BOOK THIS SPACE FOR AD
ARTICLE AD
Security researchers have discovered a new piece of malware called SkinnyBoy that was used in spear-phishing campaigns attributed to Russian-speaking hacking group APT28.
The threat actor, also known as Fancy Bear, Sednit, Sofacy, Strontium, or PwnStorm, used SkinnyBoy in attacks targeting military and government institutions earlier this year.
Classic tactics, new tool
SkinnyBoy is intended for an intermediary stage of the attack, to collect information about the victim and to retrieve the next payload from the command and control (C2) server.
According to Cluster25 threat research company, APT28 likely started this campaign at the beginning of March, focusing on ministries of foreign affairs, embassies, defense industry, and the military sector.
Multiple victims are in the European Union but the researchers told BleepingComputer that the activity may have impacted organizations in the United States, too.
SkinnyBoy is delivered through a Microsoft Word document laced with a macro that extracts a DLL file acting as a malware downloader.
The lure is a message with a spoofed invitation to an international scientific event held in Spain at the end of July.
Opening the invitation triggers the infection chain, which starts with extracting a DLL that retrieves the SkinnyBoy dropper (tpd1.exe), a malicious file that downloads the main payload.
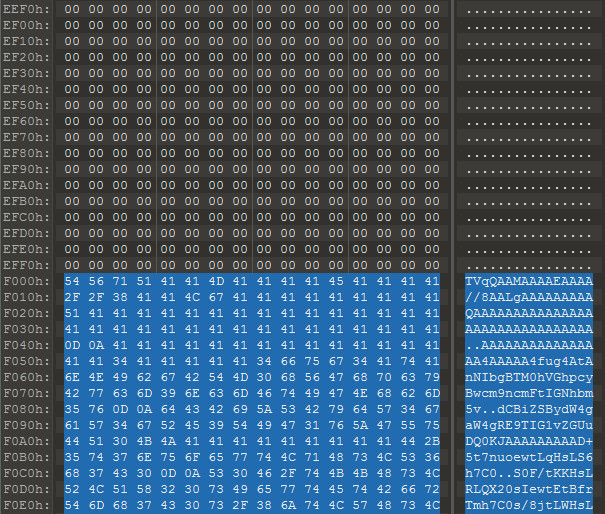
Once on the system, the dropper establishes persistence and moves to extract the next payload, which is encoded in Base64 format and appended as an overlay of the executable file.
This payload deletes itself after extracting two files on the compromised system:
C:\Users\%username%\AppData\Local\devtmrn.exe (2a652721243f29e82bdf57b565208c59937bbb6af4ab51e7b6ba7ed270ea6bce) C:\Users\%username%\AppData\Local\Microsoft\TerminalServerClient\TermSrvClt.dll (ae0bc3358fef0ca2a103e694aa556f55a3fed4e98ba57d16f5ae7ad4ad583698)To keep a low profile, the malware executes these files at a later stage, after creating a persistence mechanism via a LNK file under Windows Startup folder, Cluster25 says in a report shared with BleepingComputer.
The LNK file is triggered at the next reboot of the infected machine and looks for the main payload, SkinnyBoy (TermSrvClt.dll), by checking the SHA256 hashes of all the files under C:\Users\%username%\AppData\Local.
SkinnyBoy’s purpose is to exfiltrate information about the infected system, download, and launch the final payload of the attack, which remains unknown at the moment.
Collecting the data is done by using the systeminfo.exe and tasklist.Exe tools already present in Windows, which allow it to extract file names in specific locations:
C:\Users\%username%\Desktop C:\Program Files - C:\Program Files (x86) C:\Users\%username%\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Administrative Tools C:\Users\%username%\AppData\Roaming C:\Users\%username%\AppData\Roaming\Microsoft\Windows\Templates C:\Windows - C:\Users\user\AppData\Local\TempAll the information extracted this way is delivered to the C2 server in an organized fashion and encoded in base64 format.
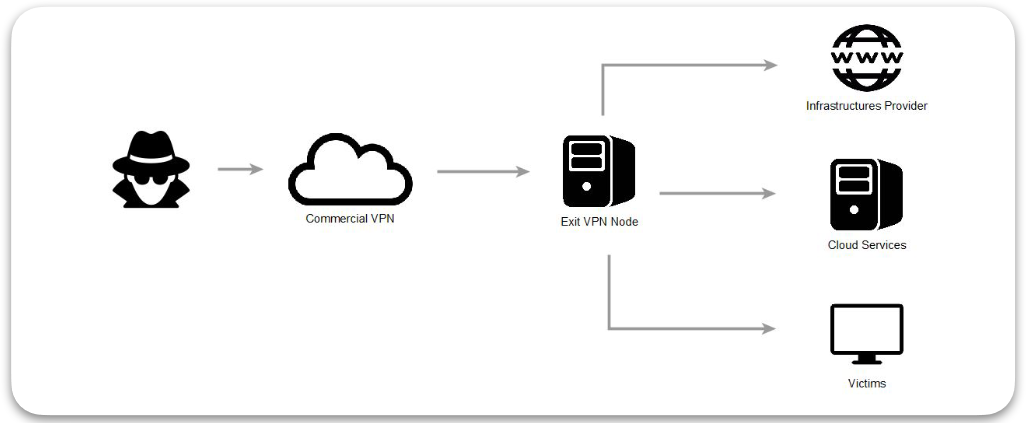
Cluster25 says that the attacker used commercial VPN services to purchase elements for their infrastructure, a tactic that adversaries typicall use to better lose their tracks.
After observing the tactics, techniques, and procedures, Cluster25 believes that the SkinnyBoy implant is a new tool from the Russian threat group known as APT28. The company has mid-to-high confidence in its attribution.
In the report today, Cluster25 provides YARA rules for all the tools examined by its researchers (SkinnyBoy dropper, launcher, and the payload itself) as well as a list of observed indicators of compromise that can help organizations detect the presence of the new malware.
.png)













 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·