BOOK THIS SPACE FOR AD
ARTICLE ADHi
I Found a host header injection on a Hackerone target frontegg which lead to open redirect and cache poisoning
let’s start
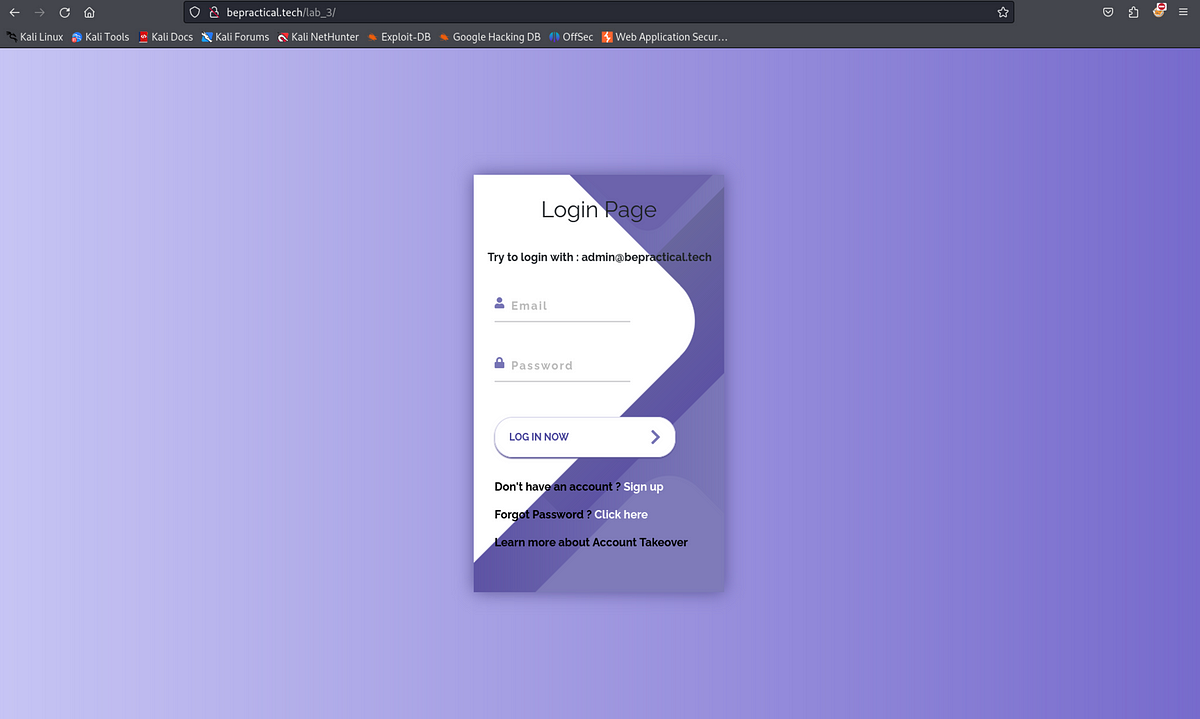
Target:portal.au.frontegg.com
Open burpsuite and capture the first request
It redirect to us to portal.au.frontegg.com
now change the host
You can see that now the location parameter change in response after changing in request
Follow redirection 2 times and You will get this
Now you get the 200ok in response
you will redirect to bing.com and by this way you can also steal cookies and sensitive information into attacker website and if you try it more many times it will become cache poisoning and you don’t need to try host header attack again and again it will automatically redirect to attacker site
Thank you !!
.png)
 4 months ago
25
4 months ago
25 













 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·