Threat actors leveraged a cloud video hosting service to carry out a supply chain attack on more than 100 real estate websites operated by Sotheby's Realty that involved injecting malicious skimmers to steal sensitive personal information.
"The attacker injected the skimmer JavaScript codes into video, so whenever others import the video, their websites get embedded with skimmer codes as well," Palo Alto Networks' Unit 42 researchers said in a report published this week.
The skimmer attacks, also called formjacking, relates to a type of cyber attack wherein bad actors insert malicious JavaScript code into the target website, most often to checkout or payment pages on shopping and e-commerce portals, to harvest valuable information such as credit card details entered by users.
In the latest incarnation of the Magecart attacks, the operators behind the campaign breached the Brightcove account of Sotheby's and deployed malicious code into the player of the cloud video platform by tampering with a script that can be uploaded to add JavaScript customizations to the video player.
"The attacker altered the static script at its hosted location by attaching skimmer code. Upon the next player update, the video platform re-ingested the compromised file and served it along with the impacted player," the researchers said, adding it worked with the video service and the real estate company to help remove the malware.
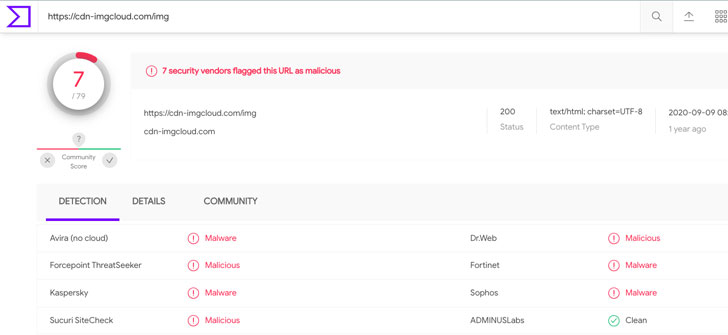
The campaign is said to have begun as early as January 2021, according to MalwareBytes, with the harvested information — names, emails, phone numbers, credit card data — exfiltrated to a remote server "cdn-imgcloud[.]com" that also functioned as a collection domain for a Magecart attack targeting Amazon CloudFront CDN in June 2019.
"A Brightcove customer experienced a security issue that originated with videos stored by the customer on a third-party solution, and at no point were other customers, or their end-users, at risk due to this incident," the company said in a statement shared with The Hacker News.
To detect and prevent injection of malicious code into online sites, it's recommended to conduct web content integrity checks on a periodic basis, not to mention safeguard accounts from takeover attempts and watch out for potential social engineering schemes.
"The skimmer itself is highly polymorphic, elusive and continuously evolving," the researchers said. "When combined with cloud distribution platforms, the impact of a skimmer of this type could be very large."
Found this article interesting? Follow THN on Facebook, Twitter and LinkedIn to read more exclusive content we post.
.png)
 2 years ago
142
2 years ago
142 


















 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·