Cybersecurity researchers on Thursday revealed details about a new Mirai-inspired botnet called "mirai_ptea" that leverages an undisclosed vulnerability in digital video recorders (DVR) provided by KGUARD to propagate and carry out distributed denial-of-service (DDoS) attacks.
Chinese security firm Netlab 360 pinned the first probe against the flaw on March 23, 2021, before it detected active exploitation attempts by the botnet on June 22, 2021.
The Mirai botnet, since emerging on the scene in 2016, has been linked to a string of large-scale DDoS attacks, including one against DNS service provider Dyn in October 2016, causing major internet platforms and services to remain inaccessible to users in Europe and North America.
Since then, numerous variants of Mirai have sprung up on the scene, in part due to the availability of its source code on the Internet. Mirai_ptea is no exception.
Not much has been disclosed about the security flaw in an attempt to prevent further exploitation, but the researchers said the KGUARD DVR firmware had vulnerable code prior to 2017 that enabled remote execution of system commands without authentication. At least approximately 3,000 devices exposed online are susceptible to the vulnerability.
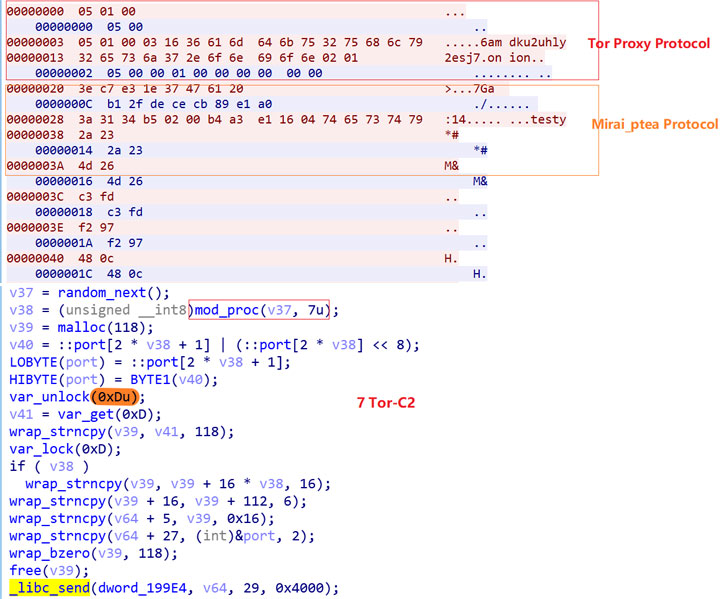
Besides using Tor Proxy to communicate with the command-and-control (C2) server, an analysis of the mirai_ptea sample revealed extensive encryption of all sensitive resource information, which is decoded to establish a connection with the C2 server and retrieve attack commands for execution, including launching DDoS attacks.
"The geographic distribution of bot source IPs is [...] mainly concentrated in the United States, Korea and Brazil," the researchers noted, with infections reported across Europe, Asia, Australia, North and South America, and parts of Africa.
Found this article interesting? Follow THN on Facebook, Twitter and LinkedIn to read more exclusive content we post.
.png)
 3 years ago
175
3 years ago
175 

















 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·