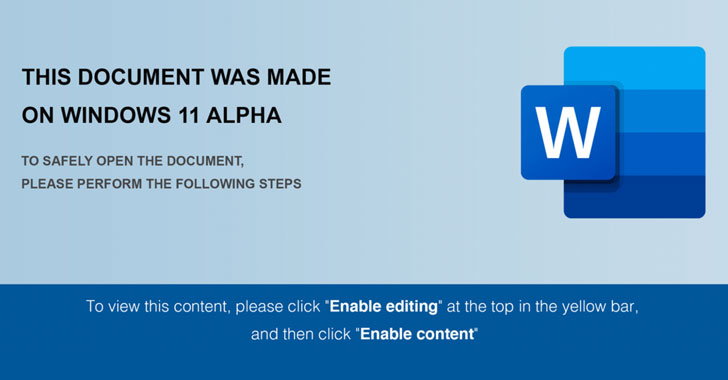
















 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·