BOOK THIS SPACE FOR AD
ARTICLE ADHey folks,
I’m here to share one of my old finding. In which i found a unique way of an open redirection which leads to an account takeover.
So the Web App i testing was a Trading Platform. Let’s call it target.com for the demonstration purpose.
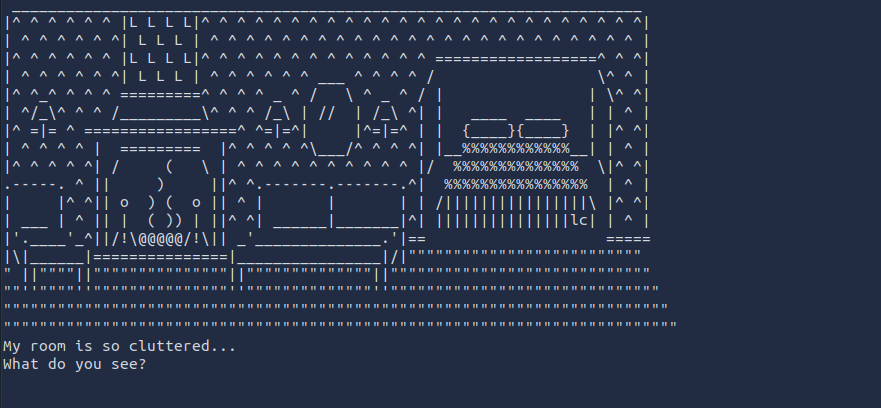
So there is a subdomain which used to login on platform. lets call it web.target.com and created a test account. After logged in i notice a feature “Verify whats-app number” so that user can verify account, reset password(both on email and directly through whats-app), get trading updates directly through whats-app. So i continued testing this functionality. While testing i noticed 2 things “number” & “domain” interesting that in post request. Is that mean that i can also change the domain?
Always trust on your Spider-Senselet’s see if i can able to perform Open Redirection
Steps:
Go to https://web.target.com & login.2. Now go to profile and add whats-app number.submit victim number/test number.
3. Intercept that request in Burp Suite and send it to repeater.
4. Now i change the “domain”: in request to “domain”:”https://bing.com" the request & response look like:

5. Now the victim receives a message from Target.com official whats-app account. victim click on link and redirected to attackers domain.

But that’s a low severity issue and doesn’t seem a security concern. So i just did one thing and try to leverage it to some serious vulnerability.
6. After verification of Whats app number i requested for password reset token. And captured that request in burpsuite.
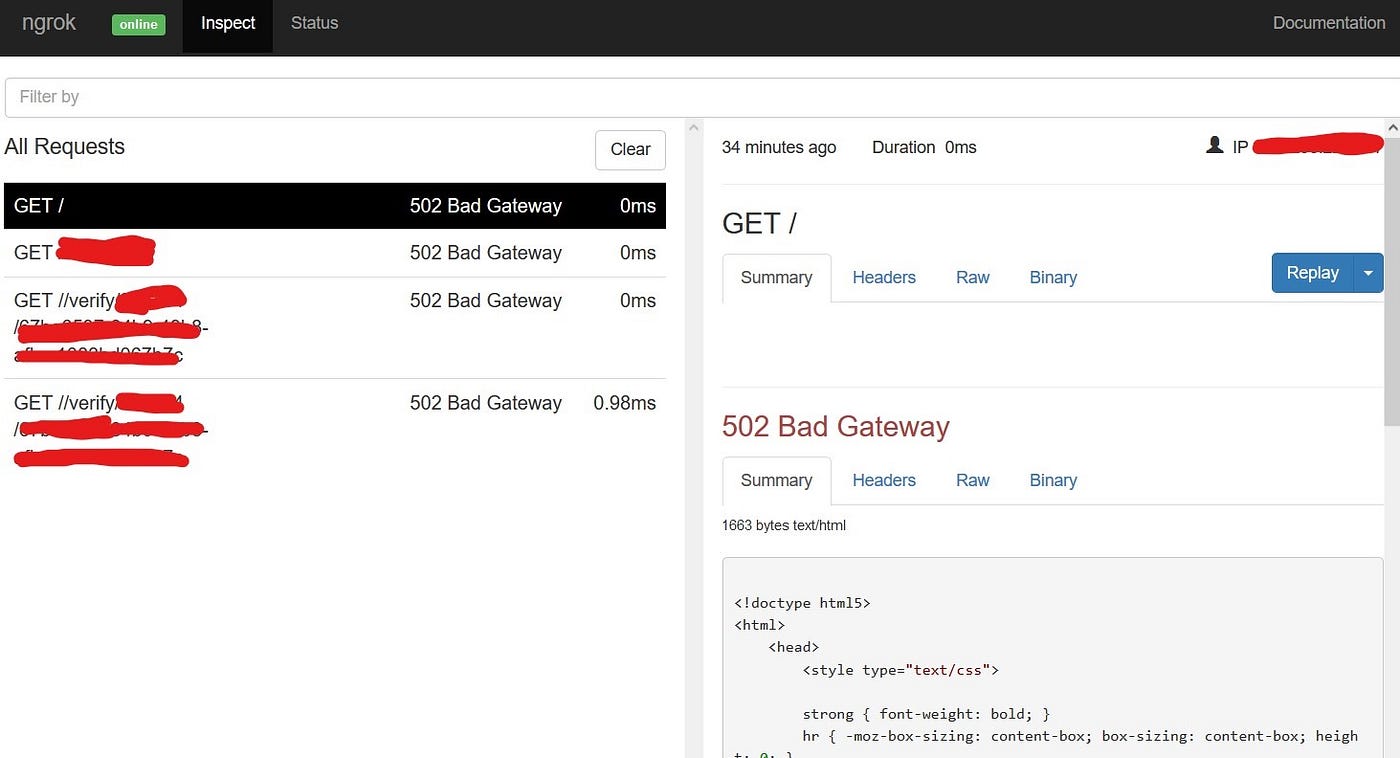
7. Changed the “domain” to Ngrok URL and got message with reset link.
8. same time got a request in Ngrok dashboard, which carry password reset token.
9. I used that token to reset password of victim account.
Impact: This vulnerability can leads to account takeover.
The company fixed the vulnerability and rewarded me💲💲💲.
.png)
 1 year ago
111
1 year ago
111 













 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·