BOOK THIS SPACE FOR AD
ARTICLE AD
North Korean hackers have been exploiting the updating mechanism of the eScan antivirus to plant backdoors on big corporate networks and deliver cryptocurrency miners through GuptiMiner malware.
Researchers describe GuptiMiner as "a highly sophisticated threat" that can perform DNS requests to the attacker's DNS servers, extract payloads from images, sign its payloads, and perform DLL sideloading.
Delivering GuptiMiner via eScan updates
In a report released today, cybersecurity company Avast says that the threat actor behind GuptiMiner had an adversary-in-the-middle (AitM) position to hijack the normal virus definition update package and replace it with a malicious one named ‘updll62.dlz.’
The malicious file includes the necessary antivirus updates as well as a GuptiMiner malware as a DLL file named ‘version.dll.’
The eScan updater processes the package as normal, unpacking and executing it. During that stage, the DLL is sideloaded by eScan’s legitimate binaries, giving the malware system-level privileges.
Next, the DLL fetches additional payloads from the attacker’s infrastructure, establishes persistence on the host via scheduled tasks, performs DNS manipulation, injects shellcode on legitimate processes, uses code virtualization, stores XOR-encrypted payloads in the Windows registry, and extracts PEs from PNGs.
GuptiMiner also checks if the system it runs has more than 4 CPU cores and 4GB of RAM to evade sandbox environments, and determines if Wireshark, WinDbg, TCPView, 360 Total Security, Huorong Internet Security, Process Explorer, Process Monitor, and OllyDbg are actively running.
AhnLab and Cisco Talos products are also deactivated if they are running on the breached machine. Below is a complete diagram of the infection chain:
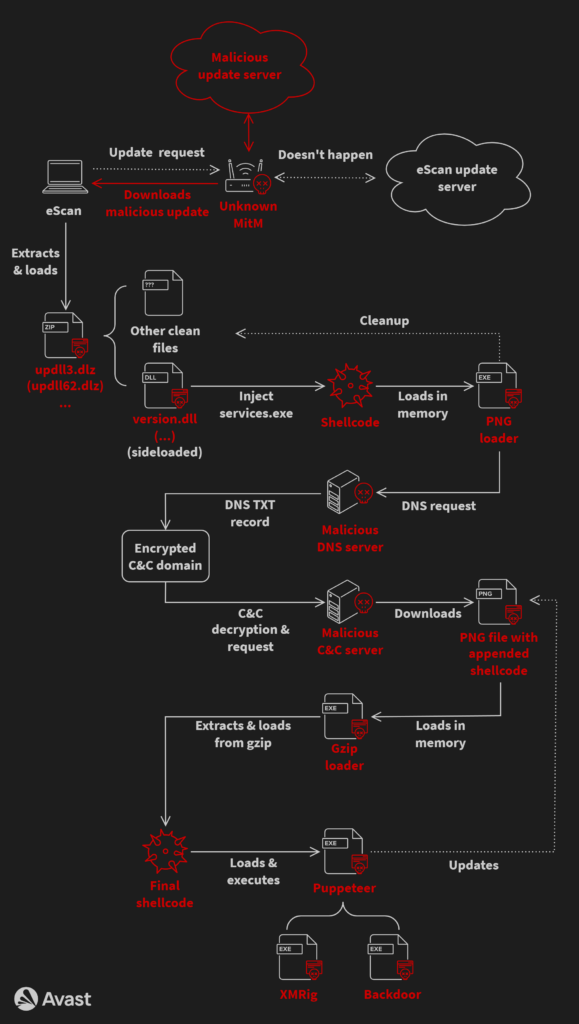 GuptiMiner attack chain
GuptiMiner attack chainAvast
Avast researchers say that GuptiMiner may be linked to the North Korean APT group Kimsuki, based on similarities between the information stealing function and the Kimsuky keylogger.
The researchers also discovered that some parts of the GuptiMiner operation suggest a possible connection to Kimsuki. A commonality is the use of the domain mygamesonline[.]org, which is ordinarily seen in Kimsuky operations.
Deployed malware tools
The hackers used GuptiMiner to deploy multiple malware on compromised systems, including two distinct backdoors and the XMRig Monero miner.
The first backdoor is an enhanced version of Putty Link, deployed on corporate systems to scan the local network for vulnerable systems and pivot points for lateral movement.
It specifically seeks out Windows 7 and Windows Server 2008 systems, exploiting them through SMB traffic tunneling.
The second backdoor is a complex modular malware that scans the host for stored private keys and cryptocurrency wallets, and creates a registry key to mark the completion of the scan, to avoid noisy repeats.
It can accept commands to install additional modules in registry, further enhancing its capabilities within infected environments. However, Avast did not provide additional details.
The attackers also dropped the XMRig miner in many cases, which is in contrast with the sophistication exhibited in the analyzed campaign and could be an attempt to divert attention from the main attack line.
eScan’s response
Avast researchers disclosed the exploited vulnerability to eScan and the antivirus vendor confirmed that the issue was fixed.
eScan also said that the last similar report they received was in 2019. In 2020, the vendor implemented a more robust checking mechanism to make sure that non-signed binaries were rejected.
In the most recent implementation, eScan's update downloads occur over HTTPS to ensure encrypted communication for clients interacting with the vendor's cloud-facing servers.
However, Avast reports that it continues to observe new infections by GuptiMiner, which could indicate outdated eScan clients.
The complete list of GuptiMiner indicators of compromise (IoCs) to help defenders mitigate this threat can be found on this GitHub page.
.png)













 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·