BOOK THIS SPACE FOR AD
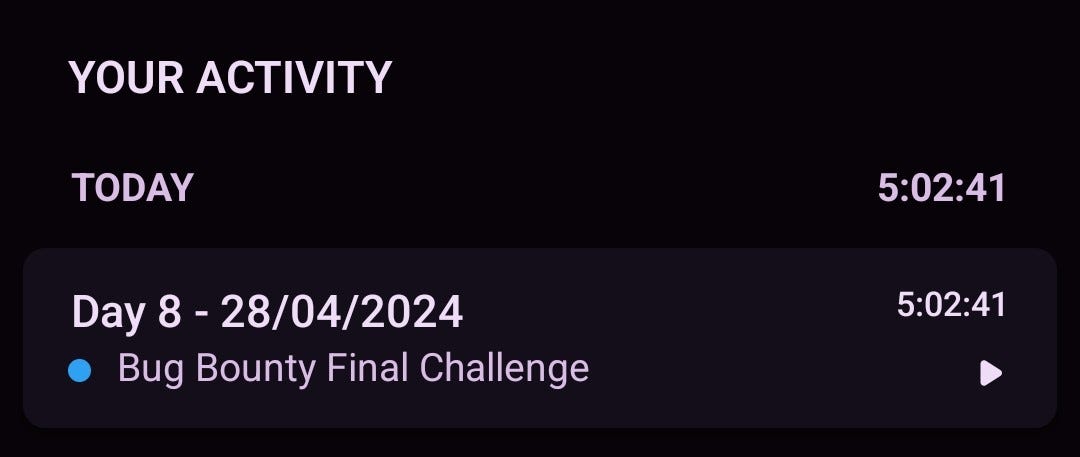
ARTICLE ADFirst of all the scope it was small Just a Login Page
1 — So The first thing that came to my mind Directory Brute Force
- Unfortunately, I didn’t get anything
2- I Tried For , SQLI , user enumeration , Brute force protection , Defautl Credentials , etc .
- But also, unfortunately, I didn’t get anything
But I said let me check parameter’s So I start for Parameter enumeration
So I found a Parameter Call [ ?Locale ] ,
What Is XSS ? https://portswigger.net/web-security/cross-site-scripting
So I Start Testing For XSS and Then I put a Normal Payload [ “>Test ] To see if it is reflected on the Source Code , But unfortunately I Faced this When I Try Open The Source Code
After attempts I found when I Put [ </script > In The Parameter There is code reflected on the page Like This >
Then I said sure there is an interaction with the code, let me put a payload [ </script> <script>alert(“omar”)</script> ]
But I said 100 percent that I will take a duplicate ):
I was surprised when the report was answered. It is not duplicate !
Takeaways :
1- Don’t Give up
2- take a brake And come back with stronger ideas
.png)
 1 year ago
86
1 year ago
86 












 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·