BOOK THIS SPACE FOR AD
ARTICLE AD
The REvil ransomware gang is increasing the ransom demands for victims encrypted during Friday's Kaseya ransomware attack.
When conducting an attack against a business, ransomware gangs, such as REvil, typically research a victim by analyzing stolen and public data for financial information, cybersecurity insurance policies, and other information.
Using this information, the number of encrypted devices, and the amount of stolen data, the threat actors will come up with a high-ball ransom demand that they believe, after negotiations, the victim can afford to pay.
However, with Friday's attack on Kaseya VSA servers, REvil targeted the managed service providers and not their customers. Due to this, the threat actors could not determine how much of a ransom they should demand from the encrypted MSP customers.
As a solution, it seems the ransomware gang created a base ransom demand of $5 million for MSPs and a much smaller ransom of $44,999 for the MSP's customers who were encrypted.
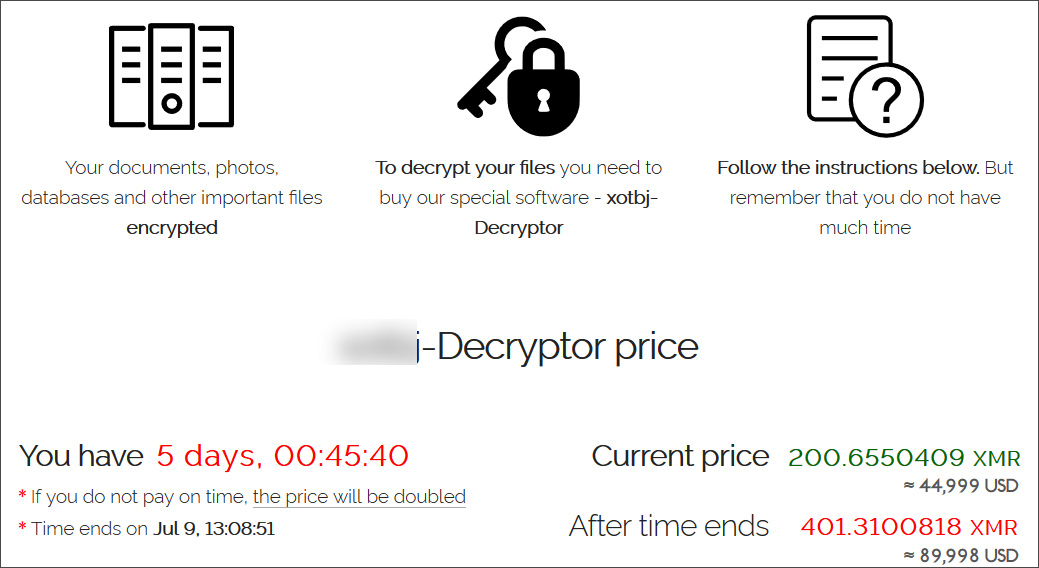 Ransom demand for Kaseya ransomware victims
Ransom demand for Kaseya ransomware victimsIt turns out this $44 thousand number is irrelevant as in numerous negotiation chats shared with and seen by BleepingComputer, the ransomware gang is not honoring these initial ransom demands.
When encrypting a victim's network, REvil can use multiple encrypted file extensions during the attack. The threat actors typically provide a decryptor that can decrypt all extensions on the network after a ransom is paid.
For victims of the Kaseya ransomware incident, REvil is doing things differently and demanding between $40,000 and $45,000 per individual encrypted file extension found on a victim's network.
 A portion of REvil ransom negotiation
A portion of REvil ransom negotiationFor one victim who stated they had over a dozen encrypted file extensions, the ransomware gang demanded a $500,000 ransom to decrypt the entire network.
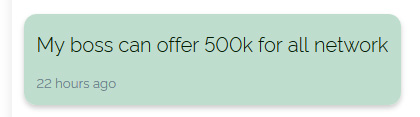 $500,000 ransom to decrypt the entire network
$500,000 ransom to decrypt the entire networkHowever, the good news is that the REvil representatives have told victims that they only encrypted networks, and nothing more. This means that REvil likely did not steal any of the victims' data, as they are known to use that as leverage in ransomware negotiations immediately.
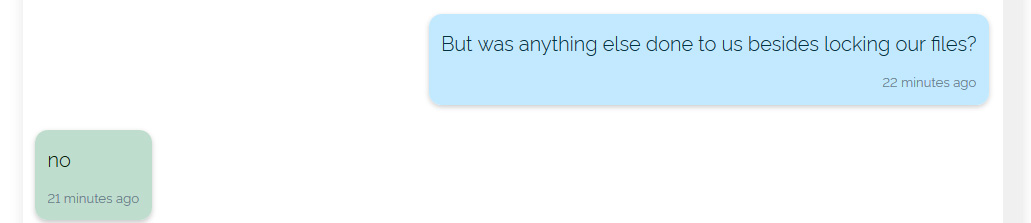 REvil indicates data was not stolen
REvil indicates data was not stolenThis also indicates that the ransomware operation did not access the victim's networks before the attack. Instead, they likely remotely exploited the Kaseya VSA vulnerability to distribute the encryptor and execute it on the victim's devices.
Attack's aftermath
Since the attacks on Friday, Kaseya has been working on releasing a patch for the zero-day vulnerability exploited in the REvil attack.
This zero-day was discovered by DIVD researchers who disclosed the t to Kaseya and helping test the patch.
Unfortunately, REvil found the vulnerability simultaneously and launched their attack on Friday before the patch was ready, just in time for the US Fourth of July holiday weekend.
It is believed that over 1,000 businesses have been affected by the attack, including attacks on the Swedish Coop supermarket chain, which had to close approximately 500 stores, a Swedish pharmacy chain, and the SJ transit system.
President Biden has directed US intelligence agencies to investigate the attack but has not gone as far to state that the attacks originated from Russia.
The FBI also announced today that they are investigating the incident and working closely with CISA and other agencies.
"The FBI is investigating the Kaseya ransomware incident and working closely with CISA and other interagency partners to understand the scope of the threat."
"If you believe your systems have been compromised, we encourage you to employ all recommended mitigations, follow Kaseya's guidance to shut down your VSA servers immediately and report to the FBI at ic3.gov," said the FBI in a press statement.
.png)














 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·