BOOK THIS SPACE FOR AD
ARTICLE ADIn an era where cyber threats are becoming increasingly sophisticated, organizations face a growing need for robust cybersecurity measures to safeguard their digital assets. Network forensics emerges as a crucial component in the cybersecurity toolkit, providing a systematic approach to investigating and resolving cyber incidents. This article delves into the world of network forensics, exploring its methodologies, tools, and its pivotal role in unraveling cyber incidents for effective resolution.
1. The Art and Science of Network Forensics
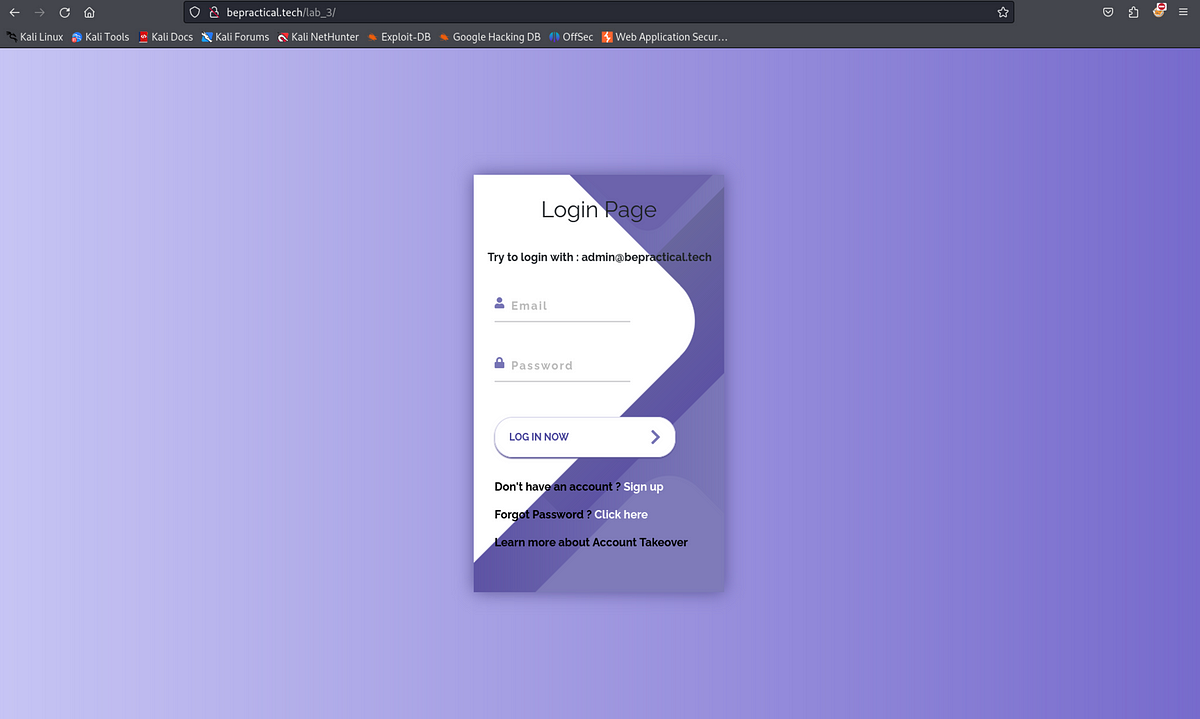
Introduce the concept of network forensics, outlining its role as both an art and a science. Discuss how it combines technological expertise with investigative skills to analyze and reconstruct cyber incidents.
2. Methodologies in Network Forensics A Step-by-Step Approach
Explore the systematic methodologies employed in network forensics. Discuss the step-by-step process, from evidence collection to analysis and reporting, emphasizing the importance of maintaining the integrity of digital evidence.
3. Real-Time Incident Response The Power of Immediate Action
Discuss the significance of real-time incident response in network forensics. Explore how organizations can leverage immediate actions to mitigate ongoing threats, minimize damage, and preserve evidence for subsequent analysis.
4. Network Forensics vs. Traditional Forensics Adapting to Digital Landscapes
Compare network forensics with traditional forensics methodologies. Highlight the unique challenges posed by digital environments and how network forensics addresses these challenges to uncover cyber threats.
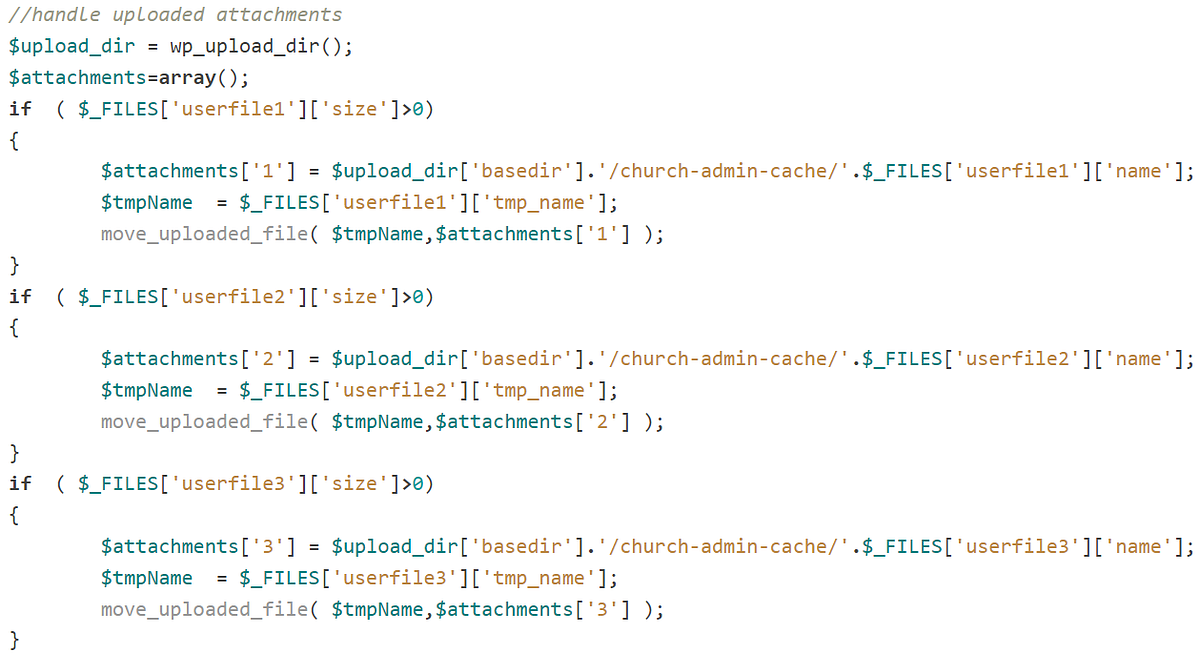
5. Tools of the Trade Network Forensics Solutions
Explore the various tools and technologies employed in network forensics. Discuss popular tools used for traffic analysis, packet capture, log analysis, and other forensic activities, emphasizing their role in uncovering cyber incidents.
.png)
 4 months ago
76
4 months ago
76 












 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·