The Iranian-origin threat actor known as Charming Kitten has been linked to a new set of attacks aimed at Middle East policy experts with a new backdoor called BASICSTAR by creating a fake webinar portal.
Charming Kitten, also called APT35, CharmingCypress, Mint Sandstorm, TA453, and Yellow Garuda, has a history of orchestrating a wide range of social engineering campaigns that cast a wide net in their targeting, often singling out think tanks, NGOs, and journalists.
"CharmingCypress often employs unusual social-engineering tactics, such as engaging targets in prolonged conversations over email before sending links to malicious content," Volexity researchers Ankur Saini, Callum Roxan, Charlie Gardner, and Damien Cash said.
Last month, Microsoft revealed that high-profile individuals working on Middle Eastern affairs have been targeted by the adversary to deploy malware such as MischiefTut and MediaPl (aka EYEGLASS) that are capable of harvesting sensitive information from a compromised host.
The group, assessed to be affiliated with Iran's Islamic Revolutionary Guard Corps (IRGC), has also distributed several other backdoors such as PowerLess, BellaCiao, POWERSTAR (aka GorjolEcho), and NokNok over the past year, emphasizing its determination to continue its cyber onslaught, adapting its tactics and methods despite public exposure.
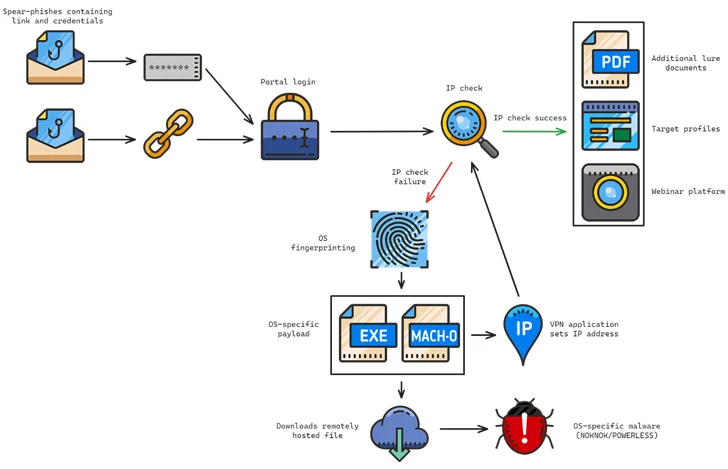
The phishing attacks observed between September and October 2023 involved the Charming Kitten operators posing as the Rasanah International Institute for Iranian Studies (IIIS) to initiate and build trust with targets.
The phishing attempts are also characterized by the use of compromised email accounts belonging to legitimate contacts and multiple threat-actor-controlled email accounts, the latter of which is called Multi-Persona Impersonation (MPI).
The attack chains typically employ RAR archives containing LNK files as a starting point to distribute malware, with the messages urging prospective targets to join a fake webinar about topics that are of interest to them. One such multi-stage infection sequence has been observed to deploy BASICSTAR and KORKULOADER, a PowerShell downloader script.
BASICSTAR, a Visual Basic Script (VBS) malware, is capable of gathering basic system information, remotely executing commands relayed from a command-and-control (C2) server, and downloading and displaying a decoy PDF file.
What's more, some of these phishing attacks are engineered to serve different backdoors depending on the machine's operating system. While Windows victims are compromised with POWERLESS, Apple macOS victims are targeted with an infection chain culminating in NokNok via a functional VPN application that's laced with malware.
"This threat actor is highly committed to conducting surveillance on their targets in order to determine how best to manipulate them and deploy malware," the researchers said. "Additionally, few other threat actors have consistently churned out as many campaigns as CharmingCypress, dedicating human operators to support their ongoing efforts."
The disclosure comes as Recorded Future uncovered IRGC's targeting of Western countries using a network of contracting companies that also specialize in exporting technologies for surveillance and offensive purposes to countries like Iraq, Syria, and Lebanon.
The relationship between intelligence and military organizations and Iran-based contractors takes the form of various cyber centers that act as "firewalls" to conceal the sponsoring entity.
They include Ayandeh Sazan Sepher Aria (suspected to be associated with Emennet Pasargad), DSP Research Institute, Sabrin Kish, Soroush Saman, Mahak Rayan Afraz, and the Parnian Telecommunication and Electronic Company.
"Iranian contracting companies are established and run by a tight-knit network of personas, who, in some cases, represent the contractors as board members," the company said. "The individuals are closely associated with the IRGC, and in some cases, are even representatives of sanctioned entities (such as the IRGC Cooperative Foundation)."
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.
.png)
 9 months ago
128
9 months ago
128 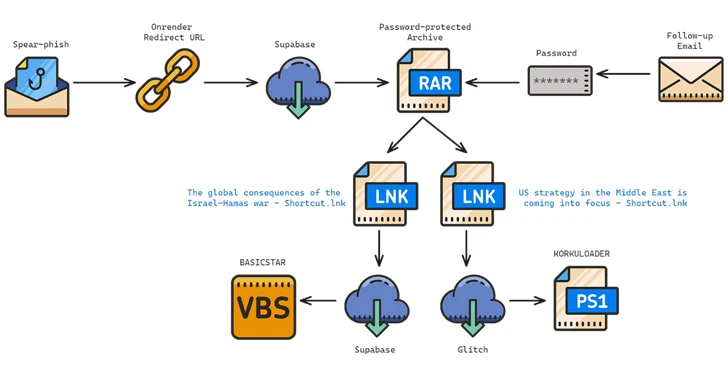

















 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·