A threat actor with suspected ties to Pakistan has been striking government and energy organizations in the South and Central Asia regions to deploy a remote access trojan on compromised Windows systems, according to new research.
"Most of the organizations that exhibited signs of compromise were in India, and a small number were in Afghanistan," Lumen's Black Lotus Labs said in a Tuesday analysis. "The potentially compromised victims aligned with the government and power utility verticals."
Some of the victims include a foreign government organization, a power transmission organization, and a power generation and transmission organization. The covert operation is said to have begun at least in January 2021.
The intrusions are notable for a number of reasons, not least because in addition to its highly-targeted nature, the tactics, techniques, and procedures (TTPs) adopted by the adversary rely on repurposed open-source code and the use of compromised domains in the same country as the targeted entity to host their malicious files.
At the same time, the group has been careful to hide their activity by modifying the registry keys, granting them the ability to maintain persistence on the target device without attracting attention surreptitiously.
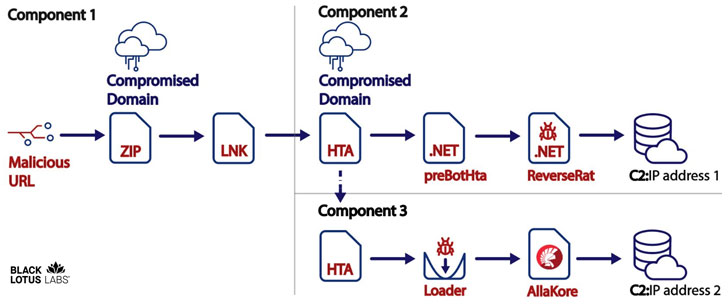
Explaining the multi-step infection chain, Lumen noted the campaign "resulted in the victim downloading two agents; one resided in-memory, while the second was side-loaded, granting threat actor persistence on the infected workstations."
The attack commences with a malicious link sent via phishing emails or messages that, when clicked, downloads a ZIP archive file containing a Microsoft shortcut file (.lnk) and a decoy PDF file from a compromised domain.
The shortcut file, besides displaying the benign document to the unsuspecting recipient, also takes care of stealthily fetching and running an HTA (HTML application) file from the same compromised website.
The lure documents largely describe events catering to India, disguising as a user manual for registering and booking an appointment for COVID-19 vaccine through the CoWIN online portal, while a few others masquerade as the Bombay Sappers, a regiment of the Corps of Engineers of the Indian Army.
Irrespective of the PDF document displayed to the victim, the HTA file — itself a JavaScript code based on a GitHub project called CactusTorch — is leveraged to inject a 32-bit shellcode into a running process to ultimately install a .NET backdoor called ReverseRat that runs the typical spyware gamut, with capabilities to capture screenshots, terminate processes, execute arbitrary executables, perform file operations, and upload data to a remote server.
The custom-developed framework also comes with a third component in which a second HTA file is downloaded from the same domain to deploy the open-source AllaKore remote agent, potentially in an alternative attempt to maintain access to the compromised network.
"While this threat actor's targets have thus far remained within the South and Central Asian regions, they have proven effective at gaining access to networks of interest," the researchers said. "Despite previously relying upon open-source frameworks such as AllaKore, the actor was able to remain effective and expand its capabilities with the development of the Svchostt agent and other components of the ReverseRat project."
Found this article interesting? Follow THN on Facebook, Twitter and LinkedIn to read more exclusive content we post.
.png)
 3 years ago
276
3 years ago
276 

















 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·