Industrial engineers and operators are the target of a new campaign that leverages password cracking software to seize control of Programmable Logic Controllers (PLCs) and co-opt the machines to a botnet.
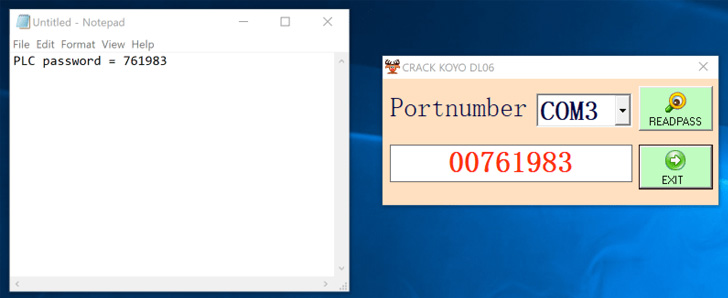
The software "exploited a vulnerability in the firmware which allowed it to retrieve the password on command," Dragos security researcher Sam Hanson said. "Further, the software was a malware dropper, infecting the machine with the Sality malware and turning the host into a peer in Sality's peer-to-peer botnet."
The industrial cybersecurity firm said the password retrieval exploit embedded in the malware dropper is designed to recover the credential associated with Automation Direct DirectLOGIC 06 PLC.
The exploit, tracked as CVE-2022-2003 (CVSS score: 7.7), has been described as a case of cleartext transmission of sensitive data that could lead to information disclosure and unauthorized changes. The issue was addressed in firmware Version 2.72 released last month.
The infections culminate in the deployment of the Sality malware for carrying out tasks such as cryptocurrency mining and password cracking in a distributed fashion, while also taking steps to remain undetected by terminating security software running in the compromised workstations.
What's more, the artifact unearthed by Dragos functions drops a crypto-clipper payload that steals cryptocurrency during a transaction by substituting the original wallet address saved in the clipboard with the attacker's wallet address.
Automation Direct is not the only vendor impacted as the tools claim to encompass several PLCs, human-machine interfaces (HMIs), and project files spanning Omron, Siemens, ABB Codesys, Delta Automation, Fuji Electric, Mitsubishi Electric, Schneider Electric's Pro-face, Vigor PLC, Weintek, Rockwell Automation's Allen-Bradley, Panasonic, Fatek, IDEC Corporation, and LG.
"In general, it appears there is an ecosystem for this type of software," Hanson noted, attributing the attacks to a likely financially motivated adversary. "Several websites and multiple social media accounts exist all touting their password 'crackers.'"
This is far from the first time trojanized software has singled out operational technology (OT) networks. In October 2021, Mandiant disclosed how legitimate portable executable binaries are being compromised by a variety of malware such as Sality, Virut, and Ramnit, among others.
Found this article interesting? Follow THN on Facebook, Twitter and LinkedIn to read more exclusive content we post.
.png)
 2 years ago
185
2 years ago
185 

















 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·