BOOK THIS SPACE FOR AD
ARTICLE AD17. July 2021
Threat Actors are Working Together. Defenders Should Collaborate Too!
XKCD ‘Board Game Argument: Legacy’
It’s Time to Issue Company Passwords Again
The Importance Of Protecting Your App’s Source Code
The Internet of Things Ongoing Directions
Google issues patches for Chrome flaw for Windows, Mac and Linux
Critical Chrome 0-Day Vulnerability Exploited in Wide – Update Your Chrome Now!!
How Can CCSP Certification Help Your Organization?
Russia Based Company, DDoS – Guard gets Targeted by Cybercriminals
Toddler Android Banking Malware Spreads Across Europe
SpearTip: New Diavol Ransomware Does Steal Data
US govt offers $10 million reward for info on nation-state cyber operations
Biden Puts a $10M Bounty on Foreign Hackers
$10 Million US Dollars, Missing Ransomware Gangs, and so much more!
China’s New Law Requires Researchers to Report All Zero-Day Bugs to Government
Private Internet Access deal: Get two years on up to 10 devices for just $70
Top Stories: Apple Debuts MagSafe Battery Pack, iOS 15 Beta 3, and More
How the U.S. became the world’s new bitcoin mining hub
Instagram Launches ‘Security Checkup’ to Help Users Recover Hacked Accounts
CloudFlare CDNJS Bug Could Have Led to Widespread Supply-Chain Attacks
Cisco fixes high-risk DoS flaw in ASA, FTD Software
One Year After Europe’s Schrems II Decision, Privacy Activist Bemoans Lack of Progress
The Notorious REvil Ransomware Gang Go Offline
Biden’s Cybersecurity Team Gets Crowded at the Top
Stop Google tracking your location
D-Link issues beta hotfix for multiple flaws in DIR-3040 routers
BASE85 Decoding With base64dump.py, (Sat, Jul 17th)
WooCommerce Patched a Bug that Threatened Databases of Prominent Sites
‘Build’ or ‘Buy’ your own antivirus product
To My Fellow CEOs: Cyber Security is your Business Too!
Essential Features of Advanced Endpoint Security for Businesses
Six Steps to Protect Your Organization from Ransomware | #RansomwareWeek
The eSIM technology stimulates the growth of the IoT market in Russia
NS1 Traffic Analysis Dashboards provide visibility into application delivery at the edge
NewgenONE: A digital transformation platform that simplifies complex business processes
Vacationing? How to avoid the cybersecurity blues
Google patches Chrome zero‑day vulnerability exploited in the wild
Week in security with Tony Anscombe
Kaseya attack: How ransomeware attacks are like startups and what we need to do about that
What is a PCI Audit? And How to Get Your Business Ready
Amazon asked Apple to remove an app that spots fake reviews, and Apple agreed
AI and financial processes: Balancing risk and reward
Aerospike expands Accelerate Partner Program to speed up partner ramp to revenue
Red Hat renews FIPS 140-2 security validation for Red Hat Enterprise Linux 8.2
SecurEnds raises $21M to scale operations and product development
OmniSci promotes Pey Silvester to VP of Engineering
Apple Donating to Flood Relief Efforts Across Germany, Belgium and The Netherlands
John Zissimos joins Okta as Chief Digital Officer
Kaseya ransomware attack should be a wake-up call to all of us, expert says
Kaseya attack: “Yes, we can do something about this, and we should do something about this”
Hackers Got Past Windows Hello by Tricking a Webcam
‘Fakespot’ Removed From Apple’s App Store After Complaint From Amazon
IT Security News Daily Summary 2021-07-16
SolarWinds hackers exploited iOS 0-day to compromise iPhones
How disinformation monitoring helps agencies break down attacks
Fixing ‘concept drift’: Retraining AI systems to deliver accurate insights at the edge
Top CVEs Trending with Cybercriminals
Linux Variant of HelloKitty Ransomware Targets VMware ESXi Servers
iOS 15’s Focus Mode Helps You Stay on Task
Right or Left, You Should Be Worried About Big Tech Censorship
Common Security Lapses That Empower Cybercriminals
Researchers Create New Approach to Detect Brand Impersonation
Bad bot activity on sports betting websites rises during Euro 2020
How to leverage accountability to ensure sustainable enterprise data security
An Overall Philosophy on the Use of Critical Threat Intelligence
How to install SELinux on Ubuntu Server 20.04
New LinkedIn phishing campaign found using Google Forms
3 Myths About Threat Actors and Password Safety
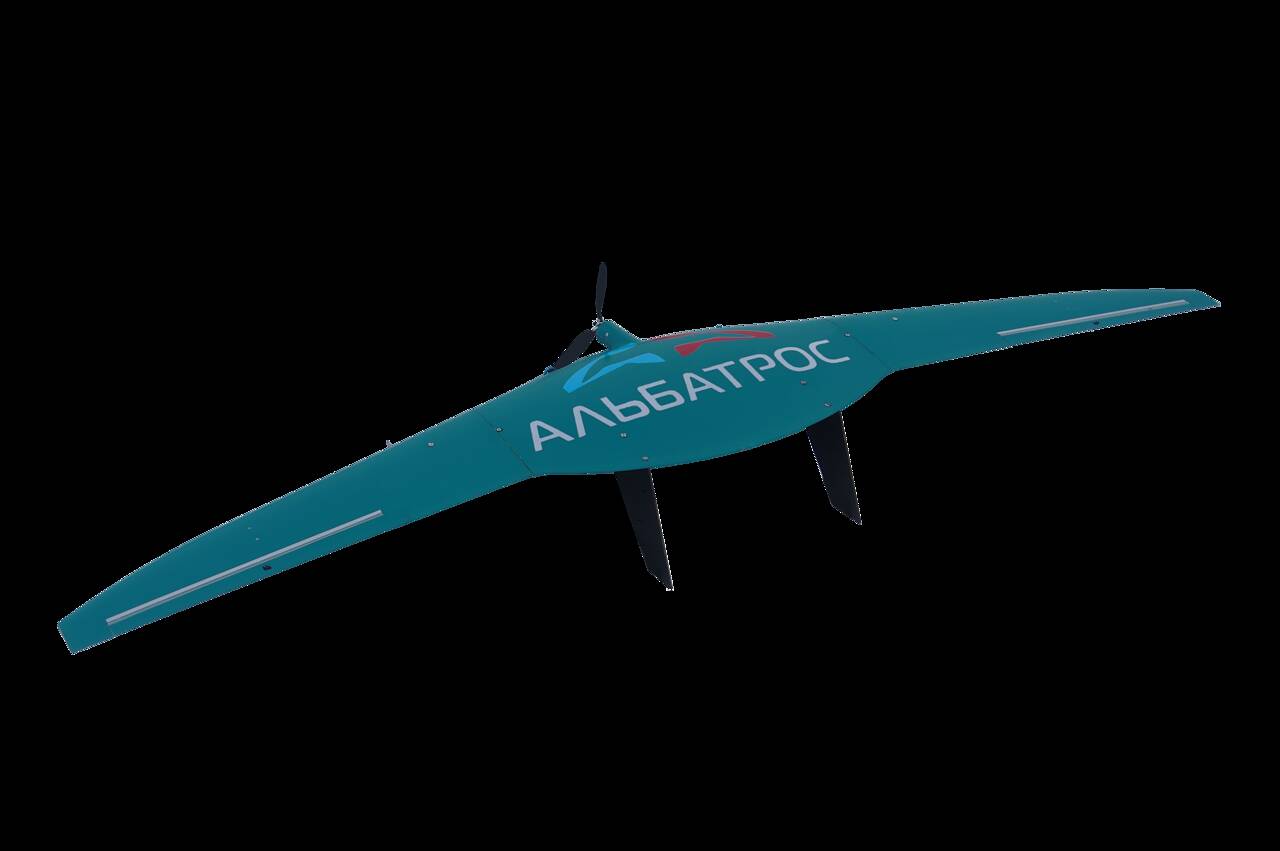
FAA seeks best practices for drone-based infrastructure inspections
NSF seeks partners for blockchain business programs
The number of false positive security alerts is staggering. Here’s what you can do to reduce yours
Cybersecurity News Round-Up: Week of July 16, 2021
With 5G coming, it’s time to plug security gaps
Tesla “Recalls” Vehicles in China due to Safety Glitch
5 #TrendTips for Open Source Security
Main Considerations for Securing Enterprise 5G Networks
This Week in Security News – July 16, 2021
How To Manage a Remote Workforce So as To Protect Them From Cyber Threats
Kaseya victim struggling with decryption after REvil goes dark
This npm Package Could Have Brought Down Cloudflare’s Entire CDN and Millions of Websites
What’s at Stake When the Transportation Sector Lags Behind in Cybersecurity
Some Apple Stores Decorated in Flag Colors to Celebrate New International Apple Watch Bands
What Cops Understand About Copyright Filters: They Prevent Legal Speech
How to configure SSL/TLS for a Http Client or a Server
Deals: AirPods Max Hit $100 Off for the First Time, Get All Colors at $449
Recent Attacks Lead to Renewed Calls for Banning Ransom Payments
MacRumors Giveaway: Win a Luna Display Adapter to Turn an iPad or Mac Into a Second Screen
Targeted Phishing Attack against Ukrainian Government Expands to Georgia
Congress might not clear defense spending, policy bills until December
IoT Attacks Increased 700% in just over Two Years
Australian Organizations Spent $55 Million in Ransom Payments
Defcon Talk Prompts New Windows Print Spooler Flaw Warning
Apple Seeds Second Public Betas of iOS 15, iPadOS 15, tvOS 15, and watchOS 8
Apple Releases Second Public Beta of macOS 12 Monterey
Don’t Let Police Arm Autonomous or Remote-Controlled Robots and Drones
Critical Juniper Bug Allows DoS, RCE Against Carrier Networks
Israel Launches Anti-Ransomware Campaign to Prevent Cyberattacks
State Department Pays up to $10M for Information on Foreign Cyberattacks
Apple Seeds Second Public Betas of iOS 15 and iPadOS 15
Will China Retaliate Against U.S. Chip Sanctions?
REvil Ransomware Uses DLL Sideloading
Cisco Patches High-Risk Flaw in ASA, FTD Software
Kremlin Does Not Know Why All Websites Linked to Hacker Group REvil Are Down
ClearDATA Announces Support for AWS for Health Initiative
Are you READY for (ISC)² Security Congress?
DoD Adds Two More (ISC)² Certifications to Requirements for Cybersecurity Staff
Six existential threats posed by the future of 5G (Part Two)
Cyber Insurers Might Be Making the Ransomware Problem Worse
Banks now rely on a few cloud computing giants. That’s creating some unexpected new risks
Wanted: State-backed bandits planning cyberattacks on US infrastructure. Reward: $10m
Apple Watch Chief Kevin Lynch to Work on Apple Car Development
Ransomware threat to SonicWall Customers
BrandPost: Achieving Zero Trust with Network Data
BrandPost: How a Higher-Ed Institution Validates Security Incidents in Minutes with ExtraHop
BrandPost: ExtraHop Contributes Network Security Expertise to MITRE ATT&CK Framework
US offers huge reward in fight against state-sponsored cybercriminals
Windows 0-Days Used Against Dissidents in Israeli Broker’s Spyware
Critical WooCommerce Vulnerability Targeted Hours After Patch
Google: New Chrome Zero-Day Being Exploited
More PrintNightmare: “We TOLD you not to turn the Print Spooler back on!”
LogRhythm is a Nine-Time Gartner SIEM Magic Quadrant Leader
Stalkers: ‘Ugly Truth’ of Facebook Staff Abusing Private Data
How can we get rid of them and why law enforcement is not really the answer
Here are the Top Online Scams You Need to Avoid Today
A procurement paradigm for digital government
Biden’s executive order on federal workforce equity: What happens next
4 healthcare risk management tips for secure cloud migration
Want to earn $10 million? Snitch on a cybercrook!
Fashion Retailer Guess Confirms Data Breach
Google Releases Security Updates for Chrome
Cisco Releases Security Updates
Deals: Get the HomePod Mini for $89.99 at B&H Photo ($9 Off)
iPhone 12 Depreciates Less Than iPhone 11, Study Finds
Forefront Dermatology Data Breach Affects 2.4 Million Patients
Fraudsters siphoned off unemployment benefits from recipients in the throes of the pandemic
Why the Fed hates cryptocurrencies and especially stablecoins
Critical Vulnerabilities Spotted In WordPress Plugin Frontend File Manager
Artwork Archive cloud storage misconfiguration exposed user data
Fastest VPN 2021: Top services tested and compared
Palo Alto Networks’ Unit 42 Publishes Report on Mespinoza Group
4 Future Integrated Circuit Threats to Watch
Microsoft alerts about a new Windows Print Spooler vulnerability
Microsoft: New Unpatched Bug In Windows Print Spooler
Hooking Candiru: Another Mercenary Spyware Comes Into Focus
Chinese APT LuminousMoth Abuses Zoom Brand For Gov’t Attacks
U.S. Gov’t Offers $10 Million For Info On Hackers Targeting Infrastructure
U.S. Customs Seizing Record Numbers of Counterfeit Wireless Headphones Since AirPods Pro Launched
COVID-19 Vaccine Passports: 5 Security Tips for You and Your Family
The Security Threat of Voice Cloning | Avast
When ‘Later’ Never Comes: Putting Small Business Cybersecurity First
Vulnerabilities in Etherpad Collaboration Tool Allow Data Theft
Google Adds HTTPS-First Mode to Chrome
How to Attract More Computer Science Grads to the Cybersecurity Field
3 reasons to use network diagram software
Hackers Could Locally Exploit a New Windows Spooler Vulnerability
A Cryptomining Farm Was Discovered in Ukraine
Popular Fashion Seller Guess Alerts Its Clients Over Possible Data Breach
Artwork Archive cloud storage misconfiguration exposed user data, revenue records
Apple Arcade Gets Three New Classics, Including Angry Birds Reloaded
IoT Malware Infections Increased by 700% Amid COVID-19 Pandemic
Hackers Can Locally Exploit a New Windows Spooler Vulnerability and Gain System Privileges
Google Parts Ways With Cloudera Cofounder – Report
Securiti allies with Snowflake to manage and secure data
Leveraging API Hooking for code deobfuscation with Frida
Toddler mobile banking malware surges across Europe
Microsoft: New Unpatched Bug in Windows Print Spooler
Jihadist content targeted on Internet Archive platform
Google Chrome 91.0.4472.164 fixes a new zero-day exploited in the wild
The HelloKitty Ransomware Linux Version Targets VMware ESXi Servers
Biden Administration announces flurry of new anti-ransomware efforts
WhatsApp Tests Message Sending Without Smartphone
UK Spy Agency Releases Annual Threat Report
Israeli Firm Helped Governments Target Journalists, Activists with 0-Days and Spyware
Social Security Numbers Exposed Following Tulsa Ransomware Attack
WooCommerce Fixes Bug Affecting Millions of WordPress Websites
DevilsTongue Spyware Targets Windows Zero-Day Vulnerabilities
Does using a VPN slow down your Internet?
Battery Gigafactory Planned For Coventry
Check Point Software named a “Champion” in Global Security Leadership Matrix 2021
Chinese APT LuminousMoth abuses Zoom brand to target gov’t agencies
Several Vulnerabilities Patched in ‘MDT AutoSave’ Industrial Automation Product
Trump Hacker and Friends on a Mission to Fix the Internet
Threat Actors Use Marvel’s Black Widow Movie To Spread Malware
25 Free & Open Source Cybersecurity Tools for Businesses
Addressing User Access in IT Security Compliance
OneLogin Eases Adoption of Zero Trust Framework with Delegated Administration
Asian Government Entities Targeted by Chinese Cyberspies in APT Campaign
The 15 biggest data breaches of the 21st century
Move over XDR, it’s time for security observability, prioritization, and validation (SOPV)
Child trafficking: 92 minor victims identified across Europe
Facebook Suspends Accounts Used by Iranian Hackers to Target US Military Personnel
New enhanced Joker Malware samples appear in the threat landscape
Twitter Testing New Edge-to-Edge Timeline Layout for Photos, Surveys Users on Ability to Edit Tweets
U.S. Government sets up ransomware task force, offers $10 million reward for info
Microsoft points the finger at Israeli spyware seller for DevilsTongue attacks
1.2 Million People Affected by Practicefirst’s Supply Chain Ransomware Breach
Multiple BaseXX Obfuscations, (Fri, Jul 16th)
Didi shares tank 7% after Chinese regulators visit the ride-hailing giant for cybersecurity review
Apple Holds Screening Event of ‘Ted Lasso’ Season Two Ahead of Global Premiere Next Week
Want your endpoint security product in the ‘Microsoft Consumer Antivirus Providers for Windows’ ?
May ransomware blight all the cyber stragglers and let God sort them out
Ask Chloé: Returning to the Office
Threat Modeling in the Age of Automation
New infosec products of the week: July 16, 2021
Chinese regulators from 7 departments visit Didi for cybersecurity review
15-Year-Old Linux Netfilter Vulnerability Let Hackers Bypass All Modern Security Mitigations
How to strike the balance between privacy and personalization in healthcare and beyond
A Tsunami of Cyber Crimes ejected by Australian Ransomware Payments
Morgan Stanley Customer Data accessed by hackers
Windows Print Spooler hit with local privilege escalation vulnerability
Update Your Chrome Browser to Patch New Zero‑Day Bug Exploited in the Wild
The rise of the Developer Experience Engineer, and why it matters
ESET: new generation viruses will be able to imitate human behavior
Microsoft Warns of New Unpatched Windows Print Spooler Vulnerability
Physical threats increase as employees return to the office
Security Evangelist or Zealot – Where to Draw the Line
(ISC)² Offers Free Access to Ransomware Education | #RANSOMWAREWEEK
How a man used a fake finger to trick his smartphone biometrics
57% of reported incidents are caused by insiders
Governance metrics lagging in ESG reporting across major organizations
Small Businesses Save Up to 60% in McAfee and Visa Partnership
Move to all-flash object storage to occur within five years
A brief guide on building audio and video live streaming platform
Are Your Employees’ Old Phone Numbers Creating Vulnerabilities?
Bug bounty platform urges need for firms to have vulnerability disclosure policy
Platform9 Managed KubeVirt unifies virtual machines and Kubernetes stacks
Strata Maverics Identity Discovery reduces cloud migration project times from months to hours
Sunlight Infrastructure Manager and Marketplace simplifies deployment of apps in edge environments
Spectral Logs enables additional layer to existing protection of code and data
Qrypt Quantum Data at Rest app offers secure data storage with one-time pad encryption
Sports events and online streaming: prepare your cybersecurity
GuidePoint Security expands its IAM consulting practice to reduce cyber risk
1Password Events API delivers real-time insight on password activity
Tech & Terrorism: Facebook Puts Onus On Users to Identify Extremism
Microsoft, Google, Citizen Lab blow lid off zero-day bug-exploiting spyware sold to governments
Securiti partners with Snowflake to enable protection of sensitive data in the Data Cloud
Kloudspot and Cisco Meraki help organizations offer safer and smarter workspace experiences
Build a data lakehouse to avoid a data swamp
Today’s Headlines and Commentary
Verge.io partners with CloudFabrix to provide data center transformation for organizations
Gas station owners sue Colonial Pipeline after ransomware attack
Generated on 2021-07-17 23:55:30.761624
By continuing to use the site, you agree to the use of cookies. more information
.png)











 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·