BOOK THIS SPACE FOR AD
ARTICLE AD
Thousands of pedophiles who download and share child sexual abuse material (CSAM) were identified through information-stealing malware logs leaked on the dark web, highlighting a new dimension of using stolen credentials in law enforcement investigations.
The novel use of the dataset was conducted by Recorded Future's Insikt Group, who shared a report explaining how they identified 3,324 unique accounts that accessed illegal portals known for distributing CSAM.
By leveraging other data stolen from the target, Insikt analysts could track those accounts to usernames on various platforms, derive their IP addresses, and even system information.
This information gathered by the Insikt Group has been shared with law enforcement to unmask the identities of these individuals and proceed to arrests.
Using stealer logs for good
A stealer log is a collection of data stolen from a particular individual by information-stealing malware, such as Redline, Raccoon, and Vidar, from infected systems.
When these types of malware are executed on a device, they collect credentials, browser history, browser cookies, autofill data, cryptocurrency wallet information, screenshots, and system information.
The information is then packaged into an archive called a "log," which is then transmitted back to the threat actor's servers.
Threat actors can then use these stolen credentials to breach further accounts, conduct corporate attacks, or sell them to other cybercriminals on the dark web, Telegram, and other platforms. Due to their size and number, these logs are rarely scrutinized and categorized but rather sold in bulk.
Previous analysis has shown that information-stealer logs can contain crucial business account data or credentials to accounts that can expose proprietary information.
As this type of malware is commonly distributed via pirated software, malvertising, and fake updates, they can siphon data from infected systems for extended periods without the victim realizing it.
This includes CSAM users who, without their knowledge, expose all of the credentials for their online banking, email, and other legitimate accounts, as well as the account credentials used for accessing CSAM sites that require registration.
Identifying CSAM consumers
Insikt analysts used infostealer logs captured between February 2021 and February 2024 to identify CSAM consumers by cross-referencing stolen credentials with twenty known CSAM domains.
They then removed duplicates to narrow the results to 3,324 unique username-password pairs.
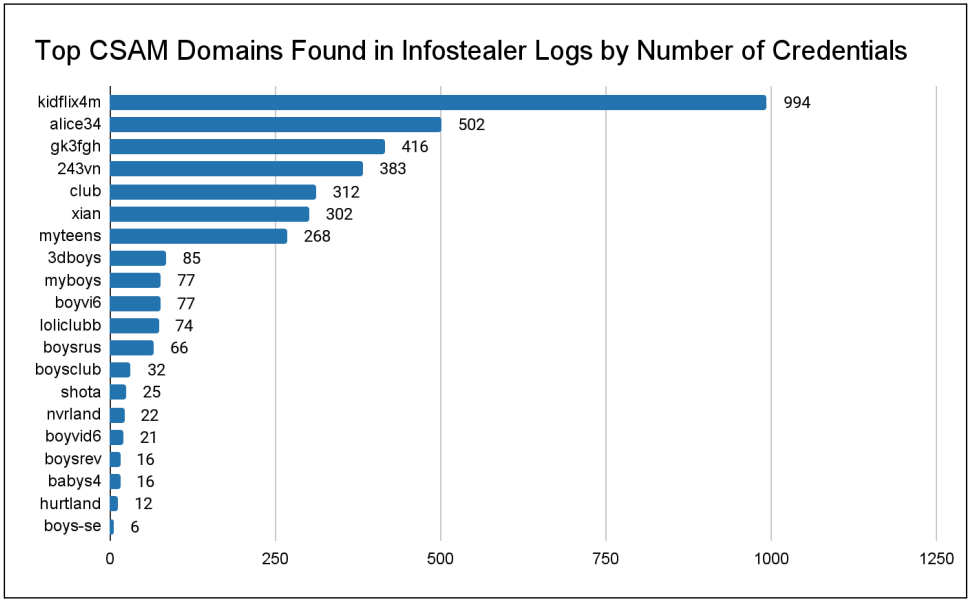 Accounts linked to known CSAM sites
Accounts linked to known CSAM sitesSource: Recorded Future
As information-stealing malware steals all credentials saved in a browser, the researchers were able to link CSAM account holders to their legal online accounts, such as email, banking, online shopping, mobile carriers, and social media.
They then used open-source intelligence (OSINT) and digital artifacts to gather more revealing information about those users. These clues include:
Cryptocurrency wallet addresses and transaction histories. Non-CSAM web accounts and browsing history. Physical addresses, full names, phone numbers, and email addresses extracted from browser autofill data. Associations with various online services, such as social media accounts, government websites, and job application portals.Recorded Future's report highlights three cases of identified individuals, summarized as follows:
"d****" - Cleveland, Ohio resident previously convicted for child exploitation and registered as a sex offender. Maintains accounts on at least four CSAM sites. "docto" – Illinois resident who volunteers at children's hospitals and has a record for retail theft. Maintains accounts on nine CSAM websites. "Bertty" – Likely a Venezuelan student who maintains accounts on at least five CSAM sites. Cryptocurrency transaction history implicates the user with the potential purchase and distribution of CSAM content. Docto's profile as reconstructed by infostealer log analysis
Docto's profile as reconstructed by infostealer log analysisSource: Recorded Future
Insinkt's analysis highlights the potential of infostealer data in aiding law enforcement to track child abuse tracking and prosecute individuals.
.png)















 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·