BOOK THIS SPACE FOR AD
ARTICLE ADA sophisticated VPN phishing and vishing campaign targeting over 130 US organizations uses social engineering tactics like phone calls and SMS messages to steal credentials. Threat actors impersonate IT staff, leading victims to fake login pages to gain network access.
Cybersecurity researchers at GuidePoint Research and Intelligence Team (GRIT) have uncovered a sophisticated phishing campaign targeting over 130 US organizations across various industries. The campaign, which utilizes highly effective social engineering tactics, involves threat actors posing as IT support staff to trick employees into revealing their VPN credentials.
The Call
The attack begins with a phone call (vishing or voice phishing attack) to an employee’s personal cell phone. The attacker poses as a member of the company’s help desk or IT team, claiming to be assisting with a VPN login issue. Once trust is established, the attacker sends the victim an SMS message containing a link to a fake VPN login page designed to mimic the legitimate VPN portal of the targeted organization.
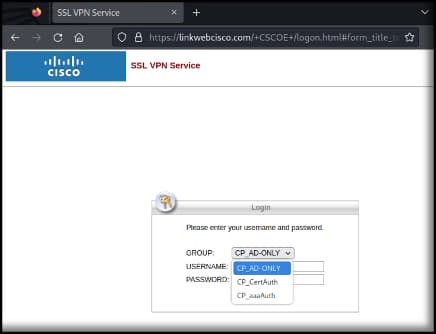
These fake login pages are made to look convincing by listing the real VPN groups used by the company. Sometimes, the attackers even create fake VPN groups like “TestVPN” and “RemoteVPN” to make the trick even more believable.
Once the user enters their credentials, including any multi-factor authentication (MFA) tokens, they are redirected to the legitimate VPN portal. This final step is designed to reassure the user that the issue has been resolved, while the attackers successfully harvest their login information.
Once they gain access to the network through the compromised VPN credentials, they immediately begin scanning for vulnerable systems to expand their access, establish persistence, and escalate privileges.
GRIT’s report shared with Hackread.com ahead of publishing, indicates that the attackers are financially motivated. Their ultimate goal is to steal sensitive data, destroy backups, and deploy ransomware for operational disruption and ransom.
GRIT researchers have also identified several domain names and IP addresses associated with the campaign, which has been active since June 26, 2024. These domain names closely resemble the VPN technologies used by the targeted organizations including CISCO, Fortinet and Palo Alto:
fortivpnlink.comvpnpaloalto.com
ciscoweblink.com
linkwebcisco.com
ciscolinkweb.com
ciscolinkacc.com
ciscoacclink.com
linkciscoweb.com
Although the report does not discuss the origin of these threat actors or the group involved, it is important to note that the ALPHV Ransomware gang (aka BlackCat) is known for using vishing attacks. One of the group’s successful targets in such an attack was an employee at the global entertainment and hospitality giant MGM Resorts, which caused worldwide service disruptions and other damages to the organization.
Nevertheless, in response to the latest threat, GRIT recommends that organizations must review VPN logs for any suspicious activity originating from VPN-assigned IP addresses over the past 30 days. If any unusual activity is identified, a thorough investigation should assess potential compromises.
Additionally, the most important part is raising cybersecurity awareness among employees; they should be educated about this type of social engineering attack and encouraged to promptly report any suspicious calls from unknown numbers claiming to be IT or help desk staff.
.png)














 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·