The U.S. National Security Agency (NSA) on Thursday released guidance to help organizations detect and prevent infections of a Unified Extensible Firmware Interface (UEFI) bootkit called BlackLotus.
To that end, the agency is recommending that "infrastructure owners take action by hardening user executable policies and monitoring the integrity of the boot partition."
BlackLotus is an advanced crimeware solution that was first spotlighted in October 2022 by Kaspersky. A UEFI bootkit capable of bypassing Windows Secure Boot protections, samples of the malware have since emerged in the wild.
This is accomplished by taking advantage of a known Windows flaw called Baton Drop (CVE-2022-21894, CVSS score: 4.4) discovered in vulnerable boot loaders not added into the Secure Boot DBX revocation list. The vulnerability was addressed by Microsoft in January 2022.
This loophole could be exploited by threat actors to replace fully patched boot loaders with vulnerable versions and execute BlackLotus on compromised endpoints.
UEFI bootkits like BlackLotus grant a threat actor complete control over the operating system booting procedure, thereby making it possible to interfere with security mechanisms and deploy additional payloads with elevated privileges.
It's worth noting that BlackLotus is not a firmware threat, and instead hones in on the earliest software stage of the boot process to achieve persistence and evasion. There is no evidence that the malware targets Linux systems.
"UEFI bootkits may lose on stealthiness when compared to firmware implants [...] as bootkits are located on an easily accessible FAT32 disk partition," ESET researcher Martin Smolár said in an analysis of BlackLotus in March 2023.
"However, running as a bootloader gives them almost the same capabilities as firmware implants, but without having to overcome the multilevel SPI flash defenses, such as the BWE, BLE, and PRx protection bits, or the protections provided by hardware (like Intel Boot Guard).
Besides applying the May 2023 Patch Tuesday updates from Microsoft, which addressed a second Secure Boot bypass flaw (CVE-2023-24932, CVSS score: 6.7) exploited by BlackLotus, organizations are advised to carry out the following mitigation steps -
Update recovery media Configure defensive software to scrutinize changes to the EFI boot partition Monitor device integrity measurements and boot configuration for anomalous changes in the EFI boot partition Customize UEFI Secure Boot to block older, signed Windows boot loaders Remove the Microsoft Windows Production CA 2011 certificate on devices that exclusively boot LinuxMicrosoft, for its part, is taking a phased approach to completely close the attack vector. The fixes are expected to be generally available in the first quarter of 2024.
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.
.png)
 1 year ago
110
1 year ago
110 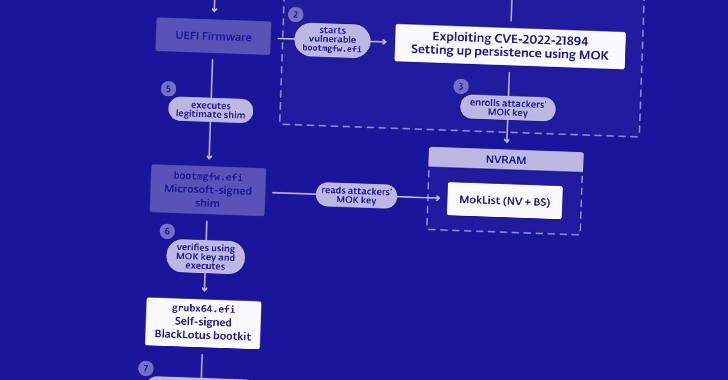
















 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·