Details have emerged about a previously undocumented malware campaign undertaken by the Iranian MuddyWater advanced persistent threat (APT) group targeting Turkish private organizations and governmental institutions.
"This campaign utilizes malicious PDFs, XLS files and Windows executables to deploy malicious PowerShell-based downloaders acting as initial footholds into the target's enterprise," Cisco Talos researchers Asheer Malhotra and Vitor Ventura said in a newly published report.
The development comes as the U.S. Cyber Command, earlier this month, linked the APT to the Iranian Ministry of Intelligence and Security (MOIS).
The intrusions, which are believed to have been operational as recently as November 2021, were directed against Turkish government entities, including the Scientific and Technological Research Council of Turkey (TÜBİTAK), using weaponized Excel documents and PDF files hosted on attacker-controlled or media-sharing websites.
These maldocs masqueraded as legitimate documents from the Turkish Health and Interior Ministries, with the attacks starting by executing malicious macros embedded in them to propagate the infection chain and drop PowerShell scripts to the compromised system.
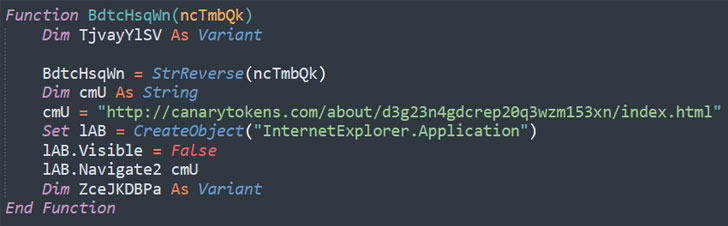
A new addition to the group's arsenal of tactics, techniques and procedures (TTPs) is the use of canary tokens in the macro code, a mechanism the researchers suspect is being used to track successful infection of targets, thwart analysis, and detect if the payload servers are being blocked at the other end.
Canary tokens, also known as honeytokens, are identifiers embedded in objects like documents, web pages and emails, which, when opened, triggers an alert in the form of an HTTP request, alerting the operator that the object was accessed.
The PowerShell script subsequently downloads and executes the next payload, also a PowerShell script that resides in the metadata of the maldoc, which, in turn, acts as the downloader for a third, unidentified PowerShell code that's ultimately run on the infected endpoint.
In a second variant of the attacks observed by Talos, the PDF documents with embedded links were found pointing to Windows executables instead of the Excel files, which then instrumented the infection chain to deploy the PowerShell downloaders.
What's more, the researchers said they found at least two different versions of the executable delivered by the adversary targeting the telecommunications sector in Armenia in June 2021 and Pakistani entities in August 2021, raising the possibility that MuddyWater may have engaged in multiple attacks as part of one long continuous campaign.
The disclosure also follows the release of a Private Industry Notification (PIN) by the U.S. Federal Bureau of Investigation (FBI) last week, detailing the malicious cyber activities of an Iran-based cyber company named Emennet Pasargad, which was tied to a sophisticated influence campaign orchestrated to interfere in the 2020 presidential elections.
"These actors are highly capable and motivated to perform their espionage activities," the researchers concluded. "With new techniques such as canary tokens used to track successful infection of targets, MuddyWater has proven their adaptability and unwillingness to refrain themselves from attacking other nations."
Found this article interesting? Follow THN on Facebook, Twitter and LinkedIn to read more exclusive content we post.
.png)
 2 years ago
171
2 years ago
171 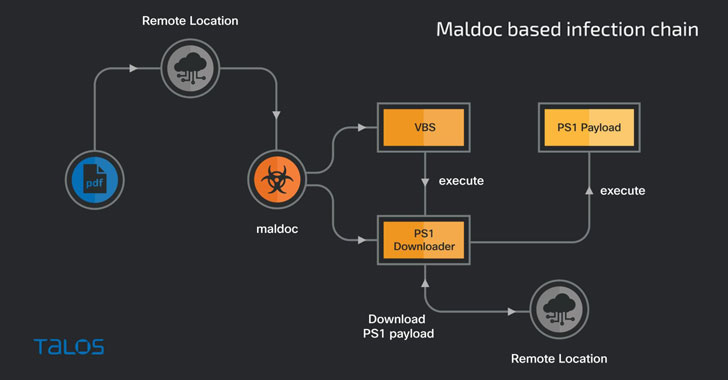

















 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·