Proof-of-concept (PoC) exploit code has been made available for a recently disclosed and patched critical flaw impacting VMware Aria Operations for Networks (formerly vRealize Network Insight).
The flaw, tracked as CVE-2023-34039, is rated 9.8 out of a maximum of 10 for severity and has been described as a case of authentication bypass due to a lack of unique cryptographic key generation.
"A malicious actor with network access to Aria Operations for Networks could bypass SSH authentication to gain access to the Aria Operations for Networks CLI," VMware said earlier this week.
Summoning Team's Sina Kheirkhah, who published the PoC following an analyzing the patch by VMware, said the root cause can be traced back to a bash script containing a method named refresh_ssh_keys(), which is responsible for overwriting the current SSH keys for the support and ubuntu users in the authorized_keys file.
"There is SSH authentication in place; however, VMware forgot to regenerate the keys," Kheirkhah said. "VMware's Aria Operations for Networks had hard-coded its keys from version 6.0 to 6.10."

VMware's latest fixes also address CVE-2023-20890, an arbitrary file write vulnerability impacting Aria Operations for Networks that could be abused by an adversary with administrative access to write files to arbitrary locations and achieve remote code execution.
In other words, a threat actor could leverage the PoC to obtain admin access to the device and exploit CVE-2023-20890 to run arbitrary payloads, making it crucial that users apply the updates to secure against potential threats.
The release of the PoC coincides with the virtualization technology giant issuing fixes for an high-severity SAML token signature bypass flaw (CVE-2023-20900, CVSS score: 7.5) across several Windows and Linux versions of VMware Tools.
"A malicious actor with man-in-the-middle (MITM) network positioning in the virtual machine network may be able to bypass SAML token signature verification, to perform VMware Tools Guest Operations," the company said in an advisory released Thursday.
Peter Stöckli of GitHub Security Lab has been credited with reporting the flaw, which affects the following versions -
VMware Tools for Windows (12.x.x, 11.x.x, 10.3.x) - Fixed in 12.3.0 VMware Tools for Linux (10.3.x) - Fixed in 10.3.26 Open-source implementation of VMware Tools for Linux or open-vm-tools (12.x.x, 11.x.x, 10.3.x) - Fixed in 12.3.0 (to be distributed by Linux vendors)The development also comes as Fortinet FortiGuard Labs warned of continued exploitation of Adobe ColdFusion Vulnerabilities by threat actors to deploy cryptocurrency miners and hybrid bots such as Satan DDoS (aka Lucifer) and RudeMiner (aka SpreadMiner) that are capable of carrying out cryptojacking and distributed denial-of-service (DDoS) attacks.
Also deployed is a backdoor named BillGates (aka Setag), which is known for hijacking systems, stealing sensitive information, and initiating DDoS attacks.
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.
.png)
 1 year ago
86
1 year ago
86 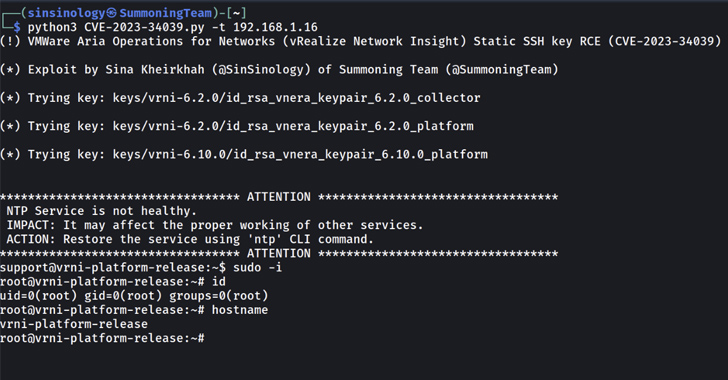















 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·