BOOK THIS SPACE FOR AD
ARTICLE AD- 7h3h4ckv157
Disclaimer:
This article is intended for educational purposes only. It is crucial to accentuate that any attempt to exploit or manipulate followers on any social media platform is unethical and against the terms of service. The purpose of this article is to increase awareness and understanding of potential security concerns, rather than encourage or endorse any malicious activities. Always prioritize ethical behavior and respect the guidelines and policies set forth by social media platforms.
I suggest you to read this similar blog about: Hacking the Like Functionality of Twitter!
Note:
This article, written by myself, is published on “HACKLIDO” to fostering knowledge-sharing and learning within the cybersecurity community. The content will be the same, I just want to share my writes on this platform too. So let’s start…
Hey, Infosec!
I extend a warm “Hai” to each and every one of you. Prepare to embark on an intellectual journey that will unravel the enigmatic nuances of manipulating follower counts, while shedding light on the often overlooked caching issues and race conditions that lie at the intersection of innovation and risk.
In this article, we invite you to delve into the hidden side of Twitter’s follower ecosystem, where reputations are forged and shattered with a mere numerical fluctuation.
Discover the astonishing power of seemingly innocuous vulnerabilities that, when harnessed deftly, can accelerate your follower count to unprecedented heights. Be prepared to challenge your perception of conventional growth strategies as we unravel the intertwined relationship between security risks and strategic exploits. Uncover the hidden dangers that lurk beneath the surface, while also exploring the remarkable opportunities that await those who dare to venture into uncharted territory. So, fasten your seatbelts and embark on this gripping expedition, where knowledge and innovation collide, and the path to success is paved with security-aware growth.
Let us unravel the secrets of Twitter’s follower ecosystem together and empower ourselves with the wisdom to navigate its complexities safely. Within the realm of social media, where the numerical value of followers possesses the capability to either establish or dismantle one’s reputation, it comes as no surprise that both individuals and businesses are ceaselessly in pursuit of innovative strategies to augment their presence on Twitter. Yet, what if I were to disclose that an ostensibly innocuous race condition, when coupled with a caching predicament, could give rise to a substantial security hazard, while concurrently serving as a conduit for swiftly multiplying one’s follower count?
Prepare to embark on an engrossing expedition into the concealed facets of Twitter growth manipulation, where the intersection of vulnerabilities pertaining to security and adroit maneuvers intertwines seamlessly. Throughout the course of this article, we shall plunge deep into the captivating realm wherein caching predicaments and race conditions collide, thereby illuminating the inherent perils and prospects that they present. Steel yourself for an enlightening odyssey through the intricate domain of Twitter’s security and expansion, where comprehensive awareness of the associated risks shall endow you with the ability to harness them to your advantage. Ready yourself to uncover the enigmatic secrets concealed beneath the surface of Twitter’s follower ecosystem, and in doing so, acquaint yourself with the means to traverse this terrain with prudence, all the while accomplishing remarkable growth.
In order to gain a deeper comprehension of the intricate technical aspects associated with harnessing race conditions to augment the number of Twitter followers, let us meticulously deconstruct the process in a step-by-step manner.
Account Creation:Initiating the procedure entails the establishment of a Twitter account, necessitating the provision of requisite particulars such as username, email address, and password. Upon successful creation of the account, progression to the subsequent phase becomes feasible.Intercepting the Request:
To exploit the vulnerability inherent in race conditions, it becomes imperative to intercept the request generated upon the activation of the “Follow” button. This feat can be accomplished through the utilization of diverse interception tools such as Burp Suite. Through the act of capturing the request, we acquire the capability to scrutinize and manipulate its parameter (In this case: User-Agent Header).Burp’s Turbo Intruder for Race Condition:
Turbo Intruder assumes the guise of an immensely potent tool, endowed with the capacity to facilitate race condition attacks. It bestows upon us the ability to dispatch an abundance of concurrent requests, with slight differentiation, thereby instigating an environment conducive to race conditions. By capitalizing on the capabilities of Turbo Intruder, we engender a sequence of follow requests, dispatched in swift succession.Exploiting the Race Condition:
With Turbo Intruder in full operation, we unleash an onslaught of follow requests, all aimed at a singular user. Our primary objective resides in exploiting the vulnerabilities harbored within Twitter’s follower mechanism, as a result of race conditions. In the realm of race conditions, the behavior of the system becomes enigmatic and unpredictable, engendered by the concurrent access of shared resources by multiple processes or threads.Increasing Follower Count:
As the race condition unfurls, the tally of followers affiliated with the target user may undergo sudden and unforeseen increments. This phenomenon manifests due to the race condition’s capacity to disrupt the customary flow of follower updates, circumventing certain verification or safeguards established.Monitoring and Assessing Results:
Vigilantly monitoring the follower count throughout and subsequent to the race condition assault assumes paramount importance. This endeavor grants us the means to gauge the efficacy of our exploit, thereby ascertaining the extent of the follower increment. By meticulously scrutinizing the outcomes, we facilitate an evaluation of the triumphs derived from our approach, thereby potentially refining the process to enable further experimentation
It bears emphasizing that exploiting race conditions for personal gains, such as artificially inflating follower counts, represents a transgression of platform policies and ethical principles. The aforementioned exposition serves solely as an exploration of the technical underpinnings pertaining to this concept, devoid of any endorsement or encouragement of such activities.
Proof Of Concept:
You can see the increment in Followers countIt remains of utmost importance to prioritize ethical conduct, duly respecting the terms of service delineated by social media platforms, thereby upholding a secure and safeguarded online environment.
Twitter team’s opinion regarding the race condition:
“We appreciate your interest in the Twitter program and your commitment to security. However, we kindly request that you review our program policy prior to disclosing any vulnerabilities. It is important to note that the behavior you have reported falls under the out-of-scope category outlined in our policy for the following reason:
Manipulation of "likes/follows/views" count due to caching issues. We acknowledge that certain statistics on our platform may occasionally display inaccurate figures temporarily when a significant number of requests are submitted within a short time frame. This occurrence can be attributed to caching, where data is temporarily stored for efficiency purposes. The cached data may require some time to synchronize with the accurate back-end data store.
Consequently, we will categorize this report as informative, and while we appreciate your contribution, we encourage you to continue your bug hunting endeavors in other areas. We extend our best wishes for your future endeavors in the field of security.
Thank you for considering Twitter’s security and for your dedication to maintaining a secure platform.”
The Hidden Dangers: Unveiling the Deceptive Facade of Temporary Follower Counts
Although the temporary nature of the followers count may suggest a limited impact, attackers can still exploit this caching bug to their advantage. Let’s delve deeper into the intricacies of this vulnerability and its potential ramifications.
When attackers target the followers count through the race condition and caching issue, they exploit the window of inconsistency between the cached data and the accurate back-end data store. By bombarding the system with a flurry of follow requests, they disrupt the synchronization process, leading to momentary discrepancies in the displayed follower count.
While these discrepancies may seem transient, they can have significant implications. Attackers can leverage the sudden increase in follower count for various purposes, such as:
False Influence:A bloated follower count can create a deceptive perception of popularity and influence. By artificially inflating their follower numbers, attackers can masquerade as influential figures, thereby gaining unwarranted credibility and potentially manipulating public opinion.Social Engineering:
A high follower count can be a powerful tool for social engineering. Attackers can exploit the inflated count to deceive unsuspecting individuals or organizations, making fraudulent claims of influence or expertise. This can lead to trust violations, financial scams, or even unauthorized access to sensitive information.Reputational Damage:
In a world where follower counts often dictate reputation, a sudden surge in followers can impact an individual’s or business’s standing. Attackers may target competitors or adversaries, artificially boosting their follower counts and tarnishing their credibility by association with suspicious or illegitimate accounts.Monetization Opportunities:
A substantial follower count, even if temporary, can be monetized through sponsored content, endorsements, or brand collaborations. Attackers could exploit the inflated count to deceive potential advertisers or sponsors, capitalizing on the perceived reach and engagement to secure lucrative deals fraudulently.Manipulation of Trends:
Social media platforms rely on engagement metrics to determine trending topics and popular content. Attackers can exploit the inflated follower count to manipulate trending algorithms, artificially propelling certain topics or accounts to prominence, thereby influencing public discourse or perception.
It is important to recognize that the impact of exploiting this bug extends beyond mere numerical fluctuations. It encompasses reputational, social, and financial implications, eroding trust and distorting the authenticity of online interactions. By understanding the profound consequences, we emphasize the necessity for social media platforms to address and mitigate these vulnerabilities, safeguarding their users from exploitation and maintaining the integrity of their ecosystems.
Hence, despite the temporary nature of the followers count, attackers can exploit this bug to unleash a cascade of consequences that extend far beyond a mere numerical blip.
Conclusion
We embarked on a fascinating journey into the realm of Twitter hacking, where the convergence of security risks and clever tactics intertwines. We explored the race condition vulnerability and its interplay with caching issues, shedding light on how attackers can manipulate the temporary nature of follower counts for their own gain. While the temporary nature of these inflated follower counts may seem harmless at first glance, the impact can be far-reaching and insidious. Attackers can exploit these moments of discrepancy to deceive, manipulate, and exploit unsuspecting users. From false influence to reputational damage, social engineering to trend manipulation, the consequences are far from trivial.
It is crucial for social media platforms like Twitter to address and mitigate these vulnerabilities, ensuring the integrity and trustworthiness of their systems. Robust security measures, continuous monitoring, and prompt response to potential threats are essential in safeguarding users from exploitation and maintaining a safe online environment. As users, we must remain vigilant, skeptical of sudden spikes in follower counts, and mindful of the potential risks lurking beneath the surface. Understanding the intricacies of these vulnerabilities empowers us to navigate the social media landscape with caution, distinguishing between genuine influence and deceptive manipulation.
In the pursuit of growth and success, let us prioritize ethical practices, respecting the policies and guidelines set forth by social media platforms. Together, we can create an online ecosystem where authenticity, trust, and meaningful connections thrive. Remember, the true measure of influence lies not in the numbers, but in the quality of engagements, genuine connections, and the positive impact we create in the digital realm. Let us strive for a responsible and secure social media landscape, where integrity prevails and true influence shines through.
I trust that you have derived some measure of satisfaction from perusing this write-up, and I shall endeavor to furnish you with another engaging and thought-provoking composition in the not-too-distant future.
I invite you to share your valuable insights and perspectives on this topic. Your contribution will enrich the ongoing discussion on this issue. Thank you for your engagement, and I look forward to connecting with you on social media. Click here to connect with me → 7h3h4ckv157
Connect through TwitterConnect through LinkedIn.png)
 1 year ago
116
1 year ago
116 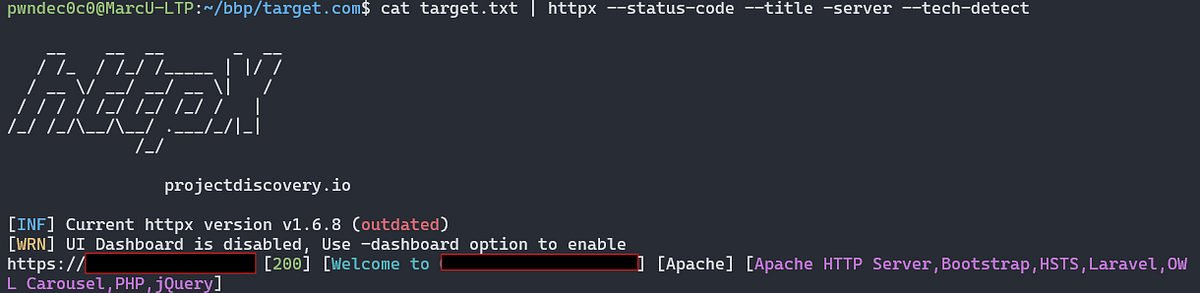













 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·