Enterprise applications used to live securely in data centers and office employees connected to internal networks using company-managed laptops or desktops. And data was encircled by a walled perimeter to keep everything safe.
All that changed in the last 18 months. Businesses and employees had to adapt quickly to cloud technology and remote work. The cloud gave businesses the agility to respond faster to change and the scale to accommodate rapid growth. Remote work boosted productivity by letting employees access cloud data from anywhere on any device.
This is not business as usual. The data center and the perimeter security are no longer the center of the universe. Now remote workers, personal mobile devices, applications, and data are in the middle.
Although employees, applications, and data have left the building, IT security teams still shoulder the responsibility for protecting confidential data and ensuring compliance with strict privacy regulations. The risk of not doing so can be costly.
Register for this upcoming webinar to learn how to reduce risk with integrated endpoint-to-cloud security.
Data security and access turned upside down
It's impossible to see risk when you don't know what you're up against. Employees now access data in your cloud from everywhere using personal devices and local Wi-Fi networks you can't see or manage. Whatever visibility you had is gone. Left unresolved, little – if anything – is under your control.
Currently, security from endpoints to the cloud involves multiple standalone tools that solve specific problems. But beware: Sometimes, juggling dozens of security tools –each unaware that the other exists – increases the risk of exposure.
Some organizations rely on virtual private networks (VPNs for remote workforce access. While they connect employees to cloud applications and data from anywhere, VPNs can assume every user and device is trustworthy (they are not). So, use caution with VPNs. They can leave your infrastructure and everything connected to it extremely vulnerable.
Mired in the momentum of mediocrity, the traditional security approach only offers a fraction of what's needed to ensure endpoint-to-cloud security. It doesn't give you visibility or insight into the security posture of your users and endpoints or cloud applications. And it can't enforce zero trust, a staple of modern security.
Minimize business risk
With data going where it's needed, organizations can minimize risk by regaining the same visibility, insights, and access controls they had with a perimeter. To do so, you need a cloud-delivered solution that provides strong data and privacy protections from endpoints to the cloud.
Lookout recommends considering these three factors to minimize risk:
Complete visibility –The first step to securing your data is knowing what's going on. This requires visibility into the risk levels of users, devices, applications, and data. Visibility also plays a key role in ensuring compliance with data privacy regulations. Unified insights –Your security infrastructure should be integrated into one unified platform to manage policies, detect cyberthreats and perform conclusive incident investigations. This will give you actionable insights from endpoints to the cloud. Secure access to empower productivity – To protect data without impeding productivity, it's critical to enforce Zero rust access that has the intelligence to understand and adapt to continuous changes in users, devices, locations, applications, and data.Data protection from endpoint to cloud
To achieve endpoint-to-cloud visibility, insights, and access control, organizations require perimeter-like security capabilities delivered from the cloud. In 2019, Gartner introduced the Secure Access Service Edge (SASE), a framework that addresses these challenges and calls for rolling multiple security solutions into one unified architecture.
Since then, throngs of vendors have integrated various security tools into their SASE products. Some offer cloud security but no endpoint security or continuous risk assessment. Others have basic access controls but don't analyze user behaviors, detect malware on the fly or identify compliance gaps. And many don't include advanced data protections that encrypt confidential data, emails, or files and enforce strict data-sharing rules.
Every vendor's interpretation of SASE should be carefully vetted to ensure that they integrate and adequately address every critical aspect of how your organization now operates with remote or hybrid work permanently in place. This modern security approach, with SASE and Zero Trust as cornerstones, will protect data from endpoints to the cloud by providing all-important visibility into devices, users, networks, access privileges, and cloud applications.
Register for this upcoming webinar to learn how Lookout delivers comprehensive endpoint-to-cloud security from one unified platform.
Found this article interesting? Follow THN on Facebook, Twitter and LinkedIn to read more exclusive content we post.
.png)
 3 years ago
172
3 years ago
172 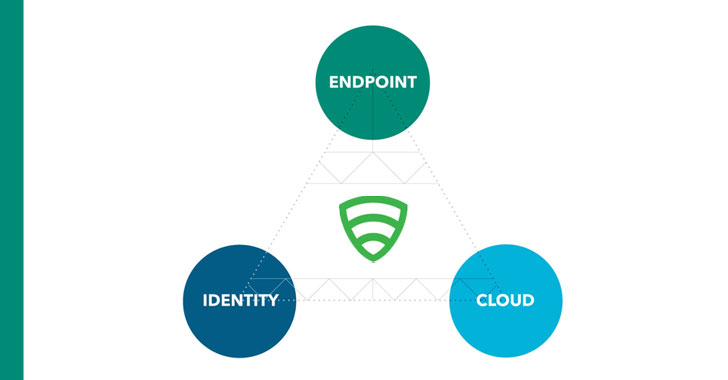















 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·