BOOK THIS SPACE FOR AD
ARTICLE AD
Russian cyberspies Gamaredon has been discovered using two Android spyware families named 'BoneSpy' and 'PlainGnome' to spy on and steal data from mobile devices.
According to Lookout, which discovered the two malware families, BoneSpy has been active since 2021, while PlainGnome emerged in 2024. Both target Russian-speaking individuals in former Soviet states.
Gamaredon (aka "Shuckworm") is believed to be part of Russia's Federal Security Agency (FSB), and its operations are closely tied to the country's national geopolitical interests.
Although the threat group has used various malware tools, BoneSpy and PlainGnome are the first documented cases of Gamaredon malware targeting mobile devices, specifically Android.
From open-source to custom malware
BoneSpy, typically delivered via trojanized Telegram apps or by impersonating Samsung Knox, was based on the open-source 'DroidWatcher' surveillance app, which dates back to 2013.
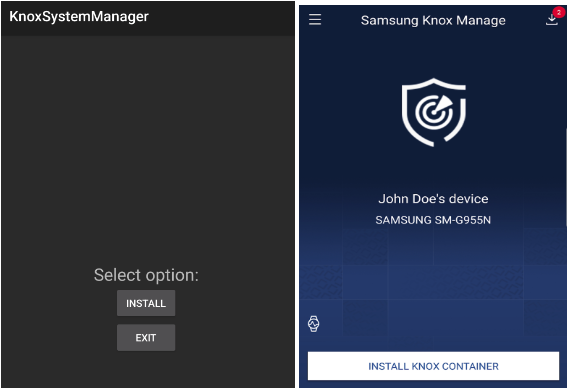 Impersonating the Samsung Knox Manager
Impersonating the Samsung Knox ManagerSource: BleepingComputer
Lookout says development work on BoneSpy peaked between January and October 2022, stabilizing to the following capabilities:
Collects SMS messages, including sender, content, and timestamps Records ambient audio and phone call conversations Captures GPS and cell-based location data Takes pictures using the camera and captures device screenshots Accesses user's web browsing history Extracts names, numbers, emails, and call details from the contact list and call logs Accesses clipboard content Reads device notificationsPlainGnome is a newer, custom Android surveillance malware that does not use the codebase of a previously known project. Lookout observed significant evolution in its code from January to October this year, indicating active development.
The new malware uses a two-stage installation process separating the dropper and payload, which makes it stealthier and more versatile.
PlainGnome features all the data collection capabilities of BoneSpy but also integrates advanced features like Jetpack WorkManager to exfiltrate data only when the device is idle, reducing detection risks.
The malware supports a recording mode that activates only when the device is idle and the screen is off to avoid tipping off victims through microphone activation indicators that they are being spied on.
Despite the increased sophistication in surveillance operations, Lookout notes that the spyware does not currently feature any form of code obfuscation, so analysis quickly revealed its true nature.
Upon launch, it requests the approval of dangerous permissions like access to SMS, contacts, call logs, and cameras. However, given its masking as a communication app, victims may be tricked into approving the request.
Lookout notes that neither BoneSpy nor PlainGnome were ever found on Google Play, so they're most likely downloaded from websites victims are directed to following social engineering. This approach matches Gamaredon's narrow targeting scope.
The researcher's report highlights Gamaredon's increasing focus on Android devices, showcasing the group's evolving tactics to expand its surveillance capabilities to mobile devices, which are increasingly used in all aspects of our lives and making them valuable targets.
.png)














 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·