BOOK THIS SPACE FOR AD
ARTICLE AD27. January 2022
This article has been indexed from
Help Net Security
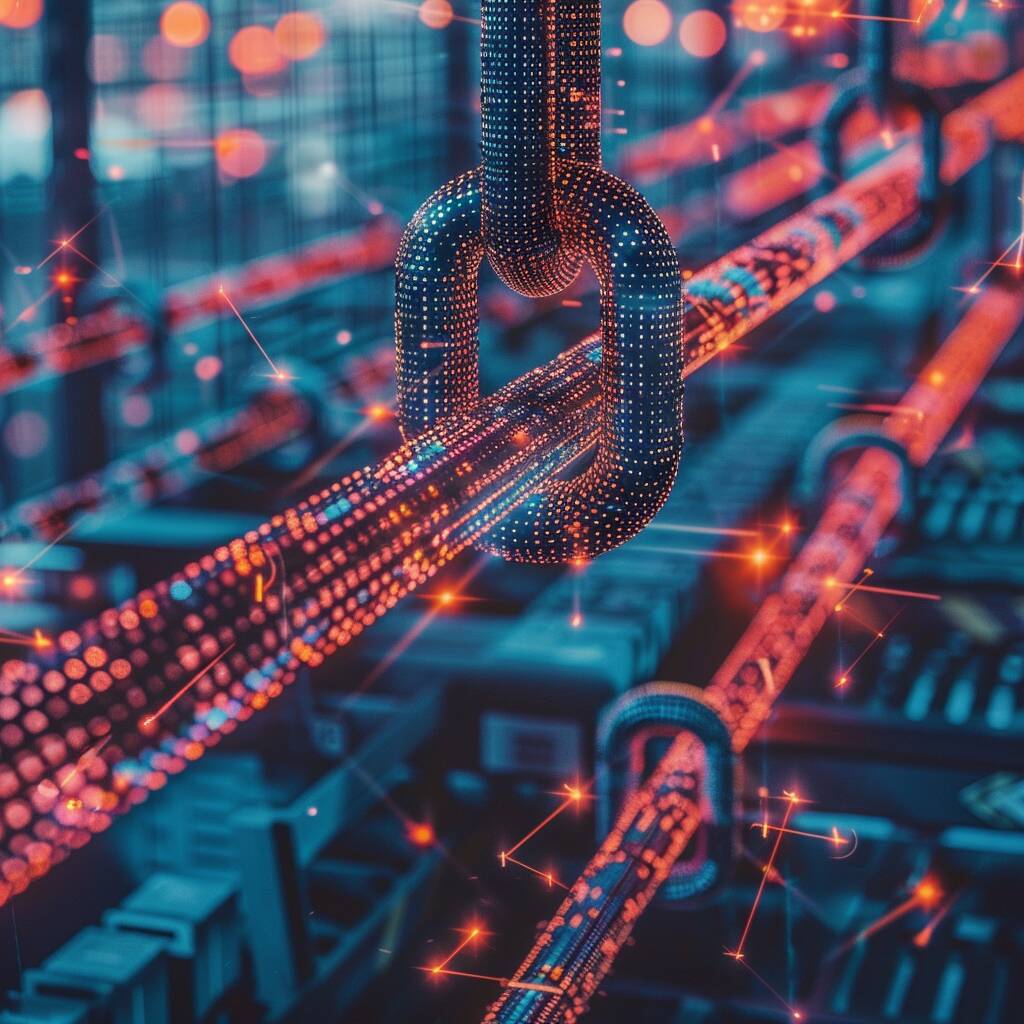
There is a seemingly trivial solution to any remote code execution attack, namely: do not to let the inbound traffic match the pattern that triggers the vulnerability of the server. Easy to say, but hard to do. There are almost endless variations of traffic patterns that could trigger the critical severity Log4j vulnerability. As a result, malicious patterns of inbound traffic are extremely hard to detect. At the same time, outbound traffic caused by a … More →
The post How would zero trust prevent a Log4Shell attack? appeared first on Help Net Security.
Read the original article:
.png)












 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·