BOOK THIS SPACE FOR AD
ARTICLE ADA novel form of phishing takes advantage of a disparity between how browsers and email inboxes read web domains.
Researchers have identified a never-before-seen method for sneaking malicious links into email inboxes.
The clever trick takes advantage of a key difference in how email inboxes and browsers read URLs, according a Monday report by Perception Point.
The attacker crafted an unusual link using an “@” symbol in the middle. Ordinary email security filters interpreted it as a comment, but browsers interpreted it as a legitimate web domain. Thus the phishing emails successfully bypassed security, but when targets clicked on the link inside, they were directed to a fake landing page nonetheless.
A Lame Phishing Attempt
On May 2, Perception Point’s incident response (IR) team flagged a hasily-designed phishing email trying to pass itself off as a Microsoft notice. “You have new 5 held messages,” it read, directing the recipient to follow a “Personal Portal” hyperlink.

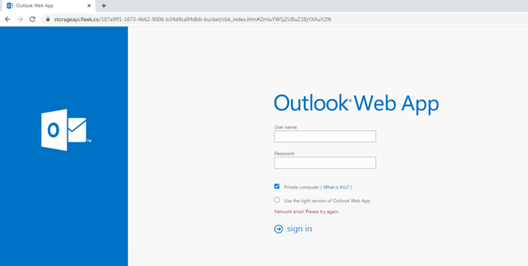
The link directed to a website masquerading as an Outlook login page. Again the hacker’s design choices were poor, and the domain name for this supposed Outlook page was, in fact, “storageapi.fleek.co,” followed by a long series of random characters.
In theory, if a user had overlooked all of these red flags, and submitted their Microsoft credentials, those credentials would’ve gone to the attacker.
So here’s the mystery: how did such a low-effort phishing attempt make it past email security filters, which are trained to spot much more sophisticated frauds than this?
The key was in the email link.
Some Background on Links
Pause here for a moment, and open up another webpage in your browser.
Type “https://” into your address bar, then any string of characters you want. Next, type an @ symbol, followed by any web domain. For example:
https[://]abc123@www[.]threatpost.com
Depending on what browser you’re using, that text before the @ will either return an error message, or disappear without a trace. Why?
Well, some browsers enable you to automatically send authentication information to the website you want to visit. The syntax is as follows:
http(s)://username[:]password[@]server/resource[.]ext
Browsers that support this feature will interpret the string before the @ sign as login credentials. Browsers that don’t will simply ignore the string and execute whatever follows the @. Either way, the domain following @ is where you’ll be going.
In January, Microsoft removed this feature from Internet Explorer because of how easily hackers can use it to mask malicious websites as legitimate ones. They explained how:
For example, the following URL appears to open http://www[.]wingtiptoys[.]com but actually opens http://example[.]com:
http://www[.]wingtiptoys[.]com@example[.]com
Which brings us to the crux of today’s news…
The Hacker’s Trick
The URL embedded in the phishing emails from our story was:
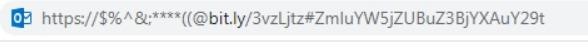
As we’ve established, browsers will read this as a URL. But email services read the @ symbol in the middle very differently.
“It is common knowledge that an @ sign will be ignored by email security systems when used within the text of an email, and there are many instances of this being used legitimately,” Motti Elloul, vice president of customer success and incident response at Perception Point, told Threatpost via email, “For example, it can be used to refer to user information within the body of the message.” For this reason, the IR team wrote in their report, “most email detection platforms cannot recognize this address as a URL, and instead see it as a comment.”
The @ symbol is a cover: to an email security filter it’s a comment, but underneath it’s a regular old malicious link.
The Impact
Our hacker – unknown but for an IP address 202[.]172.25[.]42, coming from Japan – went after “a wide range of targets, including telecom, web services and financial organizations,” said Elloul. None of their emails managed to trick any targets before they were discovered.
Despite the failure of this particular campaign, Elloul told Threatpost, “the technique has the potential to catch on quickly, because it’s very easy to execute.” As a proof of concept, at least, it proved rather effective.
“In order to identify the technique and avoid the fallout from it slipping past security systems, security teams need to update their detection engines in order to double check the URL structure whenever @ is included.”
.png)
















 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·