BOOK THIS SPACE FOR AD
ARTICLE AD
A leaked tool used by the Babuk Locker operation to create custom ransomware executables is now being used by another threat actor in a very active campaign targeting victims worldwide.
Babuk Locker was a ransomware operation that launched at the beginning of 2021 when it began targeting corporate victims and stealing their data in double-extortion attacks.
After performing an attack on Washinton DC's Metropolitan Police Department (MPD) and feeling the pressure from law enforcement, the ransomware gang shut down in April and switched to a non-encrypting data extortion model under the name PayLoad Bin.
Babuk Locker builder leaked
Last week, security researcher Kevin Beaumont discovered that someone uploaded the Babuk operation's ransomware builder to VirusTotal.
When BleepingComputer tested the builder, it was simplistic to generate a customized ransomware.
All a threat actor has to do is modify the enclosed ransom note to include their own contact info, and then run the build executable to create customized ransomware encryptors and decryptors that target Windows, VMware ESXi, Network Attached Storage (NAS) x86, and NAS ARM devices.
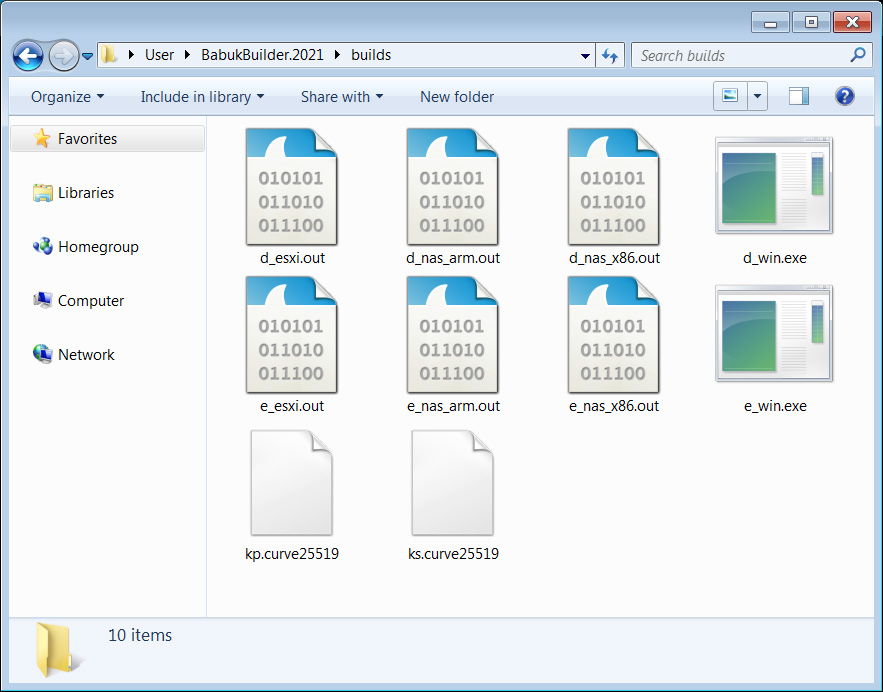 Using the builder to create a customized Babuk ransomware
Using the builder to create a customized Babuk ransomwareSource: BleepingComputer.com
Babuk builder used to launch new attacks
Soon after the builder was leaked online, a threat actor began using it to launch a very active ransomware campaign.
Starting on Tuesday, a victim reported on Reddit that they were hit by ransomware calling itself 'Babuk Locker.'
Security researcher MalwareHunterTeam also told BleepingComputer that ID Ransomware received a sharp spike in Babuk Locker submissions starting on June 29th. These victims are from all over the world, and the submitted ransom notes all contained the email address of the threat actor.
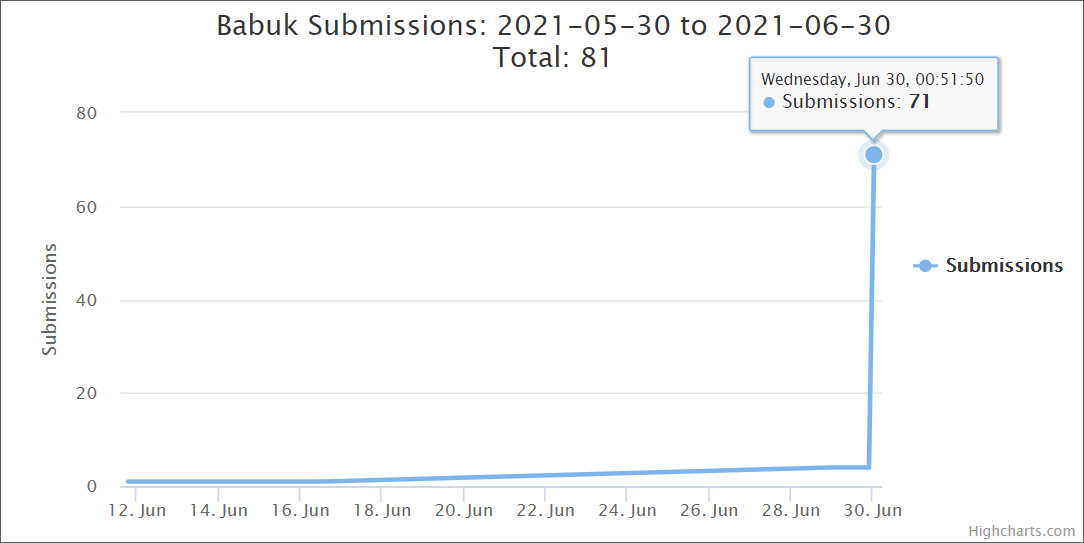 A sharp spike in Babuk Ransomware submissions to ID Ransomware
A sharp spike in Babuk Ransomware submissions to ID RansomwareLike the original operation, this ransomware attack adds the .babyk extension to encrypted file names and drops a ransom note named How To Restore Your Files.txt.
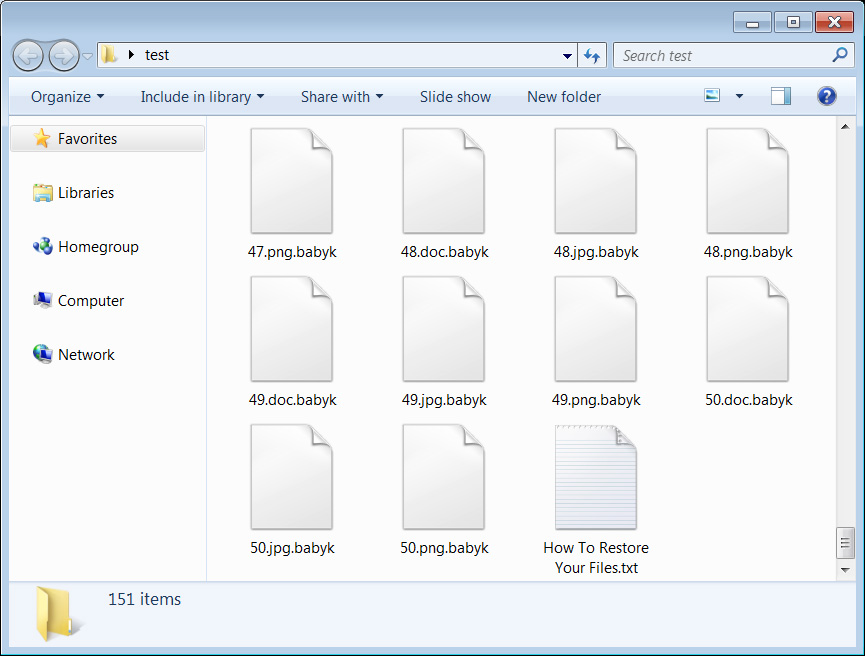 Files encrypted by Babuk Locker
Files encrypted by Babuk LockerSource: BleepingComputer
Compared to the original Babuk Ransomware operation that demanded hundreds of thousands, if not millions, of dollars to recover their files, this new threat actor is only asking for .006 bitcoins or approximately $210 from their victims.
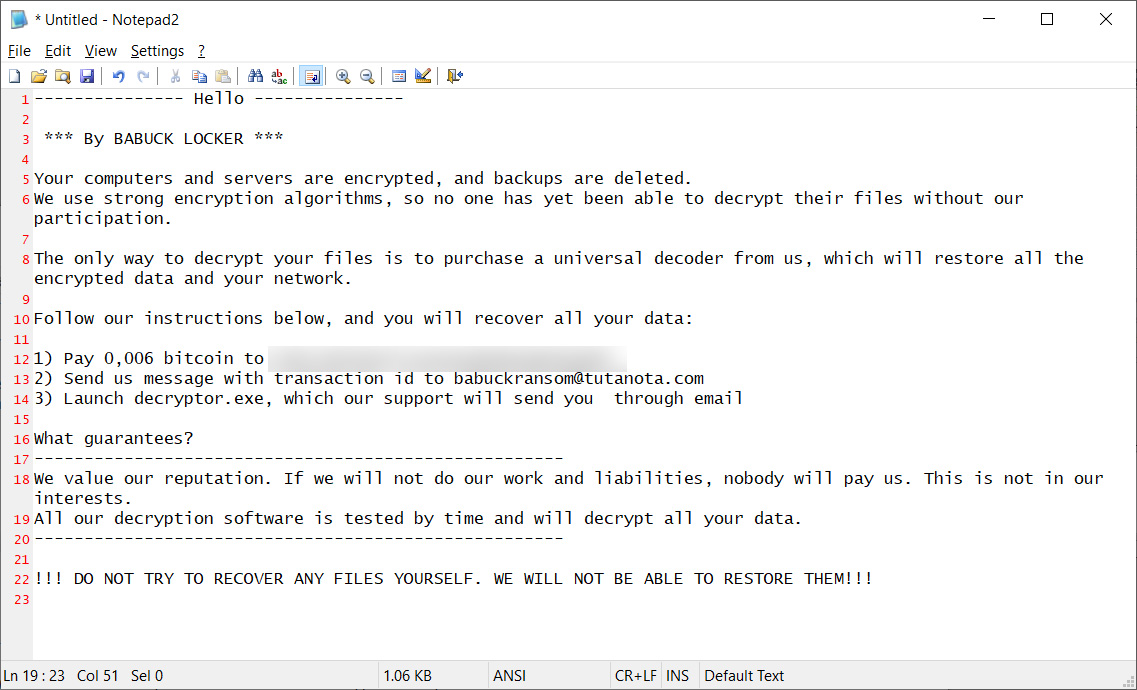 Ransom note from new Babuk ransomware attack
Ransom note from new Babuk ransomware attackSource: BleepingComputer
Another noticeable change is that the original Babuk Locker operation utilized a dedicated Tor payment site used to negotiate with victims. However, the new attacks are using email to communicate with victims through a babukransom@tutanota.com email address.
It is unclear how the ransomware is being distributed, but we have created a dedicated Babuk Locker support topic that victims can use to share more information about the attack.
If anyone pays the ransom demand for this new ransomware campaign, please let us know as we would like to ask you some private questions.
.png)














 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·